What is CVE-2026-22557?
CVE-2026-22557 is a path traversal vulnerability in the Ubiquiti UniFi Network Application caused by improper limitation of a pathname to a restricted directory (CWE-22). A malicious actor with network access can exploit the flaw to traverse directory boundaries, access files on the underlying operating system, and manipulate those files to gain unauthorized access to system accounts.
The CVSS v3.1 base score is 10.0 — the maximum possible rating — with a vector of AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H. No authentication, user interaction, or special conditions are required. The vulnerability was published in Ubiquiti's Security Advisory Bulletin 062 on March 18, 2026, and was discovered by security researcher n00r3 (@izn0u).
The practical impact extends beyond file read. By manipulating files accessible through the traversal path — including database configuration, credential stores, or access token files — an attacker can achieve full account takeover of the UniFi controller. Because the UniFi Network Application manages network infrastructure such as access points, switches, and gateways, compromise of the controller translates directly into control over the underlying network environment.
CVE-2026-22557 is disclosed alongside a companion vulnerability, CVE-2026-22558, a NoSQL injection flaw rated 7.7 that allows privilege escalation by an authenticated attacker. The two can be chained: an unauthenticated attacker exploits CVE-2026-22557 to obtain initial access, then uses CVE-2026-22558 to escalate to administrative rights within the application.
What assets are affected by CVE-2026-22557?
The affected product is the Ubiquiti UniFi Network Application (also known as the UniFi Controller) in versions prior to 10.1.89 on the official release track, versions prior to 10.2.97 on the release candidate track, and UniFi Express firmware prior to version 4.0.13. Versions 10.1.85 and earlier on the official track and 10.2.93 and earlier on the release candidate track are confirmed vulnerable.
In practice, the most relevant exposed assets are self-hosted UniFi controller instances running on Linux or Windows servers where the management interface is reachable from untrusted networks. That includes controllers exposed directly to the internet, instances accessible through corporate DMZs or partner-connected environments, and containerized deployments where the network application port has been inadvertently published. UniFi OS devices such as the UniFi Express (UX) bundle the Network Application behind the OS portal and are also affected on firmware versions prior to 4.0.13.
The attack surface is broader than standalone controller servers. Web applications, partner portals, and remote-access infrastructure that route through UniFi-managed networks are indirectly within scope because compromising the controller affects every device it manages.
What does our data show about exposure patterns?
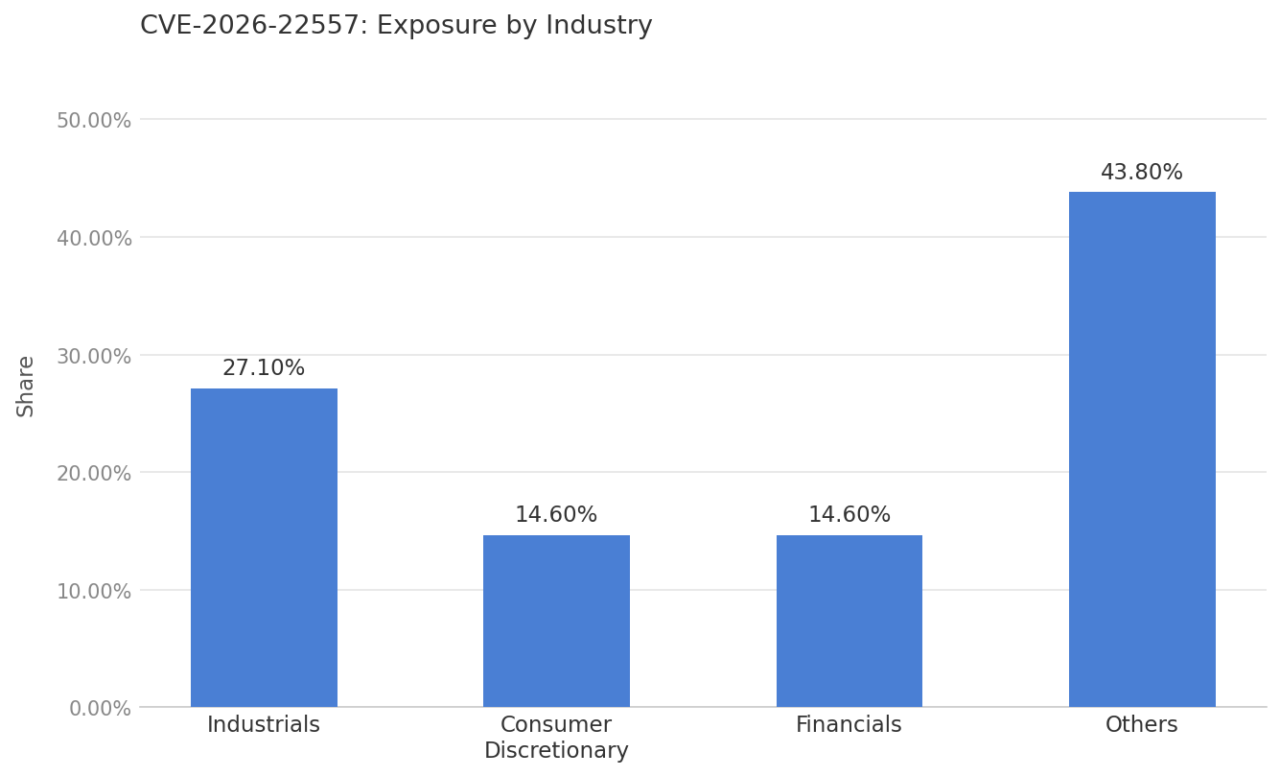
Exposure in this set is led by Industrials at 27.1% of observed assets, with Consumer Discretionary and Financials each contributing 14.6%.
