What is the Axios npm supply chain attack?
On March 31, 2026, two malicious versions of Axios were published to npm, [email protected] and [email protected], using credentials stolen from a lead Axios maintainer. The attacker injected a hidden dependency into both releases that drops a remote access trojan (RAT) on any machine that ran npm install during the exposure window. No CVE identifier has been assigned at the time of writing.
The malicious dependency executes automatically at install time via a postinstall hook, without any action by the developer. It deploys platform-specific payloads on macOS, Windows, and Linux, establishes a connection to an attacker-controlled server, and then removes its own traces — leaving no obvious evidence in the installed package directory.
A successful compromise gives the attacker persistent remote access to the affected machine. On developer workstations, this means direct exposure of source code, cloud credentials, SSH keys, API tokens, and any secrets stored in environment files or accessible through the developer's configured tools.
In CI/CD environments, the same access extends to pipeline secrets, deployment credentials, and production infrastructure. Because the RAT executes at install time rather than at application runtime, even a machine that never deploys the built code is fully exposed the moment npm install completes.
Both versions were live for approximately two to three hours before npm removed them and placed the malicious dependency under a security hold.
What assets are affected by the Axios npm supply chain attack?
Any environment that installed [email protected] or [email protected] is affected. This includes developer workstations, CI/CD pipelines, containerised build systems, and server-side Node.js applications built during the exposure window on March 31, 2026.
Axios is the most widely used HTTP client in the JavaScript ecosystem, with over 300 million weekly downloads. It is a standard dependency in React and Vue front-end projects, server-side APIs, microservices, and developer tooling across virtually every industry. The attack targeted both the current 1.x and legacy 0.x release branches simultaneously, maximizing the range of affected projects.
Importantly, the RAT executes at install time — not when the application runs. Systems that built or updated dependencies during the window are at risk regardless of whether they are internet-facing.
What does our data show about exposure patterns?
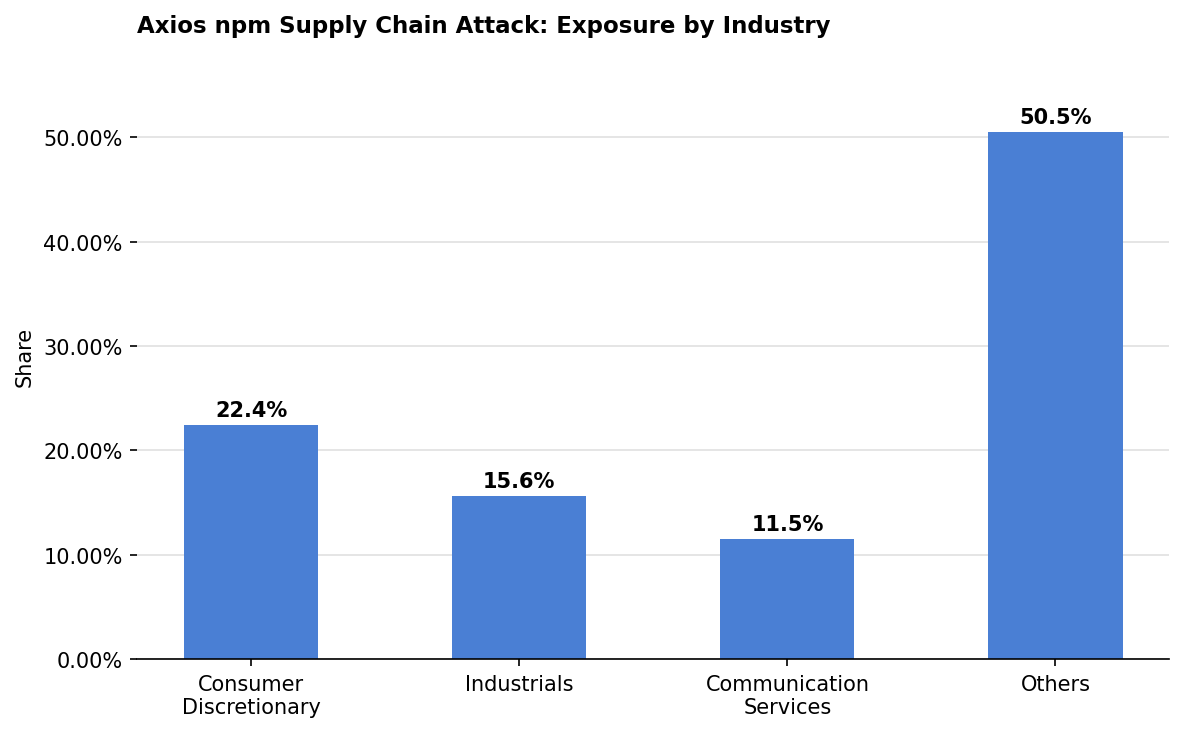
Exposure in this dataset is led by Consumer Discretionary at 22.4% of observed assets, with Industrials contributing 15.6%.
Consumer Discretionary organizations tend to run large, distributed engineering teams building customer-facing web applications — environments where Axios is almost universally present and where dependency update cycles are frequent. The combination of high update velocity and broad developer base increases the probability that the affected versions were pulled before the compromise was identified.
The 50.5% share across sectors not individually prominent in this dataset reflects the reality that Axios is not sector-specific. Any organization running active Node.js development during the exposure window carries meaningful risk, regardless of where it falls on the industry map.
Are fixes available?
The malicious versions have been removed from the npm registry and are no longer installable. A clean npm install axios will now resolve to [email protected] (for 1.x users) or [email protected] (for 0.x users).
Registry removal does not remediate systems that already installed the affected versions. The RAT dropper executed at install time and cleaned up after itself and the package directory will appear clean even on a compromised system. Defenders should audit package-lock.json files and CI/CD run logs directly for references to either affected version, rather than relying on the current state of node_modules to determine exposure.
Are there any other recommended actions to take?
Audit all lock files and pipeline logs for [email protected], [email protected], or plain-crypto-js in any version. Any system where these were installed should be rebuilt from a known-good state, not cleaned in place, with all credentials accessible at install time rotated immediately, including cloud access keys, CI/CD secrets, npm tokens, and SSH keys.
As a standing build hygiene measure, run npm ci --ignore-scripts in CI/CD environments to prevent postinstall hooks from executing during automated builds.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for the Axios npm supply chain attack in the CyCognito platform and is actively researching enhanced detection capabilities for this vulnerability.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



