



CyCognito automatically enriches every discovered asset with business context, ownership, and in-the-wild threat signals, so security teams know not just what they own but what it means.
Get a Demo

Enhance your asset inventory with external context classified by business and technical purpose. Covers 3rd-party apps, exposed services, and potential PII exposure.

CyCognito maps in-the-wild exploit intelligence to your assets. Know what vulnerabilities are actively targeted, not just which CVEs apply in theory.

Every asset is traced to the right subsidiary, brand, or business unit. Evidence supports each relationship so teams act with confidence rather than assumption.

I can't point to another tool that does as thorough a job of exploring and exposing those assets that you didn't even know you had. It's so valuable.
 Colgate-Palmolive
Alex Schuchman ・ CISO
Colgate-Palmolive
Alex Schuchman ・ CISO
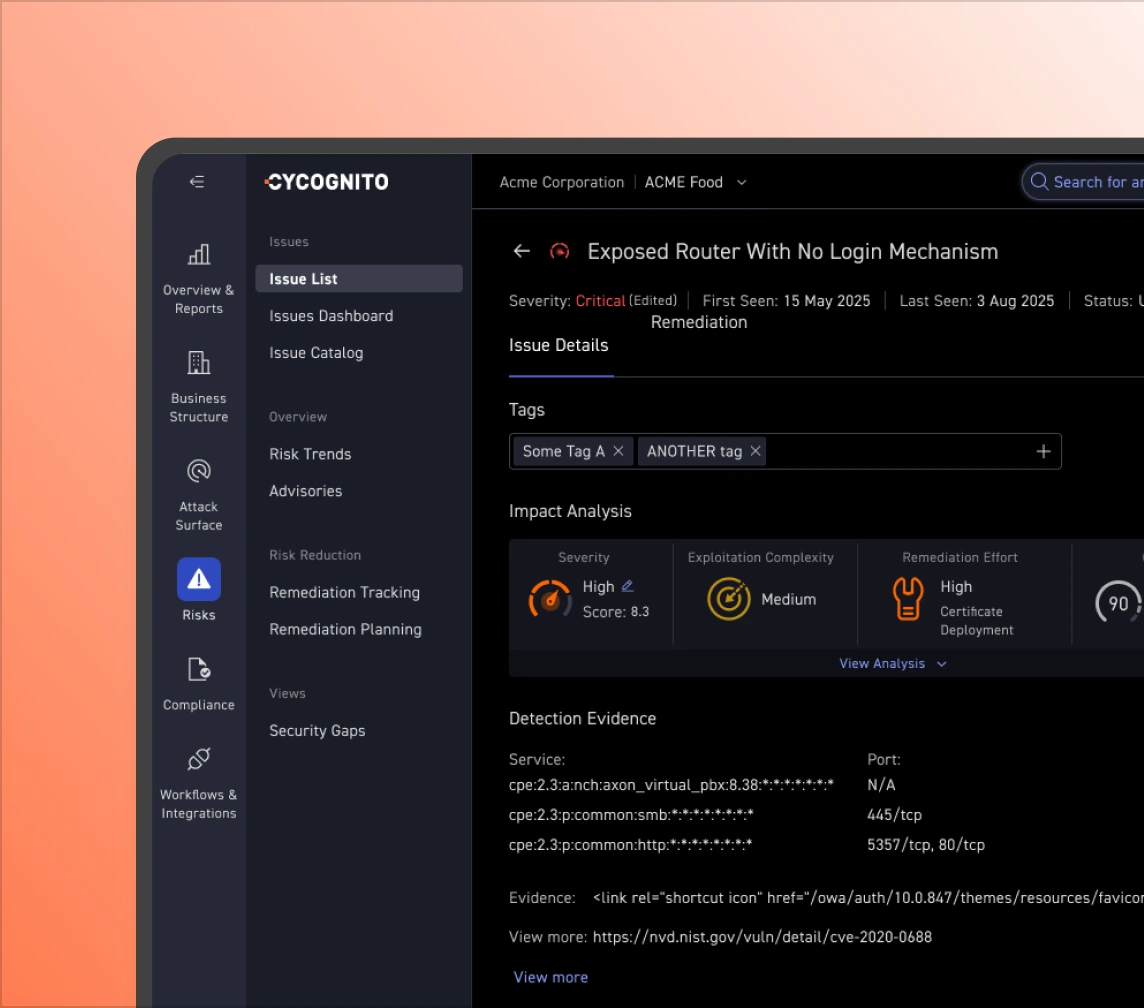
CyCognito captures what each asset does, what technology it runs, what data it handles, and how it connects to the broader environment. Business purpose, PII exposure, ecommerce functions all classified automatically, across every asset.

