Frequently Asked Questions
Product Information
What is CyCognito and what does it do?
CyCognito is a cybersecurity platform that empowers organizations to take control of their external attack surface by autonomously discovering, testing, and prioritizing critical security risks. It simulates real-world attacks to identify exploitable and urgent issues across networks, web applications, cloud services, and APIs, helping companies act fast where it matters most. [Source]
What products and solutions does CyCognito offer?
CyCognito offers a range of products and solutions, including Attack Surface Management, Automated Security Testing, Exploit Intelligence, External Exposure Management (EASM), Continuous Security Testing (Autopt), Cyber Asset Inventory (CAASM), Vulnerability Management (UVM), Cloud Security (CNAPP), and Application Security (AppSec). Each solution is designed to address specific aspects of external risk and asset management. [Source]
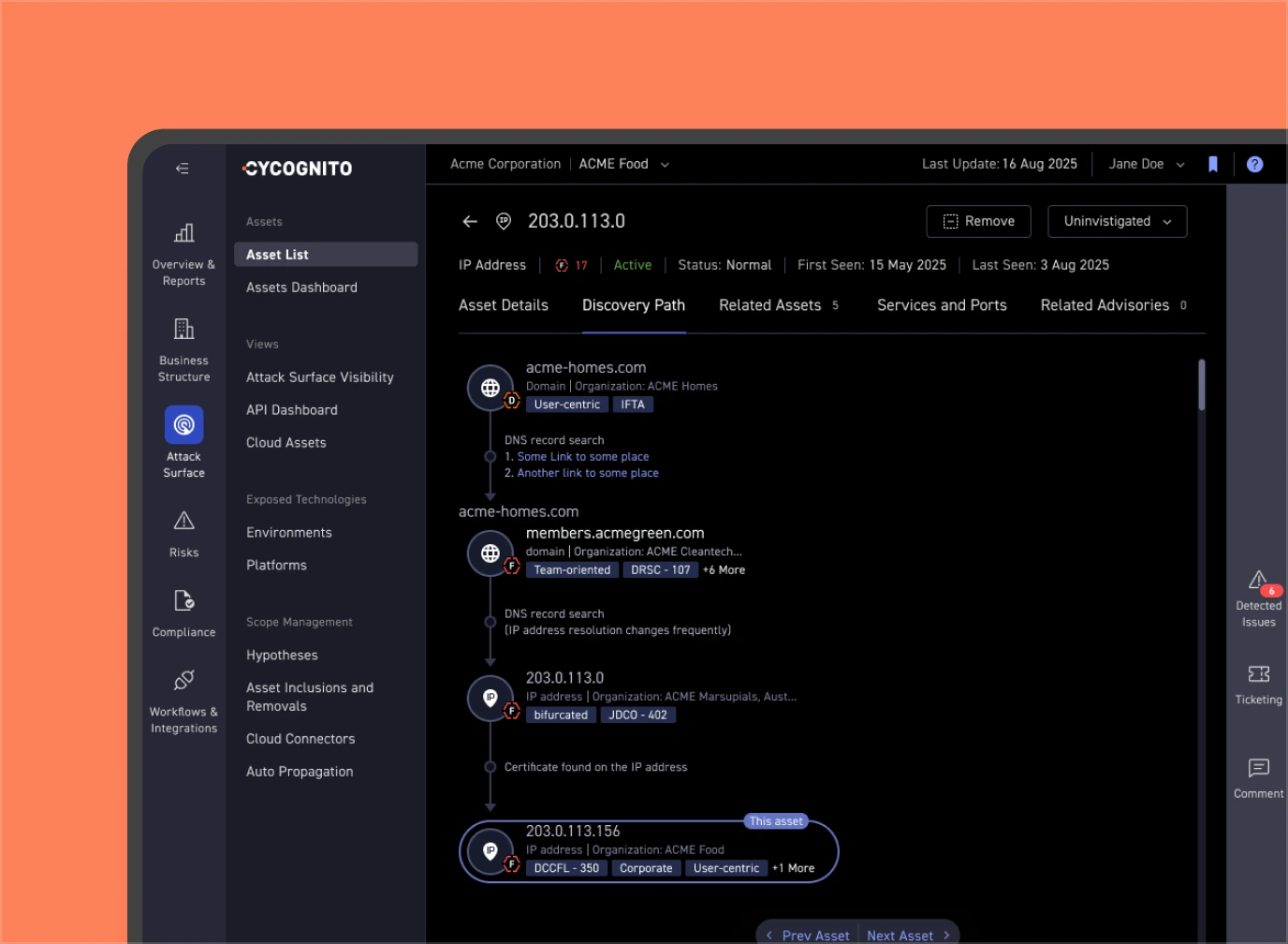
How does CyCognito discover and monitor external assets?
