What is CVE-2024-6670?
CVE-2024-6670 is a critical (CVSS v3 score: 9.8) SQL injection vulnerability. Threat researcher Sina Kheirkhah (@SinSinology) of Summoning Team (@SummoningTeam) discovered that, if the application is configured with only one user, unauthenticated attackers can leverage this vulnerability to retrieve users’ encrypted passwords.
What assets are affected by this vulnerability?
WhatsUp Gold is a network monitoring tool offered by Progress Software. CVE-2024-6670 affects all versions of WhatsUp Gold before 2024.0.0.
Is a fix available?
This critical vulnerability was patched by Progress in August 2024 alongside CVE-2024-6671. Organizations can patch this vulnerability by upgrading to version 2024.0.0.
Are there any other recommended actions to take?
Progress disclosed that unusual data in the “Name” column in the WhatsUp Gold UI can serve as a potential indicator of compromise (IOC). To access, go to Settings > Actions and Alerts > Alert Center Libraries > Threshold tab.
Is CVE-2024-6670 being actively exploited?
Researchers identified active exploitation of CVE-2024-6670 five hours after it was published on August 30th, 2024. Attackers were observed leveraging the vulnerability to bypass WhatsUp Gold’s authentication, installing remote access tools like Atera Agent, Radmin, SimpleHelp Remote Access, and Splashtop Remote. The use of remote access tools indicates threat actors may be using CVE-2024-6670 to deploy ransomware.
Research shows that even when patches and mitigations are made available quickly, not all organizations can or do immediately apply these fixes. CyCognito’s recent 2024 State of External Exposure Management report found that the median remediation time for severe security issues with CISA-issued advisories was 41 days.
How is CyCognito helping customers identify assets vulnerable to CVE-2024-6670?
CyCognito discovery and testing engines actively detect vulnerable versions of Progress Software WhatsUp Gold and leverage multiple tests to services of the vulnerable product and versions. All customers have access to an in-platform emerging security issue announcement as of September 26th, 2024. As of this publication, no vulnerable assets have been detected.
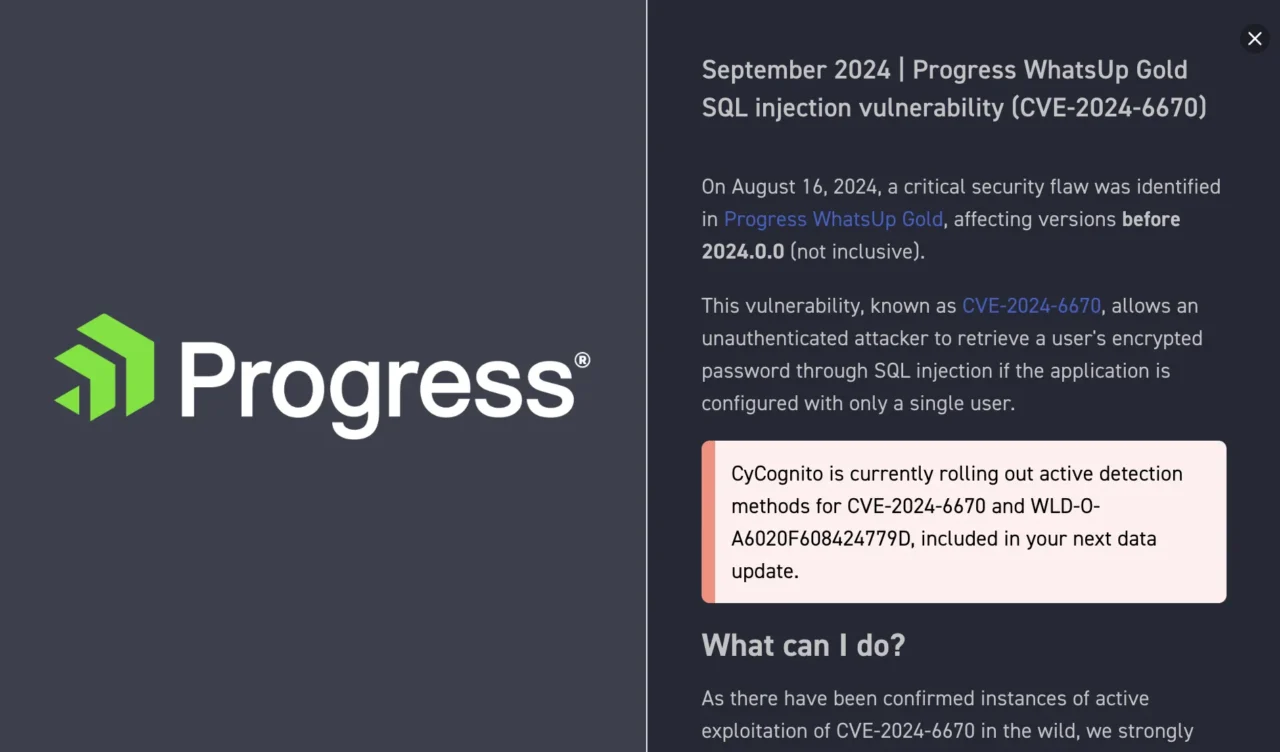
Figure 1: The alert sent by CyCognito for CVE-2024-6670
How can CyCognito help your organization?
CyCognito is an exposure management platform that reduces risk by discovering, testing and prioritizing security issues. The platform scans billions of websites, cloud applications and APIs and uses advanced AI to identify the most critical risks and guide remediation. Emerging companies, government agencies and Fortune 500 organizations rely on CyCognito to secure and protect from growing threats. Want to see how it works? Check out our website and explore our platform with a self-guided, interactive dashboard product tour. To learn how CyCognito can help you understand your external attack surface and exposed risks, please visit our Contact Us page to schedule a demo.



