In 2026, the ASM scorecard has moved well past discovery. The market is shifting from visibility to validated proof: what’s exploitable, what connects to critical systems, and what requires immediate action.
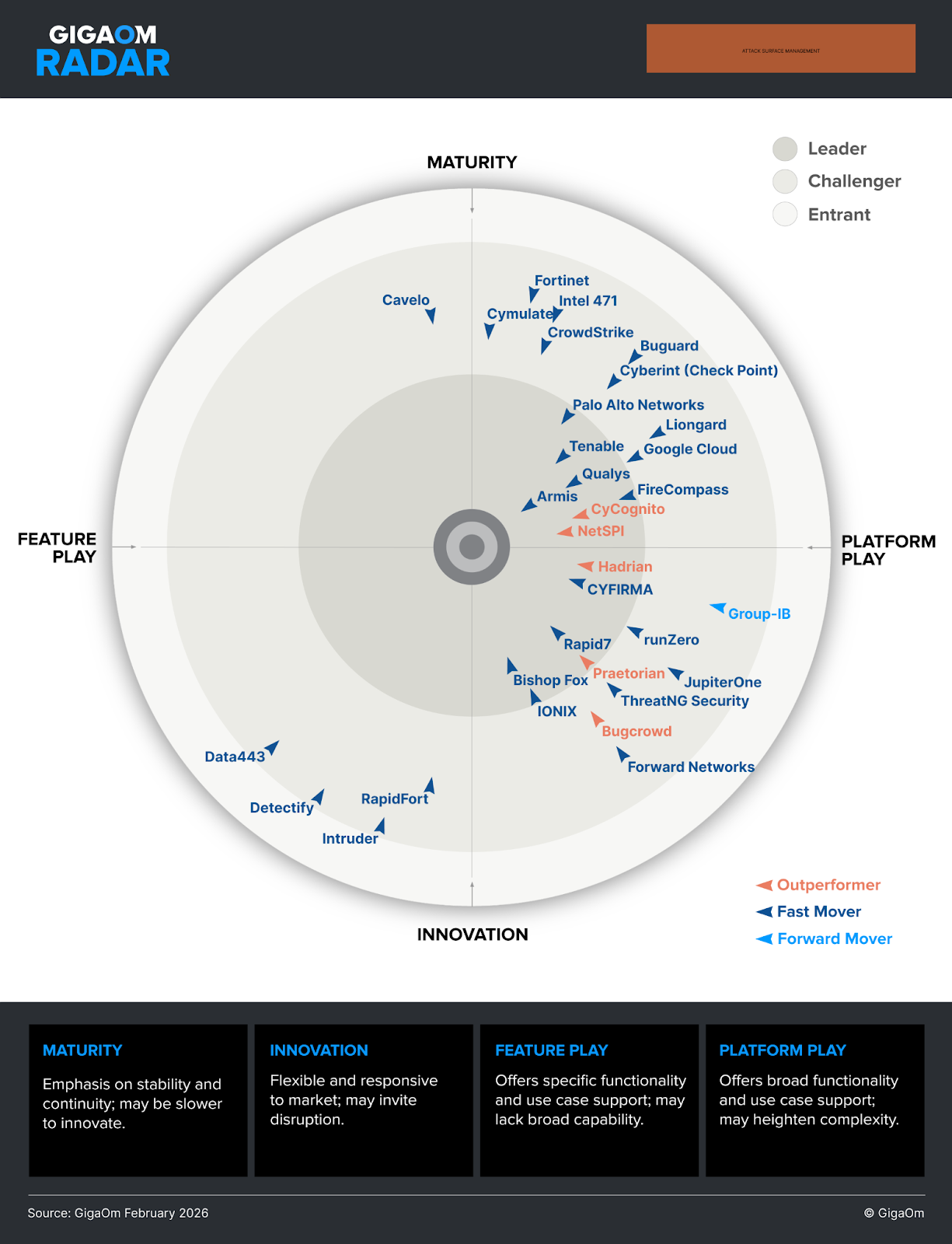
The latest GigaOm Radar for Attack Surface Management is anchored to that bar. Across 32 vendors, it highlights the platforms that have moved beyond inventory into contextual prioritization and actionable validation.
This is the turning point CyCognito is built for. That’s why this year’s report named us a Leader for the third consecutive year and, for the first time, an Outperformer.
From Security Tool to Business Imperative
At the core of the GigaOm Radar for Attack Surface Management is a simple thesis: ASM is moving from a technical control to a business function. In this framing, ASM becomes a part of the operational resilience conversation for its ability to give leadership a current, defensible view of what the organization owns, what is exposed, and what requires action.
“For the C-suite, ASM is no longer an optional hygiene tool but a business imperative for operational resilience.”
To serve this function, the report argues ASM has to default to the attacker’s perspective. Only through this lens can it outgrow its visibility-first origins and become a decision driver, helping teams prioritize what is plausibly actionable (exploitability and reach) and focus remediation on actual risk and mission-critical assets.
“By providing an attacker's eye view of the enterprise, these solutions enable organizations to prioritize remediation based on actual exploitability rather than theoretical severity. This shift allows leadership to move from reactive firefighting to strategic risk reduction.”
