ESG Report
Security Hygiene and Posture Management
Manual processes based on asset management, vulnerability scanning and penetration testing — all tied together by spreadsheets — are not keeping your organization safe.
Download the report to see why it’s time to look for solutions that cut across silos and offer real risk prioritization and meaningful, continuous coverage of the external attack surface. ESG calls these Security Observability, Prioritization and Validation (SOPV) solutions.
Get the Report
By clicking submit, I acknowledge receipt of the CyCognito Privacy Policy.
It’s Time for a New Approach
There’s an urgent need for organizations to reassess how they do security hygiene and posture management to get a better, continuous view of the external attack surface, its security risks, and meaningful prioritization of those, and automate workflows to enhance collaboration between teams.
It’s past time to go beyond the spreadsheet!
Organizations need solutions to go beyond manual processes that try to glue together disparate legacy attack surface management, vulnerability scanning, and pen testing approaches. What’s required are solutions that offer:
- Coverage over more of the security hygiene and posture management stack
- Continuous coverage of the ever-evolving attack surface
- Automation to enable a more efficient use of resources and enhance collaboration between teams
- Meaningful prioritization of security risks
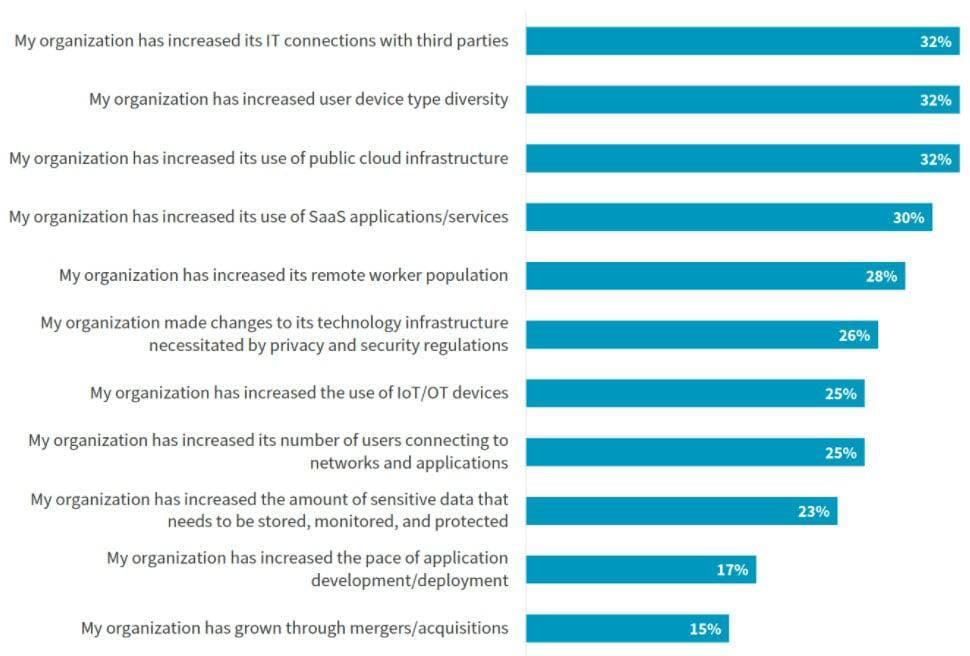
Primary Reasons Attack Surfaces have Increased