
What is CVE-2026-27876?
CVE-2026-27876 is an arbitrary file write vulnerability in Grafana's sqlExpressions feature that can be chained with a Grafana Enterprise plugin to achieve remote code execution (RCE) on the underlying host.
The flaw exists because Grafana's SQL expressions feature permits writing arbitrary files to the server filesystem. An attacker can exploit this to overwrite a Sqlyze driver or write an AWS data source configuration file, ultimately obtaining an SSH connection to the Grafana host.
The vulnerability carries a CVSS v3.1 base score of 9.1 (Critical). It is network-accessible, requires no user interaction, and has a Changed scope — meaning a successful exploit can affect resources beyond the vulnerable Grafana instance itself.
Exploitation requires two preconditions: the attacker must hold Viewer-level access or higher, and the sqlExpressions feature toggle must be enabled on the target instance. No public proof-of-concept exploit has been published at the time of writing. The vulnerability was responsibly disclosed through Grafana Labs' bug bounty program.
What assets are affected by CVE-2026-27876?
CVE-2026-27876 affects Grafana instances running versions 11.6.0 through 11.6.13, and all versions from 12.0.0 through 12.4.1, where the sqlExpressions feature toggle is enabled.
The toggle is not on by default in all configurations, but environments that activated it for operational convenience — particularly those running Grafana Enterprise with data source plugins — are directly in scope.
Affected assets are typically internet-accessible Grafana dashboards deployed across cloud, on-premises, and hybrid environments. Grafana is frequently deployed with broad data source connectivity, storing database credentials, API keys, and cloud provider configurations. Containerized and Kubernetes-managed deployments are equally affected if the toggle is active.
Grafana Cloud, Amazon Managed Grafana, and Azure Managed Grafana were patched ahead of public disclosure and are no longer vulnerable. The vulnerability applies to both OSS and Enterprise deployments, and Grafana Labs recommends all users upgrade regardless of tier.
What does our data show about exposure patterns?
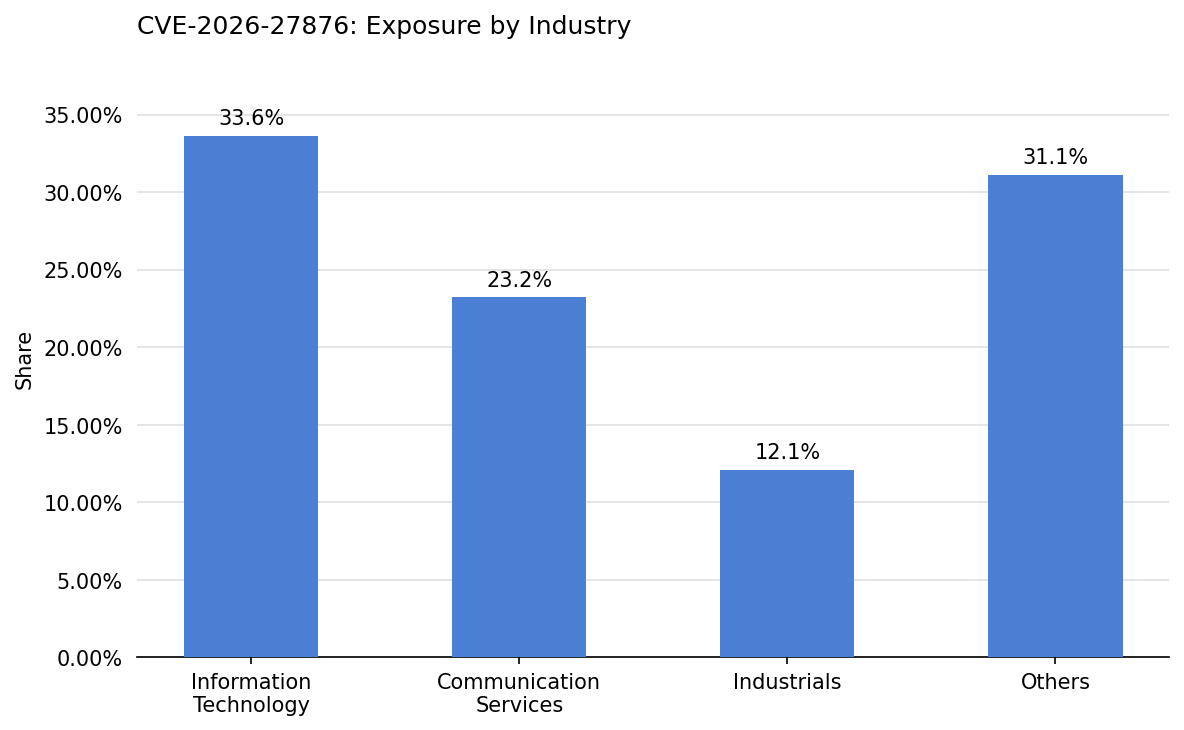
Exposure in this set is led by Information Technology at 33.6% of observed assets, with Communication Services contributing 23.2%. Together, these two sectors account for more than half of all affected instances identified.
Information Technology organizations routinely run Grafana as a core part of their observability infrastructure. The sector's prevalence reflects both the density of Grafana deployments and a tendency to enable advanced features like sqlExpressions in data engineering pipelines. Mixed ownership of monitoring assets across business units can allow non-default feature toggles to persist longer than intended.
The cross-sector spread points to Grafana's reach well beyond its core technology user base. In sectors like Industrials and Communication Services, Grafana is often administered by teams focused on reliability rather than security posture, making systematic review of feature toggles less likely during hardening cycles.
Are fixes available?
Patches are available. Grafana Labs released security-fixed versions in late March 2026, covering all supported release lines: 11.6.14, 12.1.10, 12.2.8, 12.3.6, and 12.4.2. Organizations running any affected version should upgrade as soon as possible.
For environments where an immediate upgrade is not feasible, Grafana Labs recommends deploying Grafana in a highly available environment with automatic restarts and placing a reverse proxy in front of Grafana to limit input payload size. These workarounds reduce risk but do not fully remediate the vulnerability.
Defenders should verify patch status directly with their Grafana deployment method rather than assuming a general upgrade covers all instances. Managed and containerized deployments may require additional confirmation.
Are there any other recommended actions to take?
Organizations that cannot upgrade immediately should disable the sqlExpressions feature toggle on all instances where it is not operationally required. Network access to Grafana should be restricted to authorized internal networks, query permissions scoped to least privilege, and administrators should monitor for anomalous query execution and unexpected file system activity on the Grafana host.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for CVE-2026-27876 in the CyCognito platform and is actively researching enhanced detection capabilities for this vulnerability.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



