Knowledge Hub
Practical guides, research, and insights to help security teams manage external exposure with clarity and control.
Exposure Management
Shift from a reactive to proactive exposure management process using CyCognito’s attack surface management platform.
Read more about Exposure Management
Demystifying Continuous Threat Exposure Management (CTEM)
A technology checklist for implementing exposure management in your organization.
Read more about Demystifying Continuous Threat Exposure Management (CTEM)
Discover and Contextualize
Download this brief to learn about the common problems that exist today within asset discovery and contextualization and how CyCognito can be implemented as a solution.
Read more about Discover and Contextualize
Prioritize Risk and Accelerate Remediation
Learn about today's common problems within risk prioritization and remediation and how CyCognito can be implemented as a solution.
Read more about Prioritize Risk and Accelerate Remediation
Security Testing
Download this brief to learn about the challenge of testing at scale, how to stay ahead of your changing attack surface, and how you can best prioritize and remediate risk.
Read more about Security Testing
Scale Your Pen Test and Red Team Operations with CyCognito
Learn how your pen testing teams can reduce time spent on reconnaissance and active testing, effortlessly increase test cadence and coverage, and integrate pen testing data with prioritization and remediation workflows.
Read more about Scale Your Pen Test and Red Team Operations with CyCognito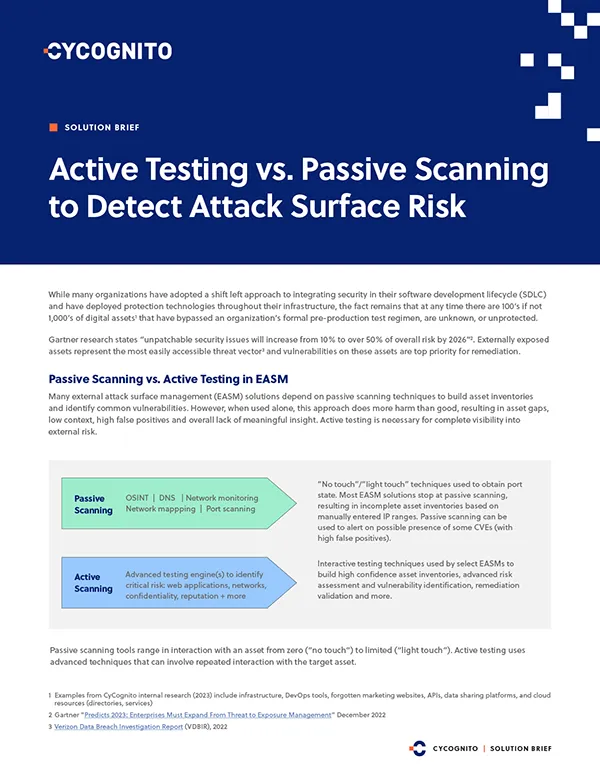
Active Testing vs. Passive Scanning to Detect Attack Surface Risk
Learn about the approaches, the challenges, the benefits, and how you can achieve continuous and comprehensive security testing across all of your external assets.
Read more about Active Testing vs. Passive Scanning to Detect Attack Surface Risk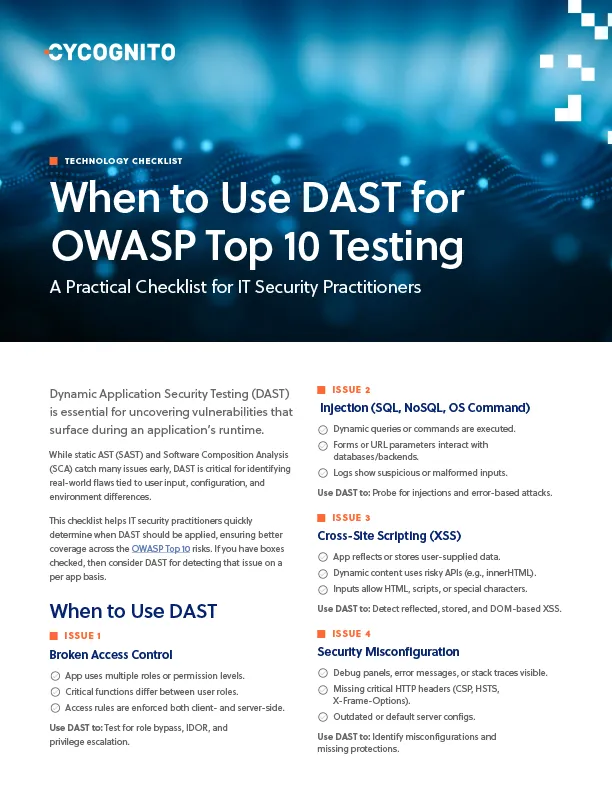
When to Use DAST for OWASP Top 10 Testing
Need a DAST reference card? This quick checklist shows you where it matters most across the OWASP Top 10. Built for hands-on security pros.