CyCognito calculates two proprietary scores per asset: Discoverability, how easy it is for an attacker to find it, and Attractiveness, how compelling it is to exploit. These scores reflect attacker decision-making, not generic severity formulas.
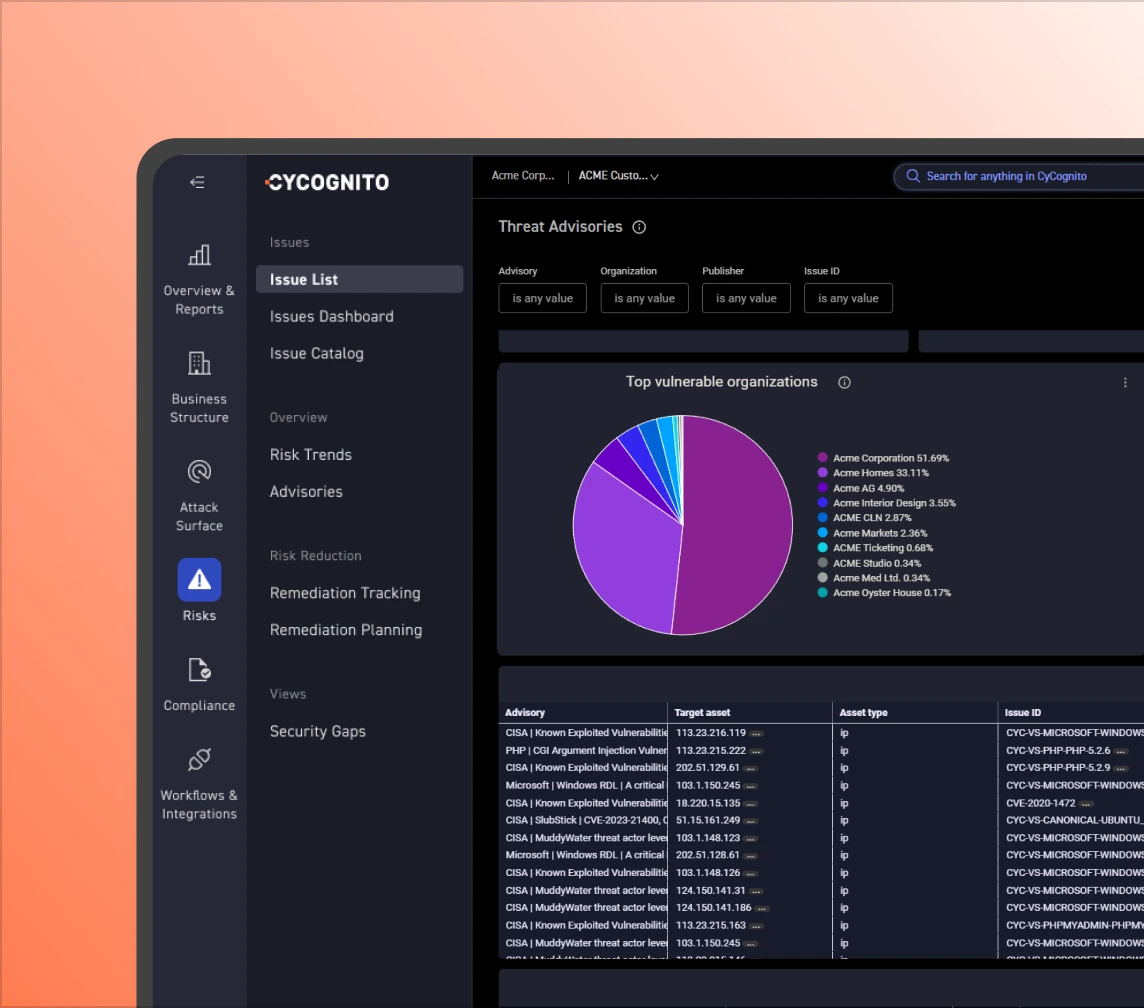
CyCognito ingests curated advisories on vulnerabilities actively exploited in the wild and tags which