



Most organizations have 30% more external assets than they know about. CyCognito maps the full picture, with no seed data, no IP lists, and no manual setup.
Get a Demo

Starts from your organization's name. No IP ranges, no asset lists, no scoping needed. Runs continuously from day one.

Attacker-style reconnaissance running across 60,000 nodes. Continuous coverage across cloud, SaaS, APIs, on-prem, and third-party systems.

Every asset is automatically attributed to the right subsidiary, brand, or business unit. Graph-based analysis and evidence back every finding.

Every finding includes a full trace: how it was found, why it belongs to your org, and who owns it. Attribution disputes are resolved before they start.

CyCognito became a cornerstone of our security set-up by solving multiple pain points with automatic detection of assets, continously anaylzing for vulnerbilities and by providing an easy-to-use and comprehensive platform to manage these issues.
 Berlitz
Stefan Romberg ・ Global CISO
Berlitz
Stefan Romberg ・ Global CISO

Most breaches start from assets victims didn't know they owned. CyCognito's 60,000-node global network surfaces those assets continuously, with no seed data or input required.
New web applications, cloud deployments, acquired companies, and shadow IT constantly expand your attack surface. CyCognito keeps pace with those changes, so your team always works from a current inventory.
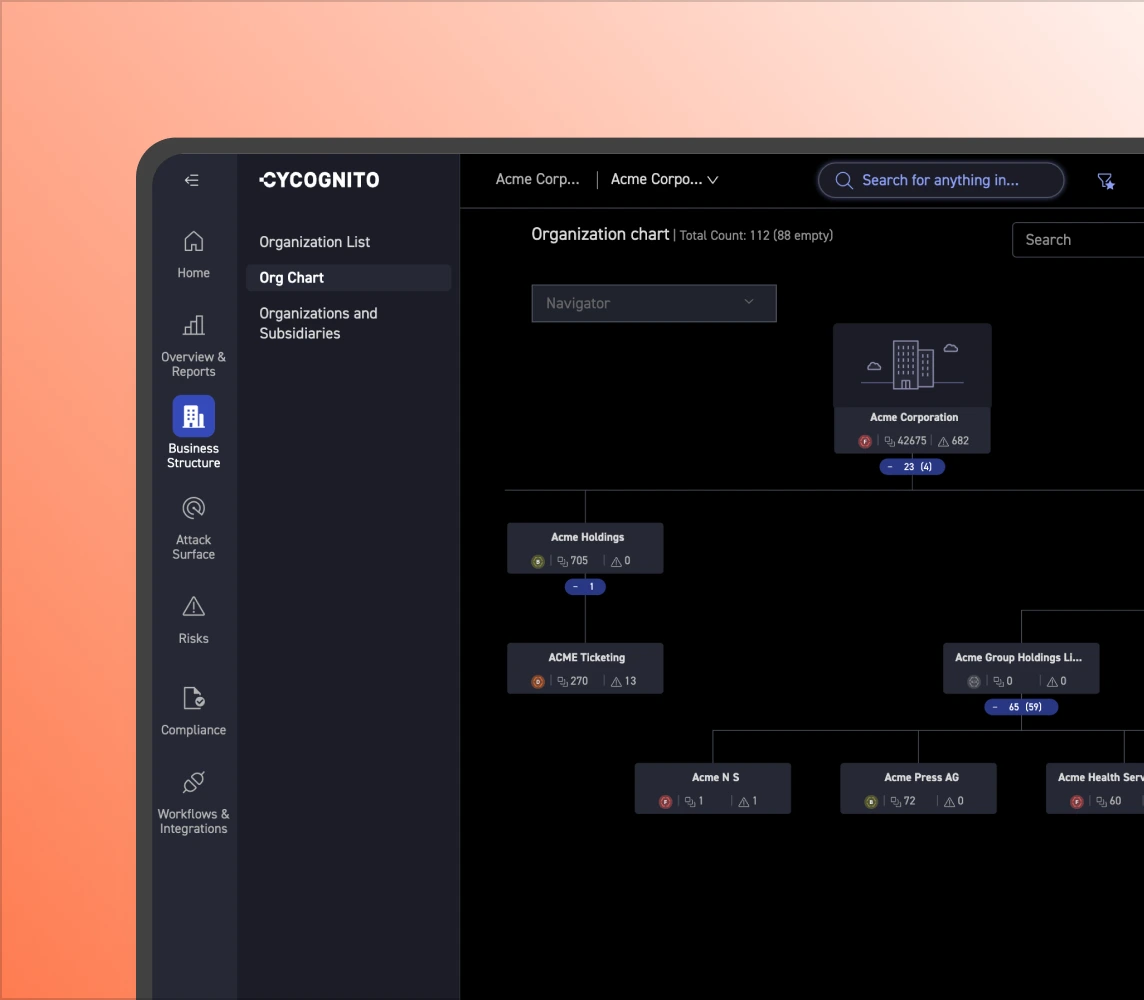
An asset with no owner never gets fixed. CyCognito's graph-based attribution connects every finding to the right subsidiary, business unit, or acquisition, with evidence attached to each.
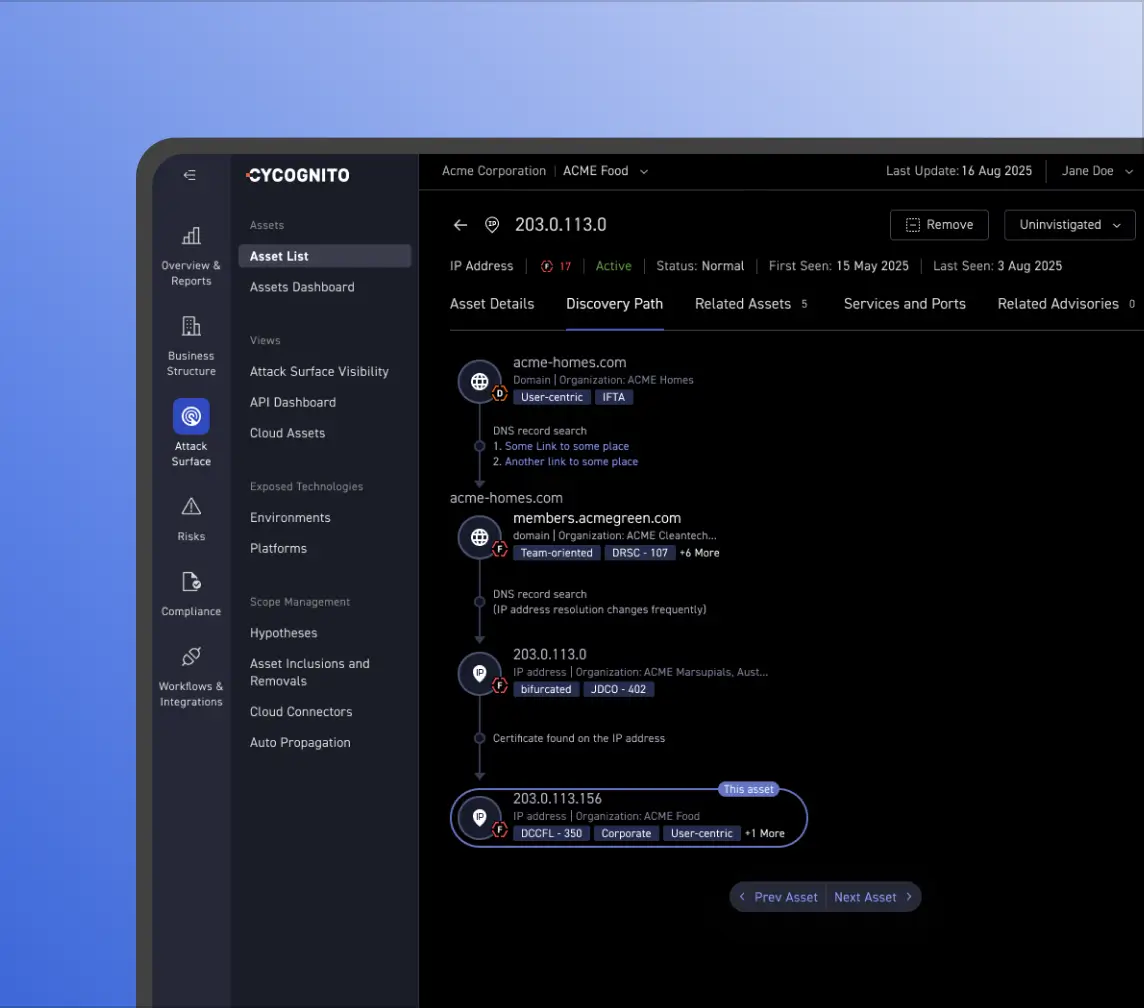
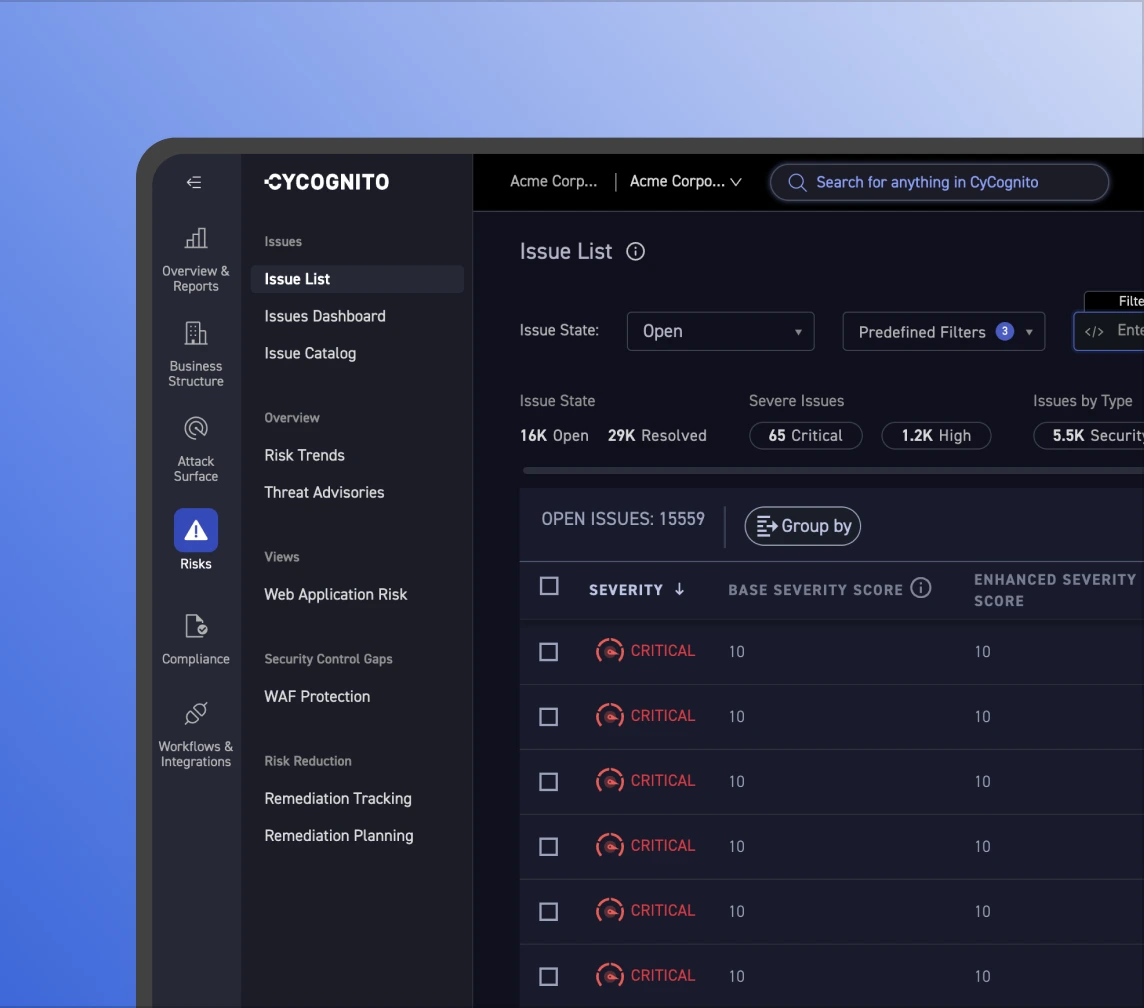
Unverified findings create friction. CyCognito backs every asset with a full evidence trail: how it was found, how it's attributed, and why it belongs to your org. Teams act without debate.