



Practical guides, research, and insights to help security teams manage external exposure with clarity and control.
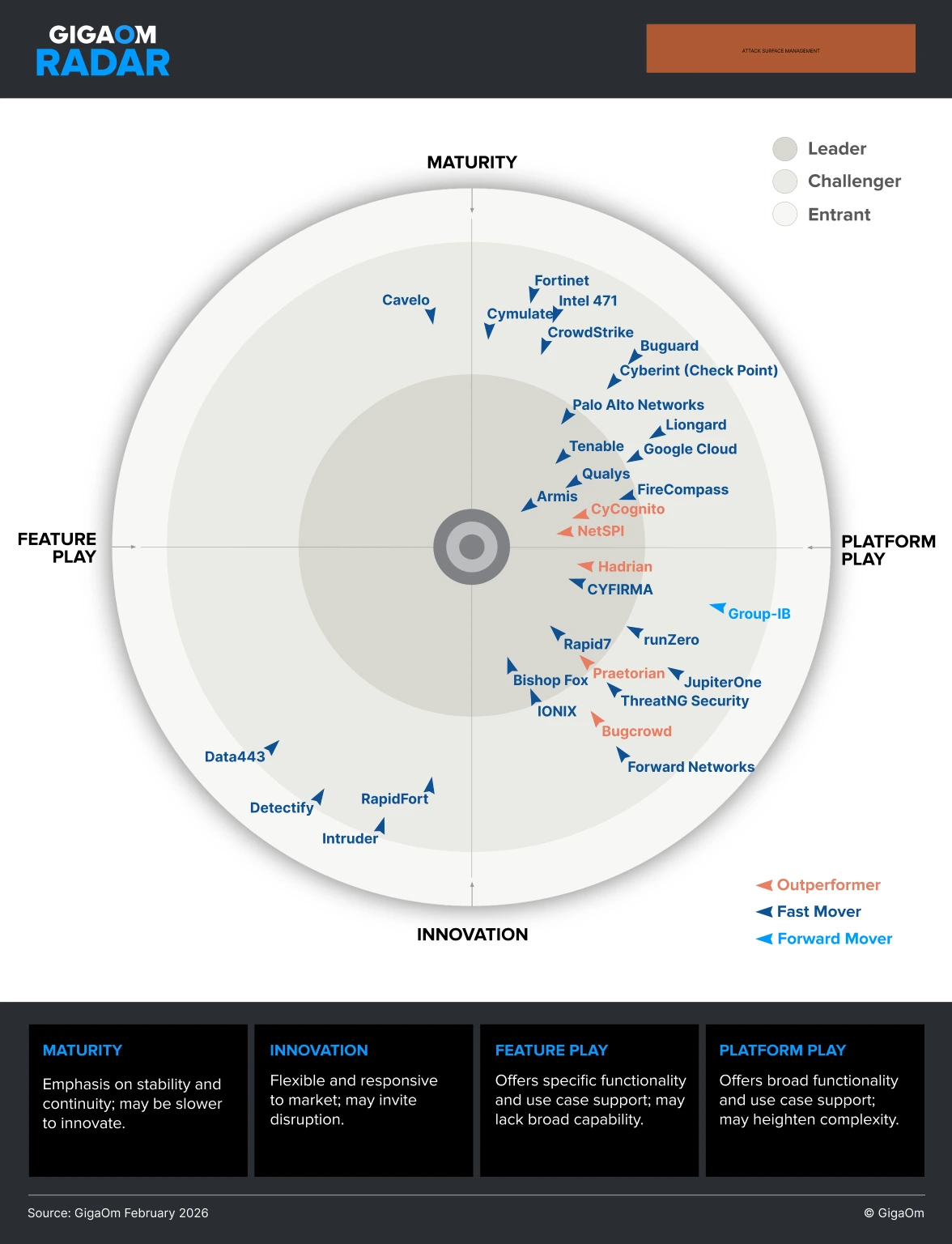
The expansion of an organization's attack surface continues to present a critical business challenge. Download the GigaOm Radar for Attack Surface Management to get an overview of the available ASM solutions, identify leading offerings, and evaluate the best solution for you.
Read more about GigaOm Radar for Attack Surface Management 2026
Download the report now to stay ahead of emerging threats and strengthen your organization’s security posture for 2024.
Read more about State of External Exposure Management, Summer 2024 Edition
The 2024 State of Web Application Security Testing report analyzes responses from hundreds of cybersecurity professionals in both the US and the UK, providing valuable insights into the current state of web application security testing.
Read more about 2024 State of Web Application Security Testing
Learn how leveraging automation through modern EASM technology can help bridge the gap between attackers and defenders, making it possible for defenders to improve their security and risk posture.