of your assets are afflicted. When a new threat emerges, you can answer the question your CISO will ask within minutes, not days.
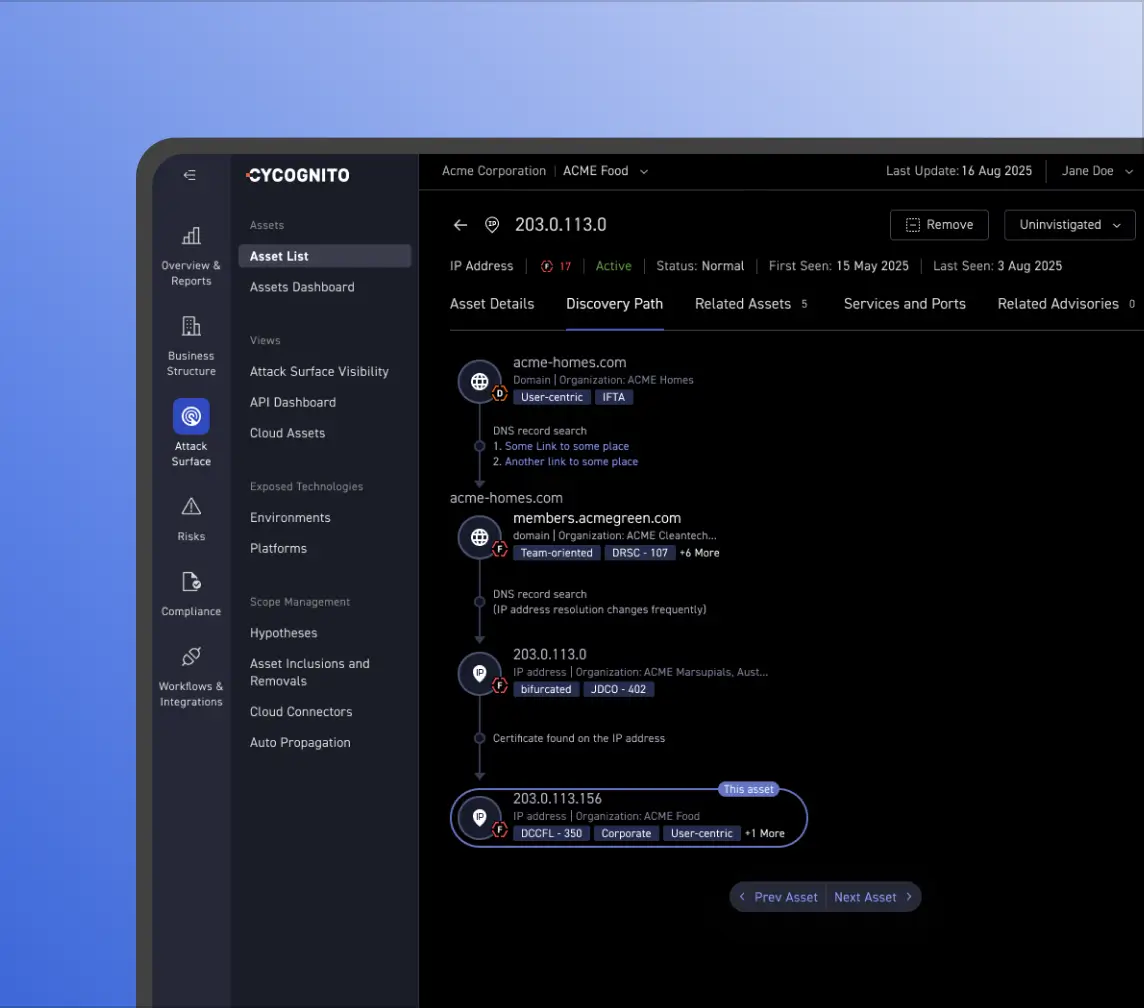
Ownership gaps slow every fix. CyCognito's proprietary attribution model connects each asset to the right team, subsidiary, or third-party relationship, with a full evidence chain so no one can dispute the assignment.