What Are Attack Surface Management Tools
Attack surface management (ASM) tools continuously discover externally accessible assets, validate what is reachable and how it behaves, then surface prioritized issues based on exploitability and business context.
Functions and features of ASM tools include:
- Asset discovery and monitoring: Scan and map all internal and internet-facing assets, including domains, sub-domains, APIs, and cloud services, and continuously monitor for changes, misconfigurations, and vulnerabilities.
- Inventory and classification: Create a comprehensive inventory of all digital assets, both known and unknown, to ensure complete visibility.
- Vulnerability and risk assessment: Analyze findings to identify exploitable weaknesses and assess their severity.
- Risk prioritization: Help organizations prioritize which risks to address first based on factors like potential impact and exploitability.
- Continuous validation: Regularly re-assesses identified assets and risks to ensure findings remain accurate over time. Validates whether vulnerabilities still exist and if remediation efforts have been successful.
This is part of a series of articles about attack surface management.
What we mean by ASM tools in this article
ASM overlaps with vulnerability management, cloud security, and third-party risk. For the list below, we include products that help teams (1) discover externally accessible assets, (2) validate security conditions on those assets, and (3) prioritize remediation.
Some vendors cover the full workflow, while others focus on one layer (discovery, validation, prioritization, vendor posture).
Importance of Attack Surface Management Tools
Attack surface management tools play a critical role in modern cybersecurity strategies. As organizations expand their digital footprint,across cloud environments,on-prem, and third-party services, the number of exposed assets grows. ASM tools help security teams stay ahead by continuously identifying and managing these risks in real time.
Key reasons why ASM tools are essential:
- Continuous visibility: ASM tools provide ongoing monitoring of all publicly reachable assets, including shadow IT and forgotten systems, helping eliminate blind spots.
- Proactive risk identification: Using active testing they can detect vulnerabilities, misconfigurations, and weak points before attackers can exploit them.
- Prioritization of threats: By assessing the criticality and exploitability of discovered issues, ASM tools help teams focus on the most pressing risks first.
- Attack surface reduction: They support efforts to minimize exposure by flagging unnecessary services, open ports, or outdated software.
- Improved incident response: With better context and asset visibility, security teams can respond faster and more effectively to incidents.
- Compliance support: Many ASM tools assist in aligning with security frameworks and regulatory requirements by documenting exposures and remediation efforts.
- Third-party risk management: Some tools extend visibility to external partners or vendors, identifying risks beyond the organization’s direct control.
Key Features of Attack Surface Management Software
Asset Discovery
Asset discovery involves identifying all assets within an organization’s network. This includes devices, applications, and cloud services that might be overlooked. It creates an accurate inventory, which serves as the foundation for further security measures. Automated tools are often used to conduct continuous scans, ensuring that no asset goes undetected.
This feature is essential because overlooked assets can become vulnerabilities. Identifying assets manually is impractical due to the scale and complexity of modern IT environments. ASM tools simplify this process and significantly reduce the risk of hidden threats by ensuring that every asset is accounted for and monitored.
Inventory and Classification
Inventory and classification involve organizing the discovered assets into categories based on their function, criticality, and risk level. This helps in understanding which assets are most vital to an organization and which ones pose the greatest security risks. By maintaining a detailed and up-to-date inventory, organizations can prioritize their security efforts more effectively.
Classification also involves tagging assets with metadata such as ownership, lifecycle stage, and compliance requirements. This ensures that all assets are adequately protected and that high-risk areas receive the necessary attention. It also simplifies the process of applying security policies and responding to incidents.
Vulnerability and Risk Assessment
Risk scoring involves evaluating the potential impact and likelihood of security incidents on identified assets. ASM tools assess vulnerabilities, threat levels, and the criticality of assets to assign a risk score. This score helps organizations understand the relative danger each asset poses to the overall security posture.
By quantifying risk, these tools enable organizations to prioritize their resources and efforts on the most significant threats. Security grading provides an overall assessment of an organization’s security posture. It considers the effectiveness of existing security controls, the presence of vulnerabilities, and compliance with industry standards.
Risk Prioritization
Risk detection involves identifying potential security issues within an organization’s assets. ASM tools use automated scanning and analysis techniques to uncover vulnerabilities, configuration errors, and signs of malicious activity. The detection process covers known threats and also identifies new, emerging vulnerabilities that could be exploited by attackers.
Prioritization is the next step, where detected risks are ranked based on factors such as the severity of the vulnerability, the value of the affected asset, and the potential impact on the organization. This allows IT teams to focus their efforts on addressing the most critical issues first.
Continuous Monitoring
Continuous security monitoring provides ongoing assessment and vigilance over an organization’s attack surface. Unlike periodic assessments, continuous monitoring offers real-time insights into security posture, allowing for immediate detection and remediation of vulnerabilities and threats.
This capability is essential for maintaining a resilient security posture in the face of evolving cyber threats. Continuous monitoring relies on automated processes and advanced analytics to ensure that security measures are always up-to-date and effective. It also supports compliance with regulatory requirements by providing continuous evidence of security activities.

Operationalizing CTEM Through External Exposure Management
CTEM breaks when it turns into vulnerability chasing. Too many issues, weak proof, and constant escalation…
This whitepaper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.

Challenges in Attack Surface Management
While attack surface management tools offer valuable capabilities, implementing and maintaining them comes with several challenges. These obstacles can impact the effectiveness of ASM initiatives and require careful consideration by security teams.
- Asset discovery gaps: Even with automated tools, some assets may remain undetected, especially in large or dynamic environments with frequent changes. Shadow IT, temporary cloud instances, and legacy systems often go unnoticed.
- Data overload: ASM tools generate large volumes of data. Without effective analysis and validation, teams may struggle to distinguish between critical threats and less urgent findings, leading to alert fatigue or missed risks. The program fails when teams can’t quickly confirm whether a finding is real and who owns the fix.
- Integration complexity: Integrating ASM tools with existing security infrastructure such as SIEM, SOAR, or vulnerability management platforms can be complex and time-consuming. Poor integration limits the value of ASM insights.
- False positives and inaccuracies: Inaccurate classifications or false positives can divert resources and reduce confidence in the tool’s output. Fine-tuning is often required to improve accuracy and relevance.
- Internal and external visibility gap: ASM tools often provide stronger insight into exposed assets than internal systems, leaving gaps in internal network coverage. Additionally, assets managed by third parties or hosted in decentralized environments may not be fully visible, creating blind spots in the overall attack surface.
- Resource constraints: ASM programs require skilled personnel to manage findings, triage alerts, and implement fixes. Organizations with limited security staff may struggle to keep up with the volume of work ASM tools generate.