CyCognito uses seedless discovery to autonomously identify unknown or unmanaged assets, including shadow IT and forgotten services, without requiring manual input or asset lists. It maintains visibility with daily scans and continuous monitoring, ensuring up-to-date inventory and risk detection. [Source]
What is seedless discovery and why is it important?
Seedless discovery is CyCognito's autonomous approach to identifying assets without requiring asset lists or manual setup. This method uncovers up to 20× more exposures than traditional tools, providing comprehensive visibility into an organization's attack surface and eliminating blind spots. [Source]
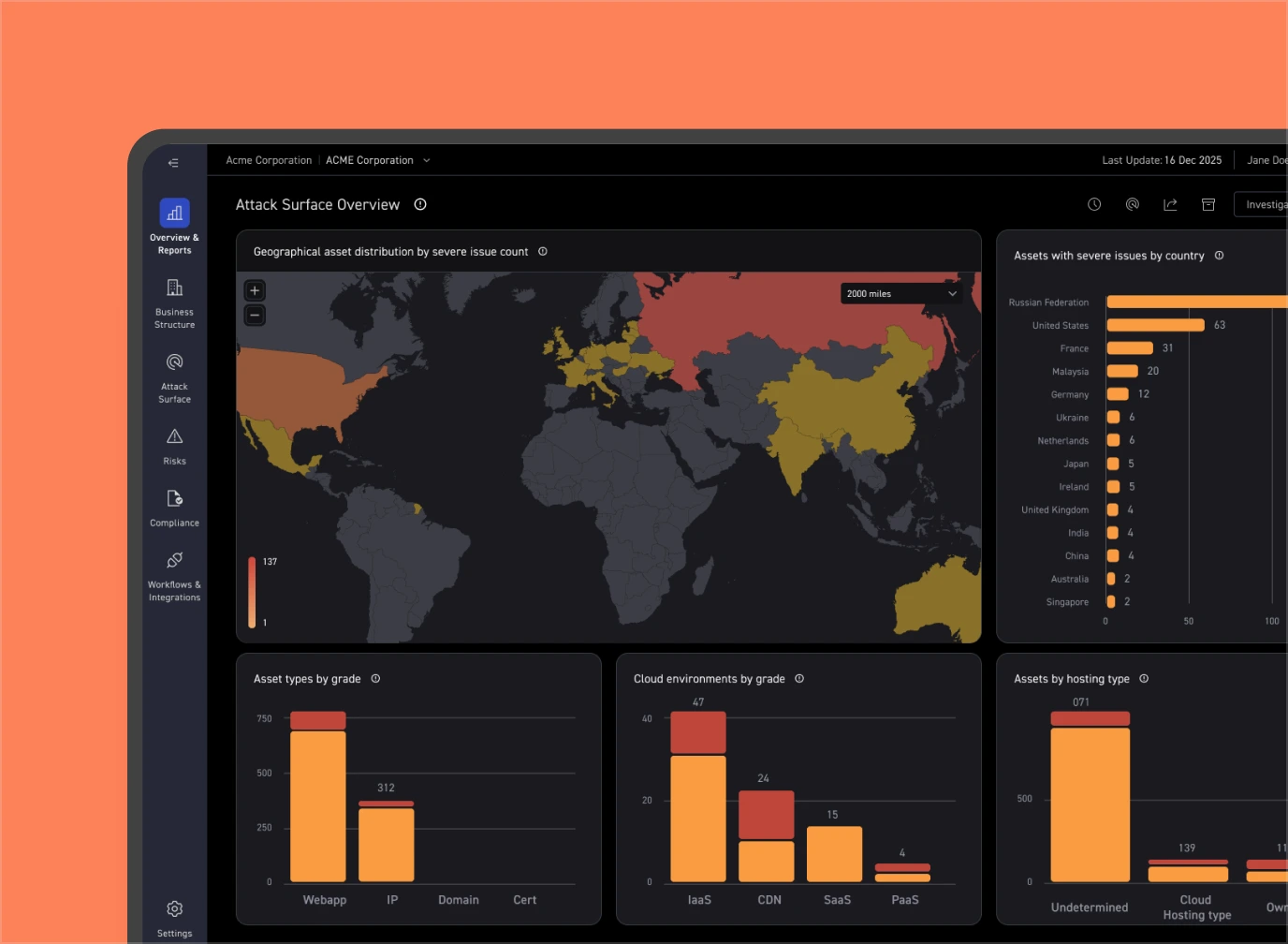
What types of assets and risks does CyCognito help identify?
