What is CVE-2026-21262?
CVE-2026-21262 is an elevation of privilege vulnerability affecting Microsoft SQL Server. The issue is caused by improper access control within SQL Server components, allowing an authenticated attacker to elevate privileges over a network.
According to Microsoft’s advisory and March 2026 Patch Tuesday disclosures, the vulnerability allows an attacker with valid access to a SQL Server instance to escalate privileges to higher database permissions, potentially reaching the sysadmin role under certain conditions. That level of access represents the highest administrative authority within SQL Server and can provide broad control over the database engine and related resources.
Public reporting indicates the vulnerability was addressed in Microsoft’s March 2026 security updates. While Microsoft has not publicly released detailed exploit mechanics, the flaw appears to involve insufficient enforcement of authorization boundaries inside SQL Server operations. In practice, that means a low-privileged but authenticated attacker may be able to cross intended permission limits and gain elevated rights within the database environment.
Successful exploitation could allow attackers to modify database objects, access sensitive data, alter configuration settings, or perform administrative actions normally reserved for highly privileged roles. Because SQL Server often supports critical enterprise applications, privilege escalation in the database layer can have broader consequences for application security, data integrity, and operational continuity.
What assets are affected by CVE-2026-21262?
The affected assets are Microsoft SQL Server deployments, including on-premises installations and SQL Server instances running in infrastructure-as-a-service environments. The impacted component is the SQL Server engine, specifically the mechanisms responsible for privilege enforcement and access control.
From an external exposure standpoint, the most relevant assets are not limited to directly exposed database servers. Internet-facing applications that rely on SQL Server in the background are also important because they can provide a path to authenticated database access. That includes customer portals, APIs, partner-facing services, remote access workflows, and internally developed business applications exposed to the internet.
In practical terms, the affected asset is any vulnerable SQL Server-backed environment where an attacker can obtain valid access to the database layer, whether through compromised credentials, application-layer abuse, exposed services, or another initial foothold. As a result, defenders should think beyond standalone database servers and include the broader application and infrastructure stack that depends on SQL Server.
What does our data show about exposure patterns?
Our data shows that exposure in this set is concentrated heavily in manufacturing. This prominence likely reflects where Microsoft SQL Server is commonly embedded rather than any indication that the vulnerability is specific to manufacturing.
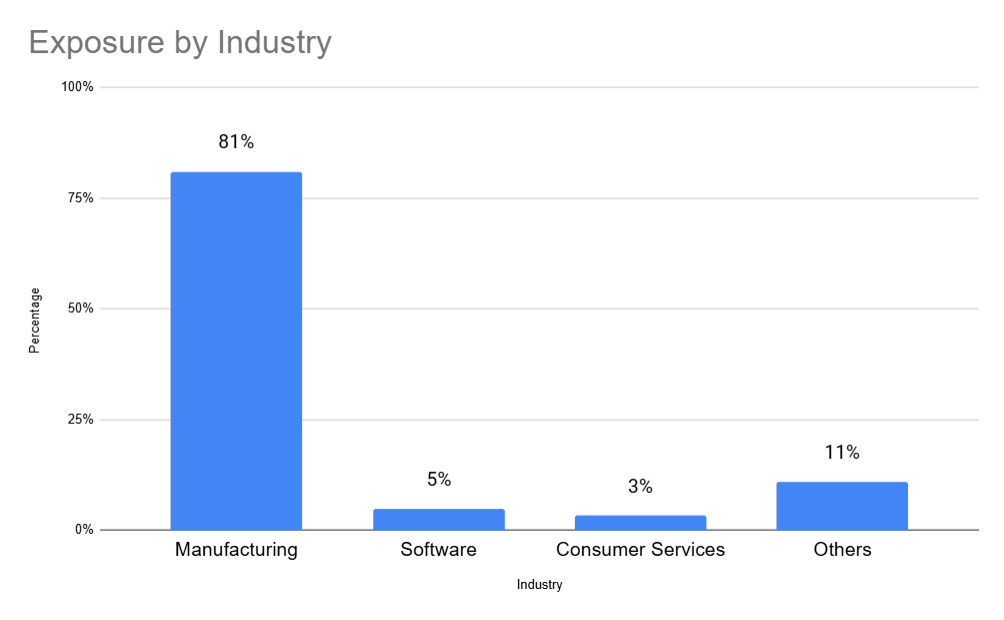
Manufacturing organizations frequently rely on SQL Server to support ERP platforms, manufacturing execution systems, supplier and distributor portals, and other long-lived operational applications. Many of those systems are tied to external business processes such as partner access, customer workflows, remote support, and regionally managed operations. That makes it more likely that SQL Server-backed applications, rather than directly exposed database servers alone, appear within the external attack surface.
The concentration in manufacturing suggests that environments with broad, interconnected operational systems are more likely to surface affected assets externally. For defenders, the relevant risk is not only direct SQL Server exposure, but also internet-facing applications and partner-facing systems that rely on SQL Server in the background.
Are fixes available?
Yes. Microsoft released patches for CVE-2026-21262 as part of the March 2026 Patch Tuesday security updates.
The vulnerability is addressed through SQL Server security updates that modify affected components in the database engine. Microsoft distributed updated builds for supported SQL Server versions, including updates for SQL Server 2022 that remediate the privilege escalation issue.
Organizations running affected SQL Server versions should apply the relevant cumulative update or security patch provided by Microsoft. Because SQL Server often supports critical business systems, patching may require coordination with application owners and validation in staging environments before production rollout. Even so, delaying remediation extends the window in which authenticated access to a vulnerable instance could become a higher-impact compromise.
Are there any other recommended actions to take?
Organizations should restrict direct internet exposure of SQL Server services, review externally reachable applications that depend on SQL Server, enforce strong authentication for database accounts, and audit role assignments for excessive privileges. Monitoring for unusual privilege escalation activity or unexpected role changes can also help detect potential abuse.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for CVE-2026-21262 in the CyCognito platform and is actively researching enhanced detection capabilities for this vulnerability.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



