What is CVE-2026-24858?
CVE-2026-20127 is a critical authentication bypass vulnerability affecting Cisco Catalyst SD-WAN Controller (vSmart) and Cisco Catalyst SD-WAN Manager (vManage). The flaw stems from improper validation within the control plane and management plane authentication mechanisms, allowing a remote, unauthenticated attacker to submit crafted requests that bypass standard authentication controls. Successful exploitation results in access to the system as a high-privileged internal user account.
Because the affected components orchestrate routing, policy distribution, and secure overlay connectivity across distributed enterprise environments, authentication bypass at this layer represents systemic risk. An attacker who gains unauthorized access to a vSmart controller or vManage instance can modify SD-WAN policies, alter device configurations, introduce rogue control plane peers, and potentially pivot into connected branch or data center infrastructure. Cisco assigned the vulnerability a CVSS score of 10.0, reflecting network-based exploitation without authentication and complete compromise of confidentiality, integrity, and availability of the affected system.
Public reporting indicates that exploitation has been observed in the wild. From an attacker perspective, centralized SD-WAN control infrastructure presents a high-value target because it provides a single management plane through which multiple geographically distributed sites can be influenced.
What assets are affected by CVE-2026-24858?
CVE-2026-20127 affects Cisco Catalyst SD-WAN Controller (vSmart) and Cisco Catalyst SD-WAN Manager (vManage) deployments across multiple release trains. Both on-premises and cloud-hosted instances are impacted if running vulnerable software versions.
Based on Cisco’s advisory, the following release trains and versions are affected:
- All releases earlier than 20.9
- 20.9 releases prior to 20.9.8.2
- 20.11 releases
- 20.12.5
- 20.12.6 prior to 20.12.6.1
- 20.13 releases
- 20.14 releases
- 20.15 releases prior to 20.15.4.2
- 20.16 releases prior to 20.18.2.1
- 20.18 releases prior to 20.18.2.1