CyCognito identifies a wide range of assets and risks, including untracked IP ranges, inherited and third-party assets, shadow IT, misconfigurations, unpatched software, and vulnerabilities in web applications, APIs, and cloud environments. [Source]
Features & Capabilities
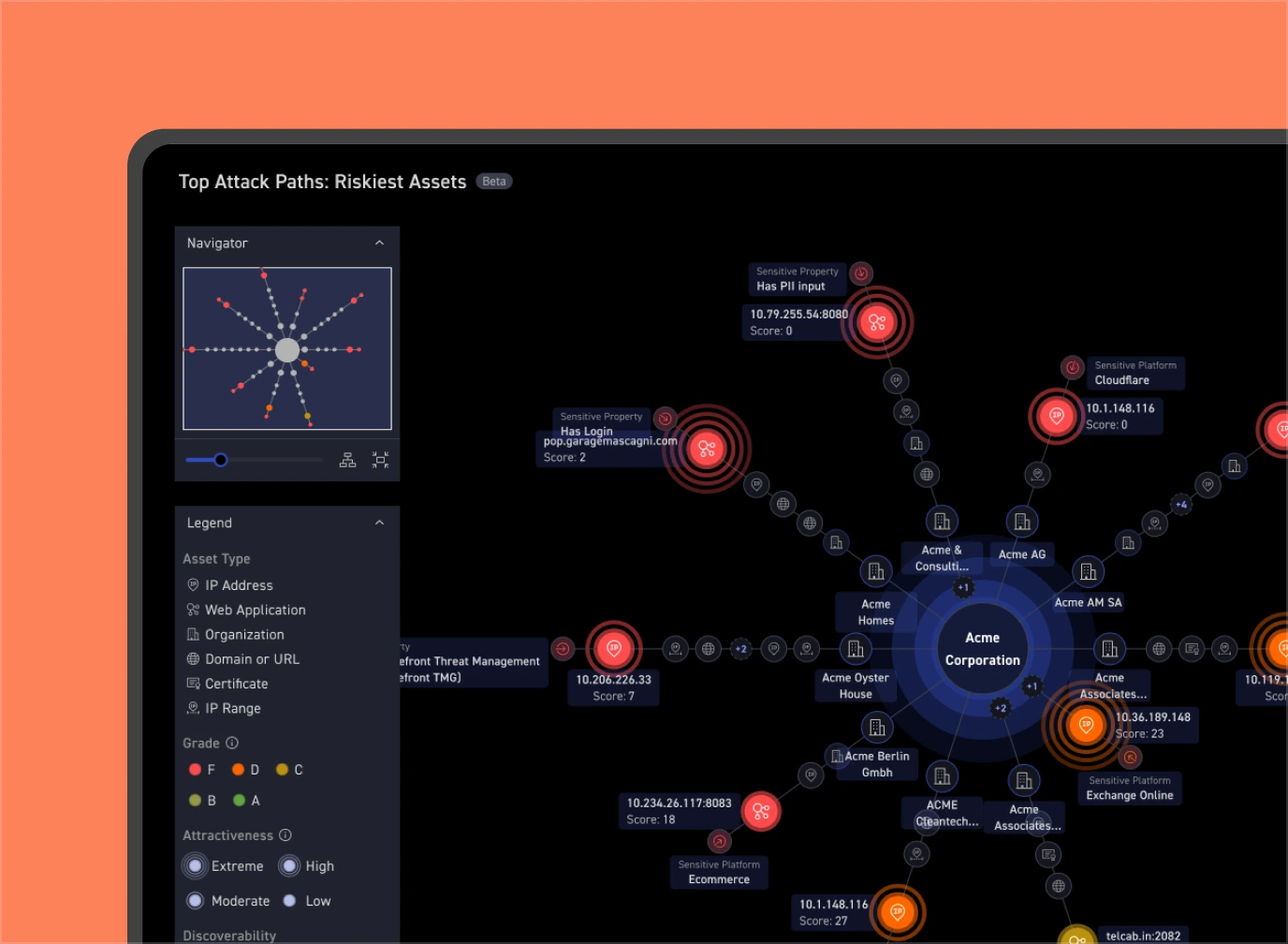
What are the key features of the CyCognito platform?
Key features include seedless discovery, risk-based prioritization, automation for scale, verified closure of security issues, comprehensive security management, and seamless integration with leading ticketing systems, SIEMs, and vulnerability management platforms. [Source]
Does CyCognito support automated security testing?
Yes, CyCognito offers automated security testing that continuously validates exploitability across your entire attack surface, helping organizations identify and remediate real risks efficiently. [Source]
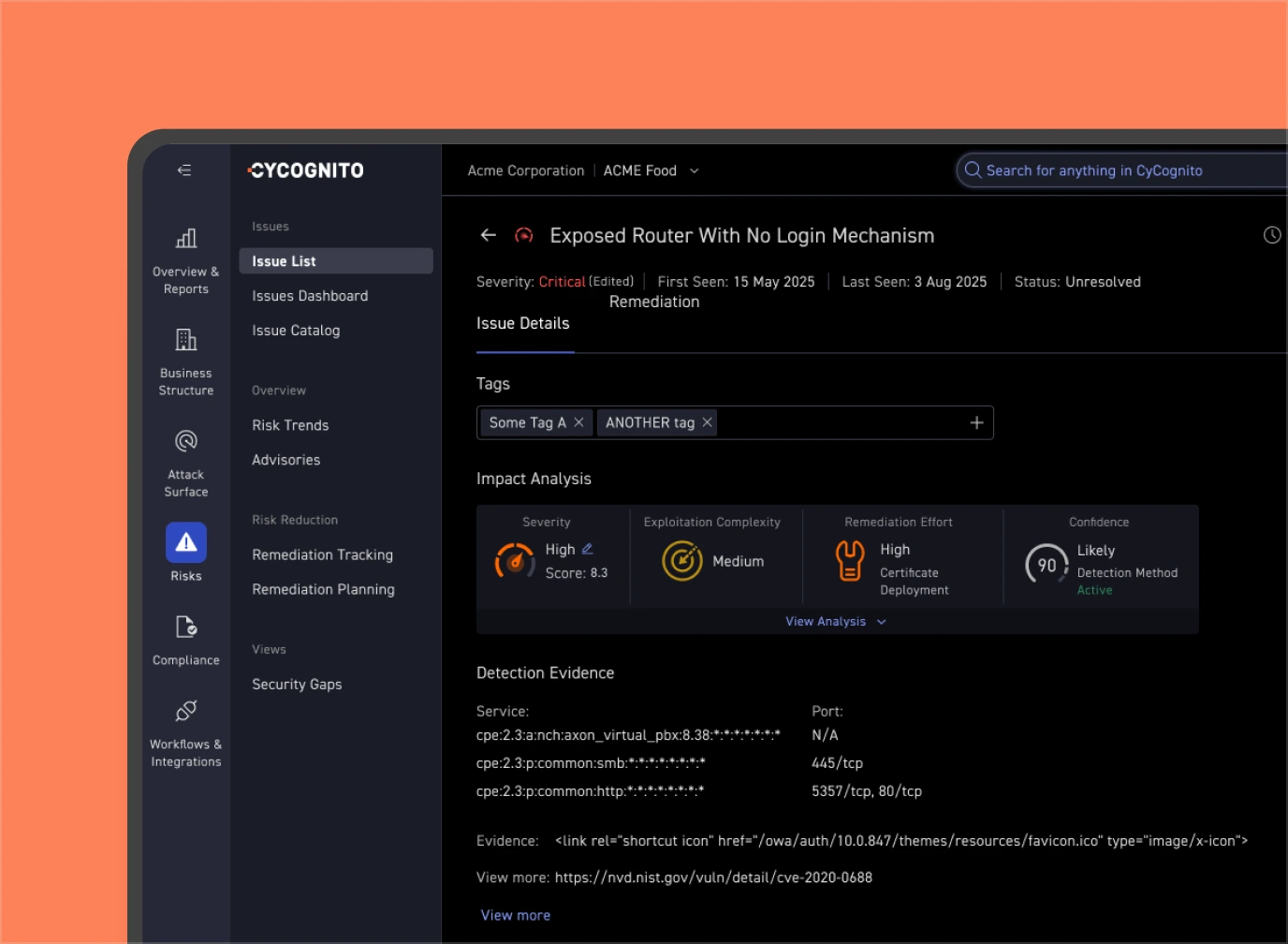
How does CyCognito prioritize vulnerabilities and risks?