- Third-party visibility limits: While some ASM tools offer third-party risk management, visibility into external vendors’ environments is often partial or outdated, limiting the ability to assess real-time risks.
- Evolving threat landscape: As attack techniques evolve, ASM tools must continuously update their detection methods. Lag in threat intelligence updates can leave gaps in protection.
Notable Attack Surface Management Solutions
CyCognito
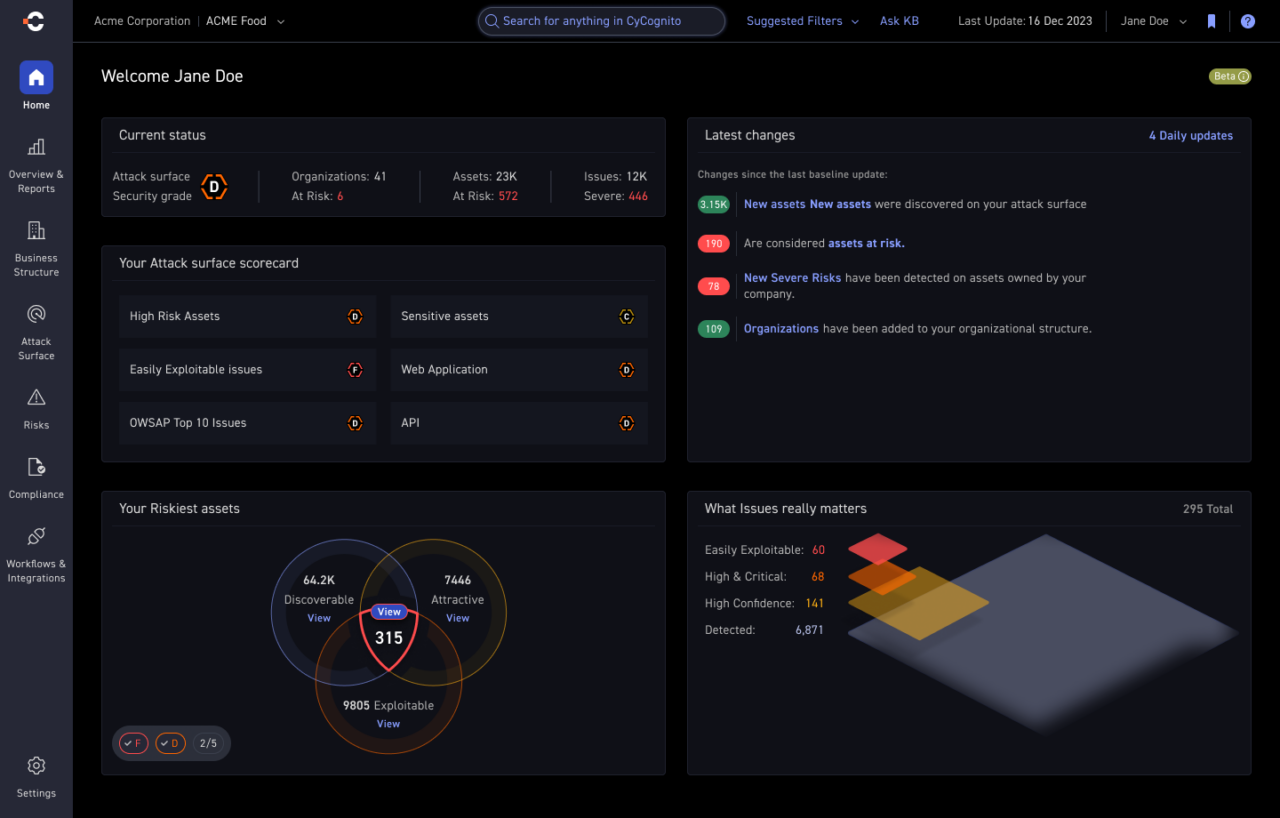
CyCognito is an attack surface management platform that continuously discovers externally accessible assets and validates exposures using active testing to produce high-confidence issues. It prioritizes what to fix based on exploitability evidence and business context, then routes issues to the right owners with proof and remediation guidance through existing workflows.
Key features of CyCognito include:
- Continuous asset discovery: Finds and tracks externally accessible assets across web apps, cloud services, domains, certificates, IPs, and APIs as the environment changes
- Active security validation: Confirms exploitability using 100,000+ tests (including always-on DAST). Tests cover security control validation, weak authentication, common OWASP vulnerabilities, data and AI service exposures, etc.
- Context-driven prioritization: Ranks issues using exploitability evidence plus asset criticality, ownership signals and attacker interest
- Organizational mapping: Connects assets to business units and subsidiaries to improve routing, accountability, and reporting
- Attack path simulation: Maps likely attacker paths across externally accessible assets to show how exposures chain together and which issues create the most direct routes to impact
- Actionable remediation guidance: Provides clear, best-practice steps to resolve prioritized issues, helping teams fix critical exposures faster.
- Holistic exposure management: Shares validated external exposure data with SIEM, SOAR, ticketing, and asset inventory/CMDB tools to support broader exposure management workflows across the security stack
- Evidence and workflow integrations: Provides verifiable proof and actionable guidance, with integrations into ticketing and security operations tools (for example ServiceNow, Jira, SIEM, and SOAR)
Key limitations include:
- Best fit at enterprise scale: Organizations with simpler environments may not need advanced features like organizational mapping
- No auto-remediation: CyCognito routes verified issues to the right owners and tracks progress, but remediation is executed by the responsible teams
- Primary focus is externally accessible assets: It is not designed to be a full internal asset management or endpoint security platform (external exposure data can be shared with those systems via integrations)
- Not a dedicated SBOM platform: If you need SBOM creation and governance, pair CyCognito with a purpose-built SBOM tool
Mandiant

Mandiant focuses on helping organizations strengthen their security posture by providing proactive and responsive capabilities grounded in real-world threat intelligence. It offers a range of consulting services, including incident response, red teaming, and offensive security testing, helping organizations identify and address security gaps before they are exploited.