The gap this highlights is between “we found 10,000 things you own” and “here are the handful of validated priorities that require action now.”
That gap is where ASM value lives today.
CyCognito in the 2026 GigaOm Radar
GigaOm’s evaluation connects CyCognito directly to the gap the market is now trying to close: moving from broad visibility to a small set of validated priorities teams can act on, even in complex enterprise environments.
As GigaOm analyst Chris Ray noted:
“CyCognito takes a methodical approach to attack surface management by focusing on accurate asset discovery and contextualized risk assessment. This strategy emphasizes maintaining comprehensive visibility while providing actionable context for identified risks, particularly focusing on validated threats.”
In the report, CyCognito’s approach is recognized for its focus on contextualized asset discovery and validated risk assessment, emphasizing the following capabilities:
1. Attack path mapping
CyCognito visualizes the attack paths an attacker would take by mapping relationships between discovered assets and exposures. Moreover, by correlating external findings with internal context from platforms like Armis or Axonius, it helps teams see the shortest remediation paths from exposed edge assets to critical internal systems.
2. Continuous validation
CyCognito’s automated testing engines deliver actionable output even in environments with over 100 million assets. The engines autonomously validate exposures, across 90,000+ tests and 30+ categories, filtering noise to identify the approximately 0.01% of items that are truly critical, with consistent performance across large-scale operations.
3. Asset categorization
CyCognito adds over 160 context elements per asset, spanning technical details, security signals, and ownership. This granularity accounts for compensating controls (such as WAF or SSO) and supports more precise prioritization and automated workflows.
4. Ecosystem integration
CyCognito is designed to operate as part of the enterprise security stack. Bidirectional integrations (including Armis and Wiz) connect external exposure to internal context, while prebuilt integrations with CMDB and workflow systems like ServiceNow help teams route work and accelerate time-to-value.
5. Automated intelligence
Using a graph-based model with evidence-based attribution, the platform normalizes and resolves entity data so findings stay current as environments change, and prioritization updates without manual effort.
Why Outperformer Is Not a Vanity Label
GigaOm reserves the Outperformer designation for vendors showing momentum through execution and innovation. This year, CyCognito earned this status, reflecting strong progress in areas including ecosystem integration and automated testing maturity.
The core value of these is continuous validation, which serves as an evidence-based bridge between “we found another potential issue” and “we need to fix it asap.” A conclusion that becomes even more actionable when enriched with context from integrated systems, clarifying potential impact, attack paths, and blast radius.
And on the flip side, of course, validation is also what gives teams permission to ignore noise, helping focus (often scarce) remediation capacity on what matters most.
In the end, validation is what enables ASM to excel at its security function while also acting as a cost saver and an optimizer.
When validation is continuous and integrated, security can act with intent and calculated urgency, routing fewer high-priority items to the right owners.From a business perspective, this shifts the conversation to measurable outcomes: reduced ticket volume, lower MTTR, less engineering capacity consumed, and lower incident response spend.
The CTEM Lens
“The narrative has now moved decisively toward exposure management and alignment with continuous threat exposure management (CTEM) frameworks.”
No ASM analysis in 2026 is complete without acknowledging CTEM, a framework that sits behind more and more conversations about exposure reduction. The GigaOm report echoes that shift, looking at ASM through the lens of which platforms support that cycle in practice (prioritization, validation, and mobilization).
One way to read the Radar is as a practical translation of CTEM into product criteria, focusing on the capabilities that drive outcomes across the cycle.
| CTEM lens | How it shows up in the Radar |
|---|---|
| Table stakes | Baseline capabilities are treated as required (not differentiators). Inclusion expects more than simple asset enumeration. |
| Discovery | Continuous discovery and inventory management are foundational, with an emphasis on finding unknown assets and keeping inventory current. |
| Prioritization | Emphasis on contextual prioritization, including attacker-relevant signals (for example attack path analysis, exploitability and threat intelligence about activity “in the wild”). |
| Validation | Validation is treated as the confidence layer that reduces noise and makes prioritization both precise and defensible. |
| Mobilization | Operational fit shows up through workflow support, automation/correlation, and integrations into systems teams run (ticketing, CMDB, security platforms). |
Working through this checklist delivers clear operational benefits, including tying exposure management to business KPIs: fewer urgent escalations, clear ownership, protected critical assets, and fewer exploitable conditions.
Final Thoughts
When a market moves quickly, you need a consistent yardstick. GigaOm has applied one to ASM for five years, long enough to show how the category’s center of gravity has changed. Anchored in defined criteria and a repeatable scoring model, the Radar serves as a trusted buyer’s guide that cuts through vague vendor narratives.
In 2026, ASM is measured by whether it supports the exposure-reduction cycle: prioritize what matters, validate what’s actionable, and mobilize remediation through the systems teams already run. CTEM has set that expectation, and the GigaOm Radar reflects it in how it evaluates the market.
GigaOm’s recognition of CyCognito as a Leader and an Outperformer reflects that bar. It signals that the category is now being judged on complementary capabilities that form the foundation for holistic exposure management and decision-grade output that holds up in enterprise environments.
Read the full report to see the criteria behind the evaluation and vendor positioning.