CyCognito combines exploitability, business context, and attack-path insights to focus on the top 0.01% of risks, reducing noise and alert fatigue. This risk-based prioritization ensures that security teams address the most critical vulnerabilities first. [Source]
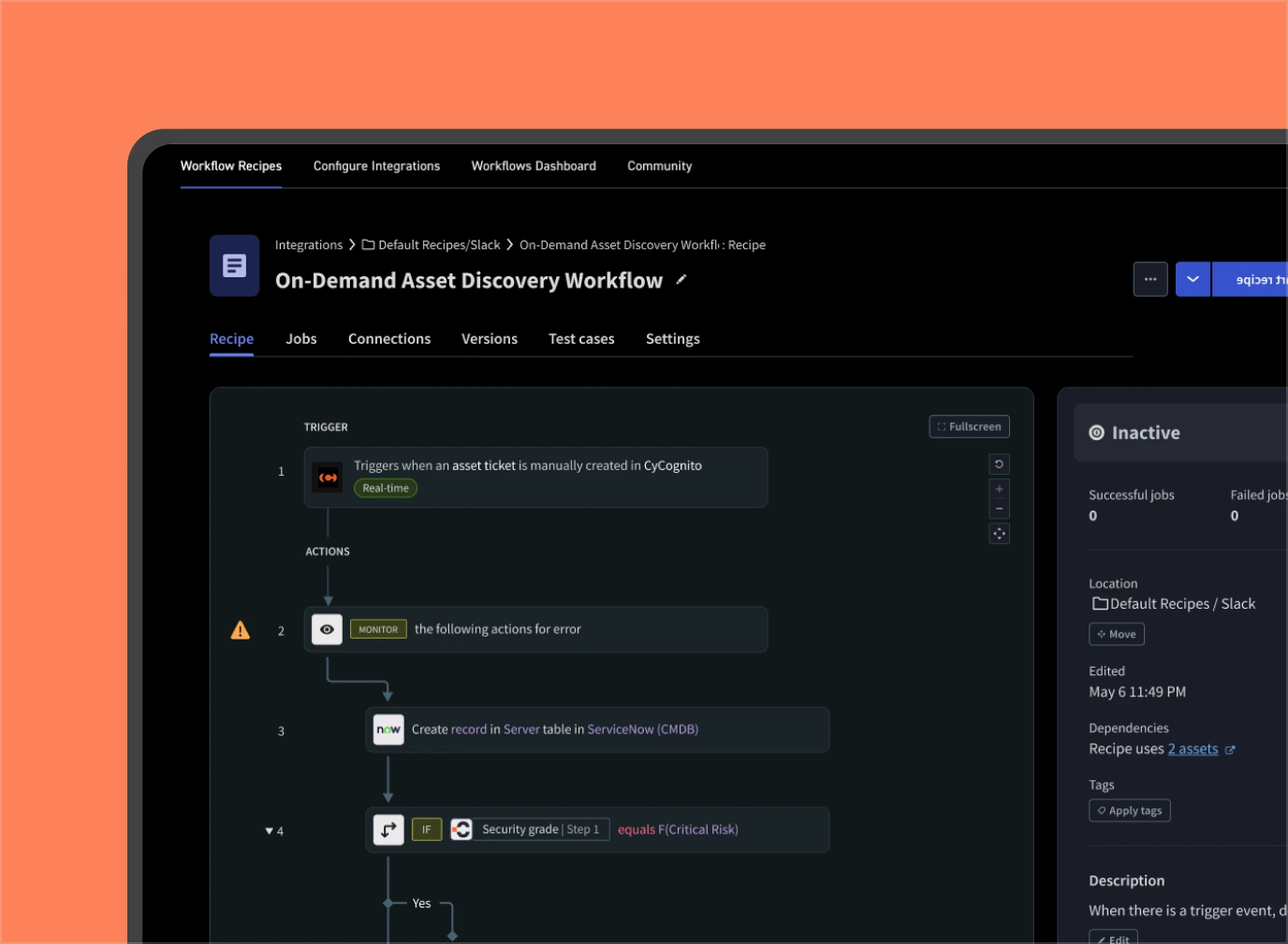
What integrations does CyCognito support?
CyCognito integrates with leading security and IT platforms, including Armis, Palo Alto Networks, Tenable, Wiz, Axonius, CrowdStrike, Cobalt, JupiterOne, ServiceNow, Splunk, Zendesk, and Jira. It supports automations in vulnerability management, incident management, asset management, SIEM/SOAR/XDR, cloud security, and ticketing solutions. [Source]
Does CyCognito provide technical documentation and resources?
Yes, CyCognito offers a comprehensive Knowledge Hub with datasheets and resources covering platform overview, automated security testing, discovery and contextualization, prioritization and remediation, exploit intelligence, vulnerability management, cloud connector, and more. [Source]
How does CyCognito verify remediation of security issues?