Key features of Mandiant include:
- Incident response and crisis management: Support for technical response and strategic communication during security incidents to minimize impact and recovery time
- Threat-informed red teaming: Simulates real-world attacks using current threat actor tactics to identify weaknesses across networks, cloud environments, and applications
- Offensive security assessments: Includes penetration testing and architecture reviews to uncover exploitable vulnerabilities
- Cyber risk management consulting: Helps organizations assess risk exposure and improve security strategy in areas like M&A due diligence, OT security, and insider threat defense
- Integrated threat intelligence: Leverages intelligence from frontline investigations to inform defense strategies and improve detection and response
- Security operations optimization: Enhances threat detection, containment, and remediation processes by aligning security operations with current threat landscapes and business needs
Key limitations include:
- Requires customer input: Asset discovery and exposure identification often depend on data provided by the customer, which can lead to blind spots
- Limited business context mapping: Security findings are not always linked to specific business units or organizational structures
- Passive testing only: Reliance on static scanning methods such as banner grabbing and port scanning may lead to false positives and miss actively exploitable issues
- Generic risk prioritization: Without real-time exploitability analysis or business context, severity assessments may not reflect the true risk
- Cadence gaps: Because scans are performed at set and prolonged intervals, new risks can remain undetected until the next cycle, increasing the time window during which assets may be exposed.
Qualys CAASM
Qualys Cyber Asset Attack Surface Management (CAASM) extends traditional vulnerability management by integrating internal asset discovery with visibility into external, externally accessible assets.
Key features of Qualys CAASM include:
- Unified VM and CAASM platform: Provides a consolidated SaaS platform that merges vulnerability management with attack surface monitoring
- Outside-in and inside-out asset view: Uses integrations like Shodan.io to simulate an attacker’s perspective and reveal exposures not visible from within the network
- Risk-based vulnerability management: Goes beyond CVSS by factoring in malware activity, threat context, and business impact to prioritize vulnerabilities
- EOL and EOS software management: Tracks outdated or unsupported applications, issuing alerts to help plan decommissioning or upgrades
Key limitations include:
- Seed-based discovery requirements: Initial asset discovery depends on predefined inputs like seed data or configurations. This can limit visibility into unknown or unclassified assets
- Manual contextualization: Asset tagging and classification often require manual effort. This slows down context-building and can lead to gaps in understanding the full attack surface.
- Limited organizational mapping: The platform does not automatically map business structures such as subsidiaries or cloud-based business units, increasing the chance of missing critical assets
- Passive and agent-based testing only: Active security validation is not part of the core platform and often requires additional modules or agent-based scanning. As a result, many externally exposed assets may go untested
- Fragmented remediation support: Remediation workflows rely on integrations with third-party tools, and the platform lacks built-in capabilities to validate whether remediation steps have successfully addressed the risk
UpGuard
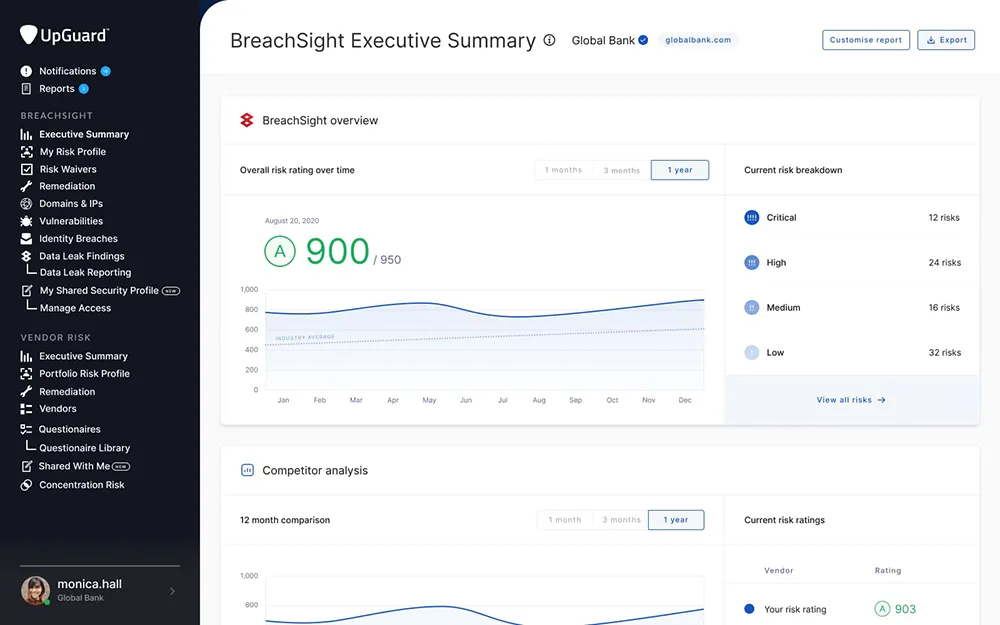
UpGuard provides an integrated platform for managing cyber risk across third-party vendors, digital assets, internal users, and trust relationships. Its platform focuses on delivering continuous visibility into an organization’s external attack surface and supply chain security posture.
Key features of UpGuard include:
- Vendor risk management: Continuously monitors third-party vendors for security posture changes and compliance gaps, supporting holistic TPRM programs
- Breach risk identification: Detects exposed data and misconfigurations in digital assets that could lead to breaches, with prioritized remediation guidance
- User risk assessment: Evaluates internal user behaviors and access risks to identify potential insider threats
- Trust relationship mapping: Provides visibility into trust-based connections between systems and third parties that could introduce hidden risks
- AI-powered automation: Uses AI for faster detection, prioritization, and response, improving efficiency in cyber risk workflows
- Unified risk view: Offers a single, real-time platform to monitor risk across supply chains, infrastructure, and people.