Read more about When to Use DAST for OWASP Top 10 Testing
The Path to Faster Fixes
Download our Faster Fixes Checklist and learn how security teams accelerate detection and remediation using fully automated active testing.
Read more about The Path to Faster Fixes
Top App Vulnerabilities Often Missed After Deployment
This cheat sheet reveals the 10 most common post-deployment issues that black box testing can uncover, no credentials or internal access required.
Read more about Top App Vulnerabilities Often Missed After Deployment
Five Cloud Security Metrics That Matter
Discover 5 cloud security KPIs that reveal real risk, improve response times, and help leadership track meaningful progress across your cloud estate.
Read more about Five Cloud Security Metrics That Matter
Five Common Gaps in CNAPP Coverage
Learn 5 critical CNAPP gaps and how to fix them. Improve cloud visibility, testing, and risk coverage with this practical cheat sheet.
Read more about Five Common Gaps in CNAPP Coverage
Closing the Production App Risk Gap – A Business Imperative
Learn how to manage application risk beyond deployment. Align controls across the SDLC to close production gaps and reduce real-world business risk.
Read more about Closing the Production App Risk Gap – A Business Imperative
CyCognito + Wiz
CyCognito strengthens Wiz’s cloud-native security with an outside-in perspective and active testing. Validated findings seamlessly integrate into DevSecOps workflows to streamline remediation across the attack surface.
Read more about CyCognito + Wiz
CyCognito + JupiterOne
CyCognito and JupiterOne Cyber Asset Attack Surface Management (CAASM) platform helps Security and IT Operations teams identify, protect, and manage their cyber asset attack surface.
Read more about CyCognito + JupiterOne
CyCognito + Armis
CyCognito and Armis help Security and IT Operations teams gain complete asset visibility, map critical attack paths, and accelerate remediation.
Read more about CyCognito + Armis
CyCognito + ServiceNow VR
CyCognito and ServiceNow® Vulnerability Response empowers organizations to focus on the most critical risks through real-time visibility, enabling faster response times and more efficient security and IT teams.
Read more about CyCognito + ServiceNow VR
CyCognito + Axonius
CyCognito and Axonius help Security and IT Operations teams identify, protect, and manage their cyber asset attack surface.
Read more about CyCognito + Axonius
CyCognito + Splunk
CyCognito and Splunk empower companies to take control of external risk and attack surface management by identifying critical security risks and correlating them with events seen within the Risk-Based Alerting platform.
Read more about CyCognito + Splunk
CyCognito + Cortex XSOAR
CyCognito and Cortex XSOAR empower companies to take control of external risk and attack surface management by unifying automation, case management, real-time collaboration, and threat intelligence management.
Read more about CyCognito + Cortex XSOAR
Understanding the Technology: EASM & BAS
EASM and BAS are security operations technologies getting a lot of attention for their ability to improve security posture. Learn about them, how they compare, how to make an informed selection, and more.
Read more about Understanding the Technology: EASM & BAS
Understanding the Technology: Threat Intelligence & Exploit Intelligence
Learn the strengths of Exploit Intelligence and compare them against traditional threat intelligence platforms.
Read more about Understanding the Technology: Threat Intelligence & Exploit Intelligence
Five Lessons for Security Leaders from the Past Year’s Breaches
2022 was a challenging year for cyber security pros with an array of high-profile breaches. Learn about the breaches, the lessons learned, and, most importantly, how to ensure the next story isn’t about you.
Read more about Five Lessons for Security Leaders from the Past Year’s Breaches