CyCognito periodically retests issues to ensure genuine remediation, addressing unresolved risks even after ticket closure. This helps organizations confirm that vulnerabilities have been effectively mitigated. [Source]
Is CyCognito easy to use for security teams?
Yes, CyCognito is consistently praised for its ease of use and intuitive platform design. Customers highlight its comprehensive yet user-friendly interface, making it accessible for security teams to manage and prioritize risks effectively. [Source]
How quickly can CyCognito be implemented?
CyCognito is designed for rapid deployment and minimal setup. It does not require agents or sensors and begins continuous discovery and validation immediately, allowing organizations to gain visibility and prioritize risks almost instantly. [Source]
What technical support and resources are available for CyCognito users?
CyCognito provides a Knowledge Center, a Support Portal, and a dedicated Customer Success Team to assist with implementation, best practices, and ongoing support. [Source]
Use Cases & Benefits
Who can benefit from using CyCognito?
CyCognito is ideal for IT security teams, CISOs, security operations teams, enterprises with complex infrastructures, government agencies, Fortune 500 companies, and organizations in industries such as education, media, gaming, hospitality, and healthcare. [Source]
What business impact can organizations expect from CyCognito?
Organizations can save up to $500,000 annually by reducing dependency on manual penetration testing and bug bounty programs. CyCognito also reduces critical findings from about 25% to 0.1%, streamlines workflows, and improves operational efficiency. [Source]
What pain points does CyCognito address for security teams?
CyCognito addresses challenges such as unknown or unmanaged assets, excessive alert noise, manual processes, scaling security operations, prioritizing risks, blind spots in attack surfaces, and verifying remediation of vulnerabilities. [Source]
Can you share specific case studies or success stories of CyCognito customers?