Because vSmart and vManage act as central orchestration nodes, exposure risk is not limited to the appliance itself. Compromise can indirectly impact all edge routers and branch devices enrolled in the SD-WAN fabric. Internet-reachable management interfaces or control connections significantly increase the likelihood of exploitation.
What does our data show about exposure patterns?
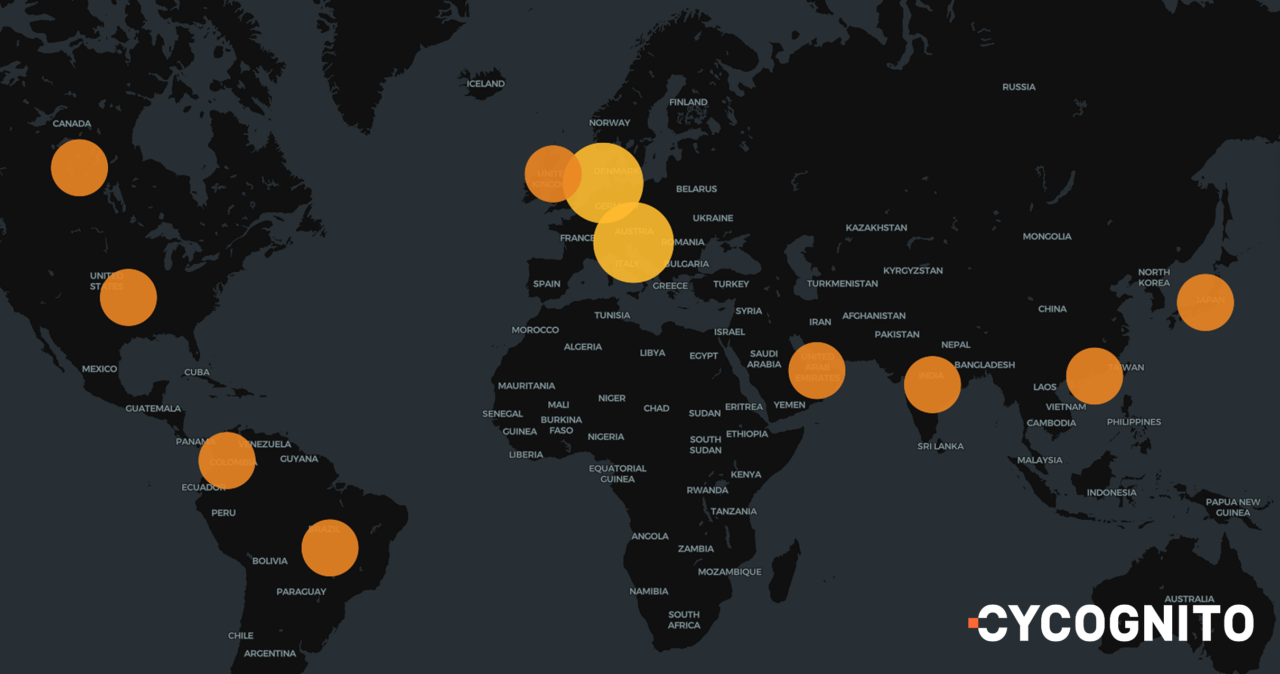
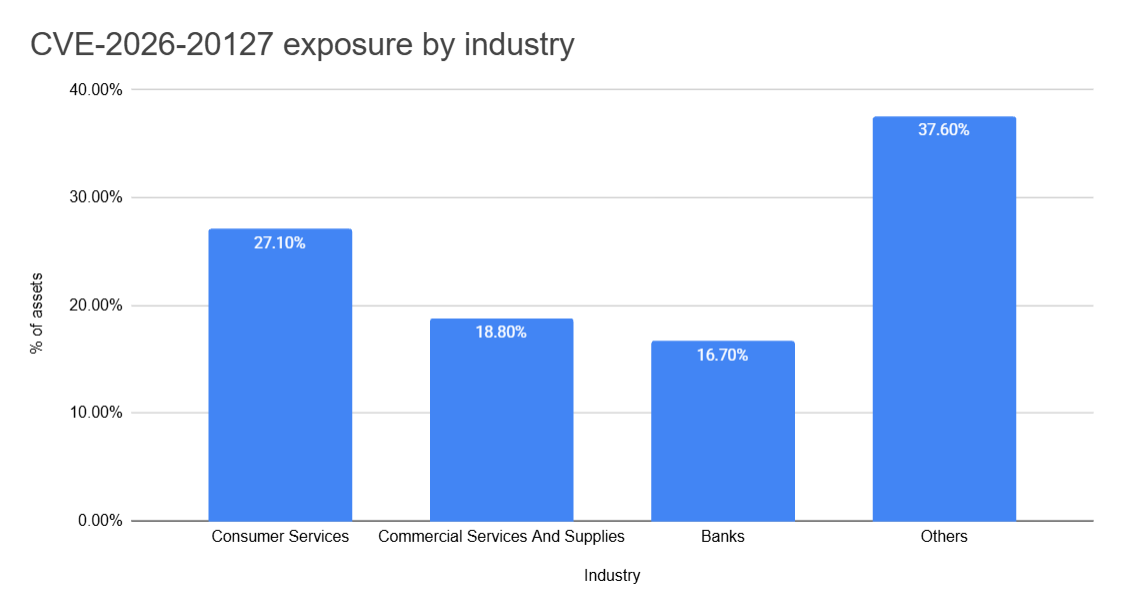
CyCognito exposure data indicates that externally reachable Cisco Catalyst SD-WAN infrastructure is distributed across multiple industries rather than concentrated in one vertical. Consumer Services and Commercial Services and Supplies represent a notable share of observed exposure, with Banks also prominent. Other industries make up the remaining observed exposure.
Across industries, exposure appears more consistent with unintentional reachability than deliberate publication. Misconfigured security groups, temporary administrative access rules that persist beyond change windows, and legacy IP allocations are recurring contributors. Because CVE-2026-20127 enables unauthenticated access, even brief or limited exposure increases risk.ler instances remaining externally accessible beyond their intended scope.
Are fixes available?
Cisco has released software updates addressing CVE-2026-20127 across affected release trains. Organizations must upgrade to fixed versions identified in Cisco’s advisory to remediate the issue. There are no effective workarounds that fully mitigate the vulnerability without upgrading.
Are there any other recommended actions to take?
Organizations should immediately inventory all Cisco Catalyst SD-WAN Controller and Manager instances, restrict management and control plane access to trusted networks only, review authentication and control plane logs for anomalous activity, validate peer configurations against known baselines, and conduct compromise assessments on exposed systems prior to and after patching.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for CVE-2026-24858 inside the CyCognito platform on February 2, 2026, and is actively researching enhanced detection capabilities for this vulnerability.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