The prominence of Industrials is consistent with environments that deploy distributed, site-connected network infrastructure at scale. Organizations in this sector commonly operate manufacturing facilities, logistics hubs, and operational technology environments where UniFi equipment is used to manage facility-level networking.
Controllers in those environments are frequently administered by IT teams that may not apply software updates on the same cadence as cloud-managed infrastructure, increasing the window in which vulnerable versions remain in service.
The presence of Financials alongside Industrials reflects how widely UniFi has been adopted beyond traditional small-business use cases. In both sectors, the relevant risk is not limited to directly exposed controllers — internet-facing applications and partner-accessible services backed by UniFi-managed infrastructure extend the effective attack surface considerably.
Across all sectors, the primary driver of exposure is the lack of visibility into where the UniFi Network Application is running and whether it is reachable from untrusted networks.
Are fixes available?
Yes. Ubiquiti released patches for CVE-2026-22557 as part of Security Advisory Bulletin 062, published March 18, 2026. The fixes are available now across all affected tracks.
For the official release, updating to UniFi Network Application version 10.1.89 or later remediates the vulnerability. For the release candidate track, version 10.2.97 or later is required. UniFi Express (UX) users should update to firmware version 4.0.13 or later, which bundles Network Application version 9.0.118 or later.
Ubiquiti has noted that updating through the standard Debian package repository may not deliver the most recent version; administrators running self-hosted instances on Linux should verify they are applying the update directly from the Ubiquiti download page rather than relying on package manager delivery alone.
Because the CVSS score is 10.0 and no authentication is required to exploit the vulnerability, organizations running affected versions — particularly those with internet-accessible controllers — should treat this as an emergency patch rather than a routine update cycle item.
Are there any other recommended actions to take?
Restrict access to the UniFi Network Application management interface so it is reachable only from trusted management networks or VPN-gated hosts, never directly from the internet. Apply network segmentation and firewall rules to isolate the controller from untrusted segments.
After patching, rotate credentials for all UniFi accounts and audit role assignments for unexpected privilege changes. Ubiquiti also recommends migrating self-hosted instances to UniFi OS-based hardware for improved security management going forward.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for CVE-2026-22557 in the CyCognito platform and is actively researching enhanced detection capabilities for this vulnerability.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