Key limitations include:
- Limited customization for security questionnaires: Creating custom security questionnaires can be challenging, especially for organizations with specific formats or detailed question sets. Some users still rely on their home-built questionnaires due to this limitation
- No built-in remediation capabilities: While UpGuard identifies risks and vulnerabilities, the platform does not offer integrated remediation tools. Users are responsible for handling remediation independently, which may slow down the response process
- Inability to exclude irrelevant assets: There is no straightforward way to dismiss machines that are offline, not externally accessible, or outside the organization’s control. These assets can still negatively affect security scores, even if they pose no real risk
- Customer support is AI-only: Users have reported difficulty in getting human support, with the chat system relying heavily on automated AI responses, which may not resolve more complex or nuanced issues
- Lack of advanced predictive analytics: While it provides real-time visibility, UpGuard lacks advanced predictive features like risk trend forecasting or proactive vendor scoring
Armis
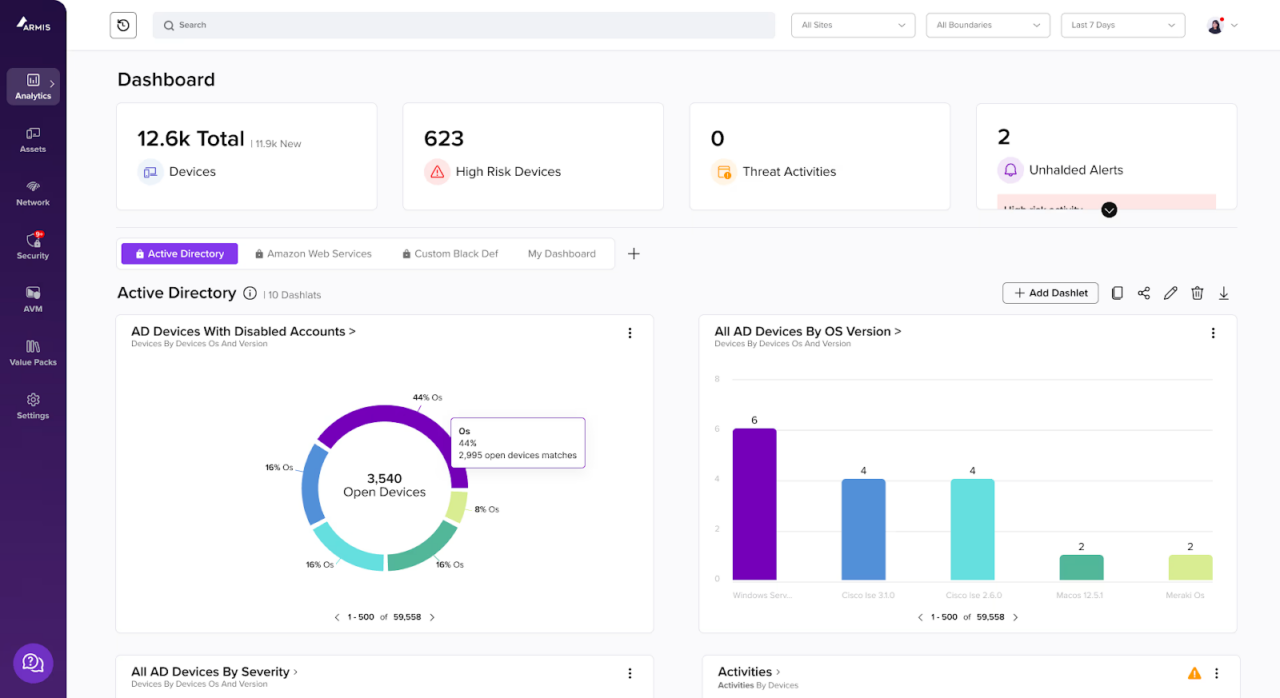
Armis Centrix™ offers a unified platform for managing cyber asset visibility and reducing exposure across IT, IoT, OT, cloud, and medical device environments. By aggregating and normalizing asset data from disparate systems, it creates a single source of truth to assess the organization’s full attack surface.
Key features of Armis include:
- Comprehensive internal visibility: Aggregates and deduplicates data across cloud, on-premises, and unmanaged environments to build a unified inventory
- Real-time risk prioritization: Combines vulnerability severity, exploitability, and asset business value to highlight the most urgent risks
- Contextual threat analysis: Correlates live network behavior, asset posture, and known threat indicators for accurate detection
- Agentless deployment: Monitors devices and networks without requiring agents, making it suitable for sensitive or hard-to-manage environments
- Automated response workflows: Supports policy-based actions and integrations to simplify remediation processes
- Support for diverse environments: Extends visibility across IT, OT, IoT, medical, and cloud systems in a single platform
Key limitations include:
- Internal asset visibility focus: Strong for internal IT, IoT, OT, and medical device environments, not designed as a primary external ASM platform.
- Integration and tuning effort: Value depends on data source integrations and ongoing tuning, especially early in deployment.
- Remediation depth varies: Orchestration is strong, but deeper remediation typically runs through external tools and existing IT workflows.
Wiz
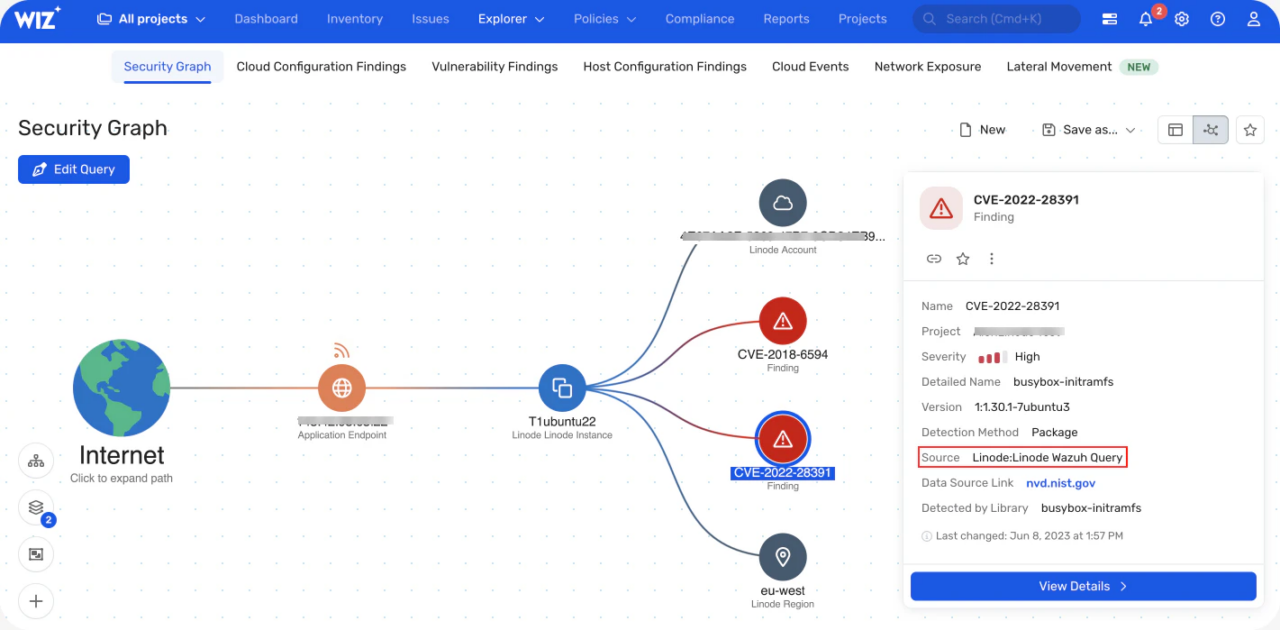
Wiz is a Cloud-native Application Protection Platform (CNAPP) which offers attack surface management capabilities, and can be used to uncover, contextualize, and prioritize internet-exposed assets across cloud environments.
