Resources
What's New
Research Reports
White Papers + eBooks
Solution Briefs
Datasheets
Webinars
Videos
Learning Center
API Security
Application Security
Attack Surface
DRPS
Exposure Management
Vulnerability Assessment
Vulnerability Management
EASM 101
External Attack Surface Management
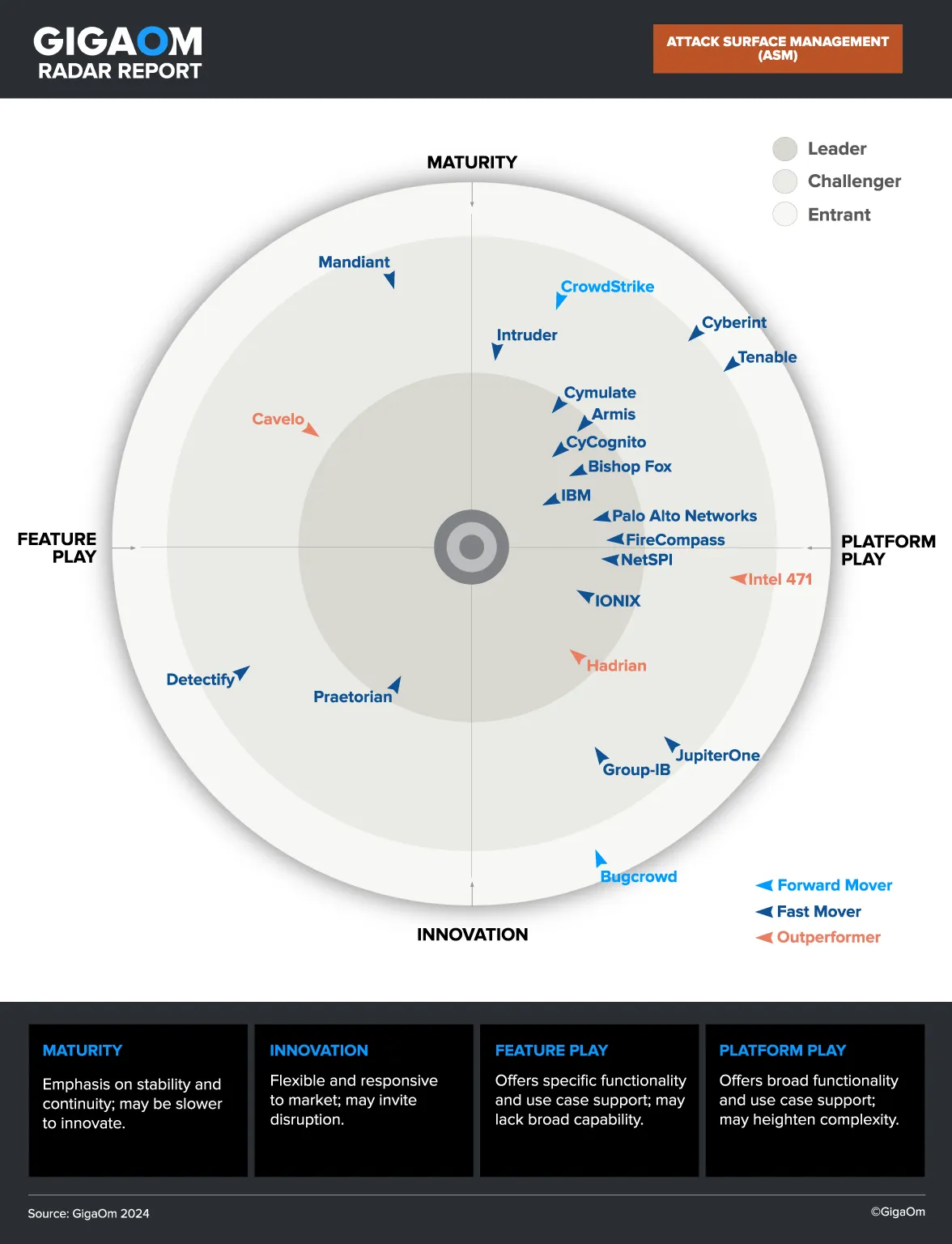
Attack Surface Management
Attack Surface Discovery
Attack Surface Protection
Attack Surface Reduction
Security & Compliance
Glossary
Blog