Yes, for example, Scientific Games used CyCognito to uncover hidden assets and obsolete devices, Ströer reduced alert fatigue, Berlitz identified 140 critical issues in a year, and a hospitality company detected and shut down rogue access. [Source]
Which industries are represented in CyCognito's case studies?
Industries include gaming, media, education, hospitality, and telecommunications, demonstrating CyCognito's versatility across different sectors. [Source]
Who are some of CyCognito's customers?
CyCognito is trusted by leading global enterprises such as Tesco, Colgate-Palmolive, Panasonic, Ströer, Hitachi, Storebrand, Bertelsmann, Wipro, Adama, Berlitz, Asklepios, Scientific Games, Agoda, Altice, and Sleep Number. [Source]
How does CyCognito help organizations reduce alert fatigue?
CyCognito reduces alert fatigue by focusing on validated risks and actionable threats, enabling security teams to concentrate on the most critical vulnerabilities and reducing noise from non-actionable alerts. [Source]
What is the impact of CyCognito on vulnerability management?
CyCognito enables organizations to prioritize vulnerabilities based on real risks, reducing critical findings from about 25% to 0.1% and allowing teams to focus on actionable threats. [Source]
How does CyCognito support compliance and audit preparation?
CyCognito supports compliance with frameworks such as ISO27001:2022, NIST 800-171 R2, PCI-DSS v4, and CIS CSC by automating evidence collection and mapping findings to relevant controls, simplifying audit preparation. [Source]
Security & Compliance
What security and compliance certifications does CyCognito have?
CyCognito holds SOC 2 Type II and ISO 27001 certifications, demonstrating robust security controls and adherence to stringent information security management practices. [Source]
How does CyCognito protect customer data?
CyCognito prioritizes protecting customer information through robust security controls, adherence to industry standards, and transparency via its Privacy, Compliance, and Trust Center. [Source]
Does CyCognito provide early warning of compliance violations?
Yes, CyCognito integrates with asset inventory and security testing workflows to provide actionable insights and early warning of compliance violations, simplifying remediation. [Source]
Where can I find more information about CyCognito's compliance and trust practices?
More information is available at CyCognito's Privacy, Compliance, and Trust Center, which provides transparency on data processing practices and access to security and compliance reports. [Source]
Competition & Comparison
How does CyCognito compare to Qualys?
CyCognito focuses on external attack surface management with autonomous, seedless discovery, uncovering up to 20× more exposures than Qualys, which primarily offers vulnerability management tools and requires manual input. [Source]
How does CyCognito compare to CrowdStrike Falcon Surface?
CyCognito uses autonomous, black-box pentesting with over 100,000 testing modules and prioritizes risks based on exploitability and business context, while CrowdStrike relies on passive scanning and lacks active testing results. [Source]
How does CyCognito compare to Tenable ASM?
CyCognito offers continuous outside-in discovery and automated validation, providing 20× more visibility and focusing on the top 0.01% of risks, while Tenable ASM relies on manual input and passive scanning. [Source]
How does CyCognito compare to Microsoft Defender EASM?
CyCognito autonomously discovers hidden assets and provides rapid vulnerability scanning, while Microsoft Defender EASM requires manual input and lacks comprehensive discovery. CyCognito also offers actionable insights and continuous monitoring. [Source]
How does CyCognito compare to Palo Alto Networks Cortex Xpanse?
CyCognito uses NLP, ML, and a graph data model for business mapping, providing 20× more visibility and automated pentesting with over 100,000 modules, while Cortex Xpanse relies on manual mapping and has limited testing and prioritization. [Source]
What makes CyCognito different from other attack surface management tools?
CyCognito stands out with seedless discovery, risk-based prioritization, automation for scale, verified closure of issues, and comprehensive integration capabilities. It eliminates the need for manual setup and uncovers significantly more exposures than traditional tools. [Source]
Why should a customer choose CyCognito over alternatives?
Customers should choose CyCognito for its autonomous asset discovery, risk-based prioritization, automation, verified remediation, comprehensive management, and proven business impact, including significant cost and time savings. [Source]