Key features of Wiz include:
- Cloud-native asset discovery: Continuously detects public-facing assets like domains, IPs, and APIs across cloud, SaaS, and AI environments without requiring manual setup
- Context-aware exposure analysis: Combines external scanning with internal cloud context to determine real risk, including data sensitivity and privilege exposure
- Automated ownership mapping: Identifies the responsible business unit, infrastructure team, or developer to reduce time-to-remediation
- Attack path simulation: Uses graph-based correlation to highlight exploitable paths and reduce noise from low-impact findings
- No agent deployment required: Operates agentlessly across major cloud platforms for rapid onboarding and minimal operational friction
Key limitations include:
- Cloud-first coverage: Best for public cloud and cloud-native stacks, not a full replacement for internal asset management across on-prem environments.
- Signal volume in mature clouds: Large environments may need tuning to keep findings and risk shifts actionable.
- Premium pricing profile: Often a better fit for teams with significant cloud footprint and budget for broader CNAPP coverage.
Axonius
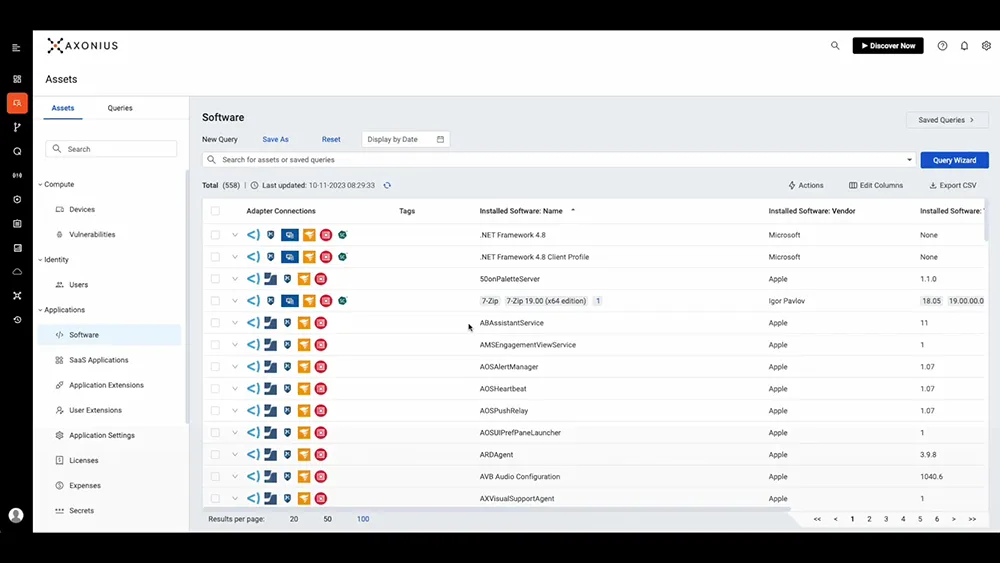
Axonius helps organizations maintain a continuously updated view of internal IT assets by aggregating asset data from across systems into a centralized platform. It enables security, IT, and GRC teams to monitor compliance, detect coverage gaps, and prioritize mitigation efforts in their on-premise environment.
Key features of Axonius include:
- Unified asset discovery and aggregation: Consolidates data from multiple sources to create an up-to-date inventory of cyber, software, and SaaS assets
- Policy enforcement and compliance tracking: Ensures assets align with defined policies through continuous monitoring and automated validation
- Risk prioritization and mitigation at scale: Surfaces the most critical exposures and supports targeted remediation aligned with organizational capacity
- CMDB reconciliation and coverage tracking: Identifies gaps in agent deployment and asset records, enabling more reliable IT operations
- Centralized reporting and KPI monitoring: Enables performance tracking across cybersecurity programs, supporting audits and strategic decisions.
Key limitations include:
- Limited external visibility: Axonius focuses primarily on internal assets and may not provide full visibility into exposed systems, third-party environments, or cloud-native exposures without third-party integrations.
- Dependency on connector coverage: Asset discovery depends on pre-built connectors to various tools and platforms. Gaps in connector support can limit visibility or require additional engineering effort.
- Manual context enrichment: Asset classification and tagging often require manual input, which can delay triage and reduce the speed of threat response workflows.
- No built-in attack surface testing: The platform aggregates asset data but lacks native capabilities for active vulnerability scanning or attack surface validation, requiring integration with separate tools.
Tenable.io
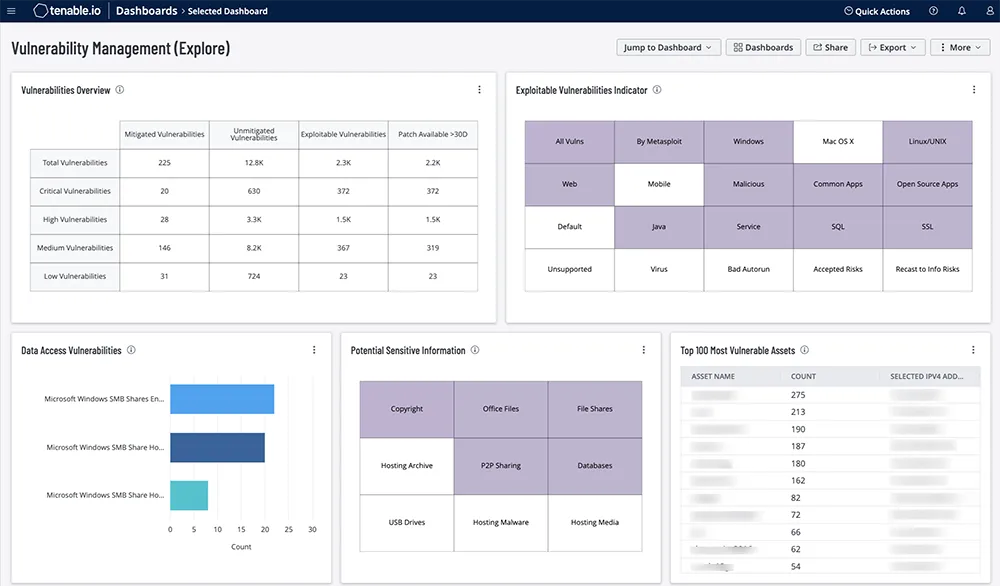
Tenable.io is a cloud-based vulnerability management solution to provide continuous visibility into asset exposures and support risk-informed remediation.
Key features of Tenable.io include:
- Continuous asset discovery and assessment: Automatically identifies known and unknown assets across environments, including highly dynamic or cloud-based infrastructure
- Risk-based vulnerability prioritization: Uses the Vulnerability Priority Rating (VPR) system, which combines threat intelligence, and asset context to score and rank vulnerabilities by actual risk
- Actionable remediation guidance: Provides best-practice steps for closing critical exposures, helping teams act quickly
- Integrated response workflows: Enables bi-directional ticketing and response orchestration to track and manage mitigation efforts
- Exposure management integration: Works with the Tenable One platform to unify visibility across IT, cloud, and operational environments.