Read more about The State of External Attack Surface and Risk Management
Read The Total Economic Impact™ of The CyCognito Platform — a Forrester study. Cost Savings And Business Benefits Enabled By The CyCognito Platform.
Read more about The Total Economic Impact™ of The CyCognito Platform
Download this study to learn how to protect your most critical assets from being easily exploited by attackers as your enterprise expands to include more subsidiary brands and web applications.
Read more about External Risk Insights
Download the IDC EASM buyers guide and understand the key capabilities to look for when selecting an External Attack Surface Management solution with expert guidance and selection criteria from analyst firm IDC.
Read more about Attack Surface Management: The Foundation of Risk Management
Download the report to learn how modern External Attack Surface Management and CyCognito enable value across enterprise security and IT teams.
Read more about Benefits of External Attack Surface Management (EASM) Across Both Security and IT
Download Forrester Consulting’s thought leadership paper “Teamwork shines a light on hidden external risks” to uncover what your organization can do to improve its risk management strategy.
Read more about Teamwork Shines A Light On Hidden External Risk
Download this report to receive guidance intended to serve as a starting point for making the best security decision for each unique organization.
Read more about Advice on External Attack Surface Management (EASM) Selection: Pure Play vs. Bundled
Download the report to learn why security testing and attack surface monitoring work hand in hand.
Read more about Gaps in Attack Surface Monitoring and Security Testing for Cyber-risk Mitigation
What you don’t know can hurt your organization. Download the report to learn the dangers of subsidiary sprawl and other unknowns.
Read more about The Danger of Subsidiary Sprawl and Unknown Unknowns in External Attack Surface Management
Are your legacy vulnerability and asset management and penetration testing practices keeping your organization safe? Download the report to find out.
Read more about Security Hygiene and Posture Management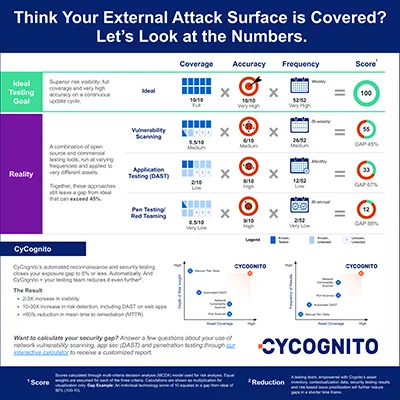
Organizations utilize vulnerability scanning, app security and pen testing. Despite this, it is easy to have a security testing gap of 45% from ideal.
Read more about Think Your External Attack Surface is Covered? Let’s Look at the Numbers.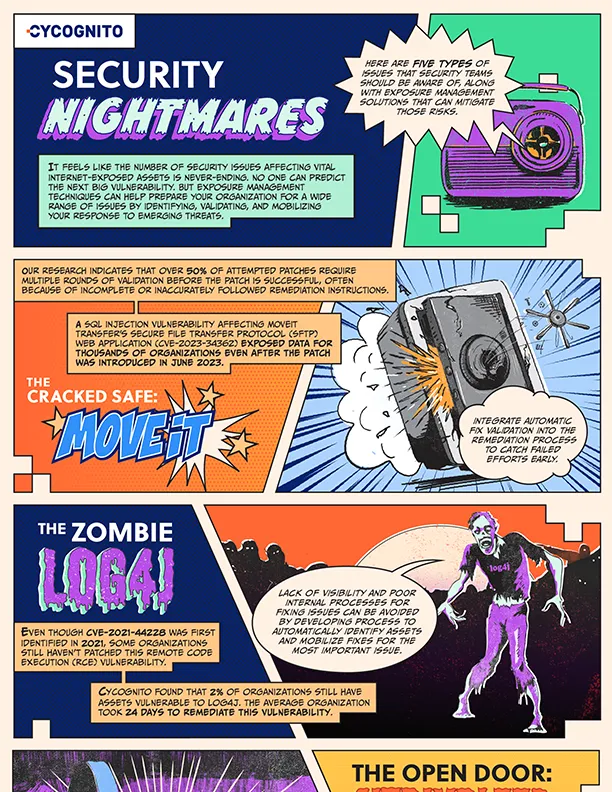
CyCognito shares insights showing how security teams can learn from previous incidents and leverage exposure management techniques to stay ahead of attackers.
Read more about Security Nightmares of 2023 and How to Avoid Them in 2024
Cyber Monday is filled with urgency, but cybercriminals take advantage of this urgency to exploit misconfigurations and vulnerabilities. This can cause massive reputational damage to inattentive organizations in the process.
Read more about Cyber Monday is Just Once a Year – Active Security Testing Shouldn’t Be