Key limitations include:
- Manual discovery effort: Asset identification and validation require significant manual input, including customer-supplied seed data and manual attribution of ownership, which slows down discovery and increases operational overhead.
- Incomplete asset coverage: Focus is limited to known domains and IPs, leaving gaps in visibility across subsidiaries, cloud infrastructure, and external assets not explicitly mapped by the organization.
- Low-fidelity testing: Reliance on passive scanning and limited unauthenticated testing means many exposures may go unvalidated, especially across large or dynamic attack surfaces.
- Integration gaps: Limited support for automated integrations with third-party tools hinders workflow efficiency and slows down detection-to-remediation cycles.
- No remediation validation: Lacks automated mechanisms to confirm whether remediation actions have resolved vulnerabilities, requiring manual follow-up and reducing confidence in fixes.
Hunto.ai
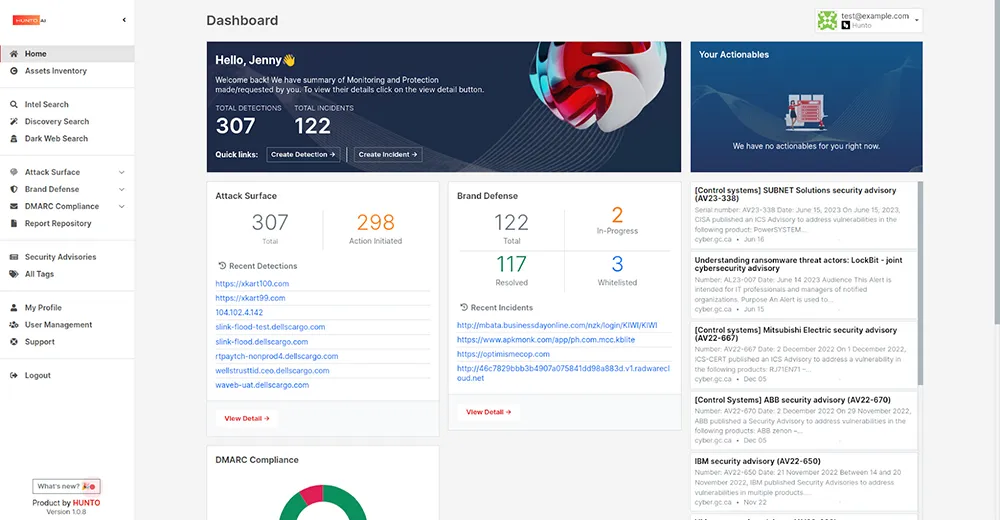
Hunto.ai provides an AI-driven platform for managing external threats across an organization’s digital presence. Its autonomous agents handle continuous discovery, monitoring, and mitigation of exposures related to attack surface, brand misuse, human risk, and email spoofing.
Key features of Hunto.ai include:
- Autonomous threat management: AI agents continuously scan for and mitigate external risks without manual input
- Attack surface monitoring: Identifies and tracks digital assets, highlighting vulnerabilities and exposures across the internet
- Brand protection: Detects impersonation, brand misuse, and fraudulent domains to safeguard organizational reputation
- Human risk detection and training: Delivers AI-based phishing simulations with post-click micro-training to raise user awareness
- DMARC+ enforcement and reporting: Enhances email security and spoofing protection with visibility and evidence for audits
- Audit-ready threat evidence: Provides documentation to support compliance with standards like RBI and ISO.
Key limitations include:
- Limited internal asset coverage: The platform focuses on external exposures and does not offer full visibility into internal network assets, limiting its utility for comprehensive ASM.
- Limited validation depth: Findings may rely more on monitoring and signals than active verification, so some items may require manual confirmation before remediation.
- No manual override controls: Users have limited ability to adjust or override AI-driven decisions, which may lead to issues with tuning or context-specific actions.
- Remediation not integrated: While exposures are identified, the platform lacks built-in remediation capabilities, requiring teams to manage fixes through separate systems.
- Restricted customization options: Users may find limited flexibility in customizing detection logic, reporting formats, or training workflows, especially for complex enterprise environments.
- Dependence on AI accuracy: Automated processes rely heavily on AI decision-making, which may occasionally result in missed threats or inaccurate classifications without human verification.
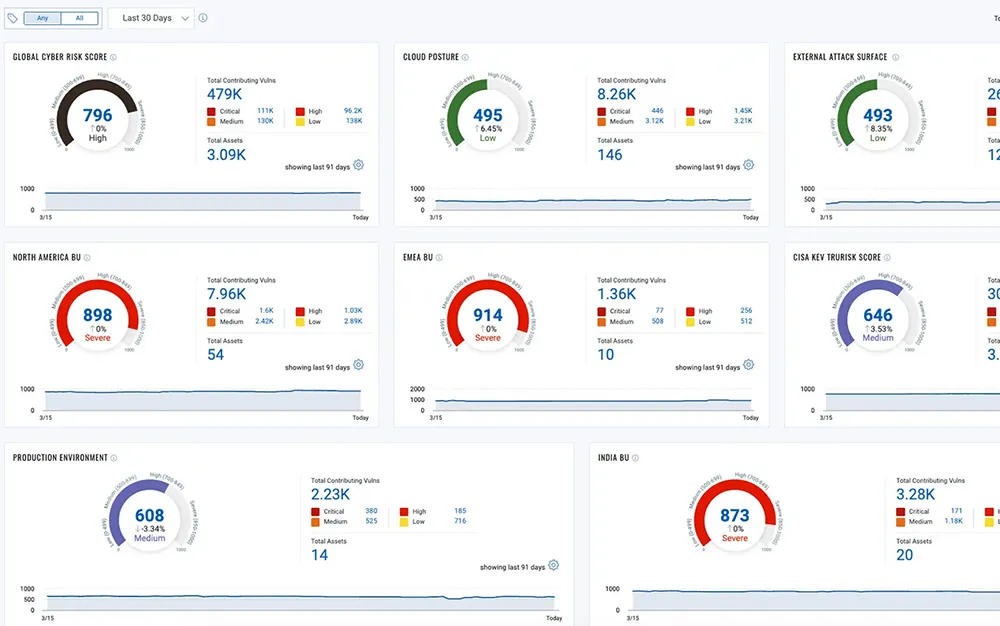
Bitsight
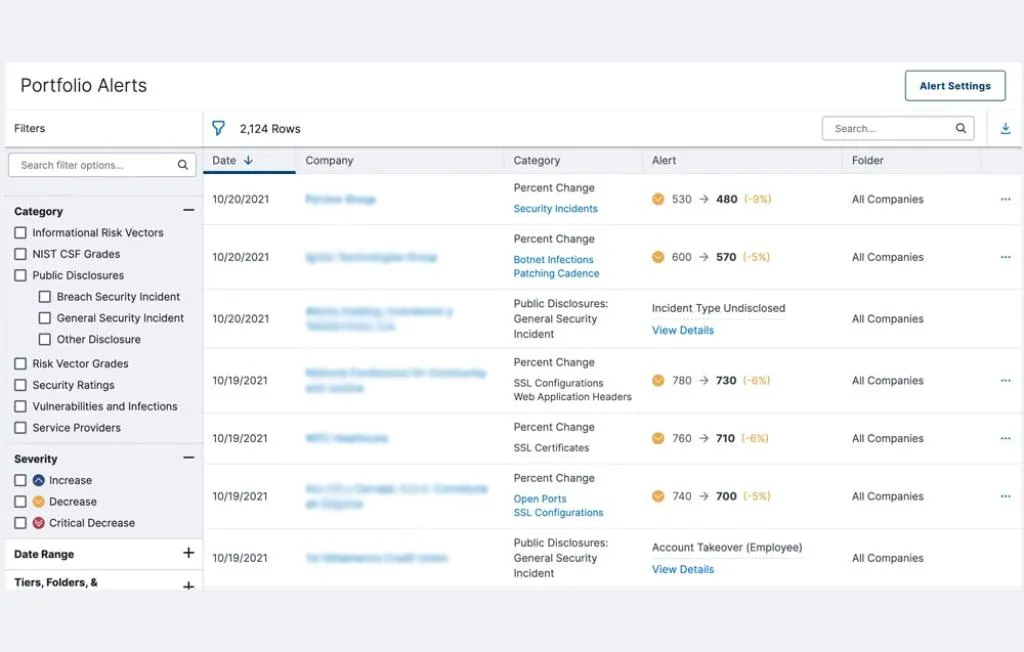
Bitsight delivers an AI-powered cyber risk intelligence platform that helps organizations detect, prioritize, and mitigate threats across their internal environments and third-party ecosystems.
Key features of Bitsight include:
- Third-party risk management: Continuously monitors vendor security posture and automates evidence collection aligned with frameworks like SIG and NIST
- Exposure management: Identifies unknown assets and shadow IT, providing a unified view of risk across digital infrastructure
- Cyber threat intelligence: Gathers real-time threat data from over 1,000 underground sources daily and enriches it with context for rapid insight
- Governance and reporting: Provides analytics to measure control effectiveness, benchmark against peers, and align strategy across stakeholders
- AI-driven prioritization: Uses machine learning and curated data to surface the most critical risks and accelerate decision-making
- Fourth-party visibility: Uncovers indirect vendor dependencies and product usage to improve supply chain transparency.
Key limitations include:
- Scoring transparency: The methodology behind Bitsight’s security ratings and risk vector (RV) scores lacks transparency, making it difficult for users to fully understand how grades are calculated.
- Detection gaps: Bitsight may overlook some known vulnerabilities or delay their detection, leading to inconsistent scan results across similar assets over time.
- False positives: The platform occasionally reports inaccurate findings, particularly related to domains without DNS records and risk vectors tied to web application and header configurations.
- Limited customization and integrations: Real-time customization is limited, and deeper integrations with governance, risk, and compliance (GRC) tools are not fully native.
- Vendor collaboration challenges: Some users have experienced confusion around vendor access to the SPM (Security Performance Management) portal and difficulties with the EVA (Evidence Validation Assessment) invitation process.
- Customer support delays: Response times from Bitsight’s support team have declined, with some users reporting delays of several days for issue resolution.
SentinelOne Singularity
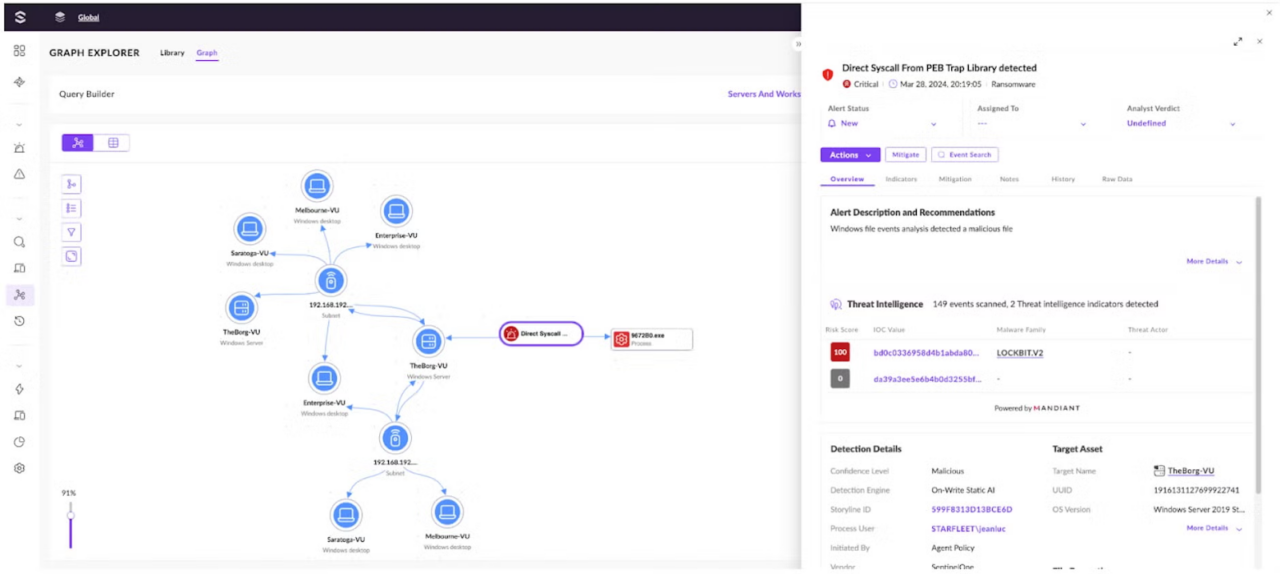
SentinelOne Singularity Complete is an endpoint and cloud workload security platform that uses AI-driven prevention, detection, and response to provide visibility into assets, telemetry, and incidents across enterprise environments.
Key features of SentinelOne Singularity include:
- Unified agent for endpoints and cloud: Improve visibility with an agent covering multiple operating systems and cloud environments, collecting telemetry to support investigation, monitoring, and analysis of endpoint and workload activity.
- On-device AI prevention: Use autonomous, on-device AI models to block malware in real time, reduce opportunities for compromise, and continuously observe activity.
- Behavioral detection and threat hunting: Detect ransomware and unknown threats with behavioral and static AI, and conduct threat hunting using natural language queries.
- Correlated telemetry and event context: Automatically correlate telemetry from endpoints, cloud workloads, and identity sources to build event timelines and visual stories that show how attacks progress across environments.
- Automated and remote response: Apply policy-driven automated response, use remediation actions such as one-click rollback, block network activity, and investigate incidents remotely using remote shell capabilities.
Key limitations include:
- Complex user interface: The platform can be difficult to navigate for new users due to a non-intuitive UI and limited availability of ready-made templates.
- Advanced features behind paywall: Some advanced capabilities require additional licensing, increasing total cost of ownership.
- Performance impact: The agent can consume significant CPU resources, particularly on servers, and may degrade endpoint performance.
- False positives: Frequent false positives can create alert fatigue, and alert classification lacks the granularity needed to reduce noise effectively.
- Manual full disk scans: Full disk scans must be initiated manually, as there’s no built-in automation in the UI to schedule them.
- Dormant threat detection limitations: Detection relies on processes being active; dormant threats may remain undetected unless a full scan is performed.
- Web protection gaps: The platform lacks basic web reputation filtering, leaving users unprotected from malicious links.
Rapid7 Surface Command
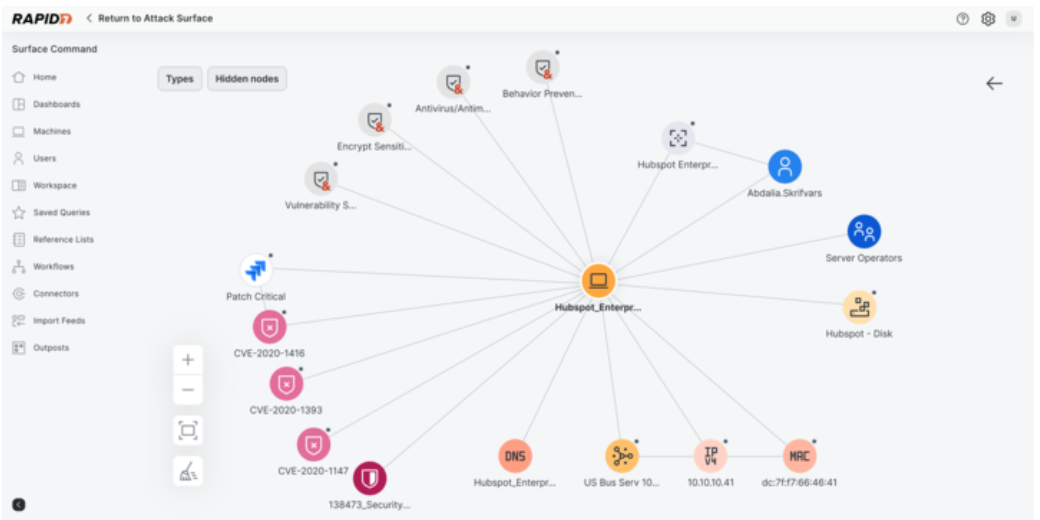
Rapid7 Surface Command is an attack surface management product that provides continuous visibility of assets from endpoint to cloud, detecting exposed resources and prioritizing security issues using contextual enrichment and exposure insights.
Key features of Rapid7 Surface Command include:
- Continuous asset discovery and monitoring: Conduct ongoing discovery and monitoring of internal and external assets to maintain current inventories, reduce blind spots, and reveal exposed resources across the digital environment.
- Context-enriched exposure prioritization: Use native and third-party business context to enrich findings and prioritize remediation on exposures that attackers are more likely to exploit.
- Reduction of data silos: Combine data from multiple sources to reduce security-information silos and enable coordinated protection for strategic business units and other important environments.
- Attack-path oriented insights: Provide perspective into potential attack paths and access points so security teams can focus on controls and monitoring where compromise is more likely to occur.
Key limitations include:
- Alert prioritization issues: Alerts can appear out of sequence or mixed with outdated information, making it harder for analysts to identify which issues to prioritize
- UI inconsistencies: The portal occasionally loads elements in unexpected places, requiring additional navigation and slowing down workflows
- False positives and noise: The system may flag legitimate internal components—like internal certificate authorities—as vulnerabilities, requiring manual overrides or exclusions
- Misclassified vulnerabilities: Some findings may not apply to the environment being scanned, leading teams to spend time investigating irrelevant issues
- Complex policy configuration: Setting up alert profiles and policies can be unintuitive and complex for new users
- Historical data processing delays: Analyzing past events can be slower than expected, impacting the speed of investigations
- Support limitations: Users have reported occasional difficulties in reaching support and receiving detailed initial analyses when opening support cases.
Tips to Select an Effective Attack Surface Management Tool
Choosing the right ASM tool depends on the specific needs of your organization, its infrastructure, and risk appetite. Below are key factors to consider when evaluating and selecting a solution:
- Comprehensive asset discovery: Ensure the tool can discover all assets on-prem, cloud, third-party, shadow IT, and ephemeral services across your environment without relying on manually provided inputs.
- Real-time continuous monitoring: Look for tools that provide persistent, real-time visibility rather than periodic scans. Continuous updates are essential for detecting dynamic changes and emerging threats.
- Risk-based prioritization: The platform should go beyond CVSS scores and prioritize vulnerabilities based on exploitability, asset value, business impact, and exposure context.
- Contextual insights: Choose a tool that enriches findings with asset ownership, relationships, and usage patterns to support faster action.
- Integration capabilities: Check for native integrations with SIEM, SOAR, vulnerability scanners, and ticketing systems to streamline workflows and automate response.
- Third-party and supply chain monitoring: If needed, opt for solutions that extend visibility into vendors, subsidiaries, and other external dependencies.
- User experience and reporting: A clear UI and actionable dashboards improve usability. Automated reporting should support compliance and executive visibility.
- Scalability and automation: Ensure the tool can scale with organizational growth and automate routine tasks to reduce operational load.
- Data accuracy and low false positives: Prioritize tools with strong accuracy and filtering to limit noise and reduce alert fatigue.
- Vendor support and threat intelligence: Consider vendors that provide timely threat intelligence updates and responsive support.
Conclusion
Attack surface management tools are essential for organizations to gain comprehensive visibility into their IT infrastructure and identify potential vulnerabilities. By automating asset discovery, classification, and continuous monitoring, these tools help prioritize risks and streamline remediation efforts. ASM solutions are crucial for maintaining a strong security posture in the face of evolving cyber threats, enabling organizations to protect sensitive data and maintain business continuity.