What is Attack Surface Management?
Attack surface management (ASM) is the continuous process of discovering, classifying, and monitoring all potential entry points in an organization’s environment that could be exploited by attackers. Attack surface management helps security teams maintain visibility over expanding and changing asset landscapes.
ASM solutions operate from both internal and external perspectives. External Attack Surface Management (EASM) emulates attacker reconnaissance, while internal ASM focuses on visibility and control inside the network. By providing a unified view of exposures, ASM enables organizations to respond faster to threats, reduce blind spots, and enforce security policies more effectively across all environments.
Modern ASM programs are guided by the Continuous Threat Exposure Management (CTEM) framework, which provides a structured approach to identifying and mitigating exposures across the attack surface. CTEM defines a continuous cycle of scoping, discovery, prioritization, validation, and mobilization, aligning closely with the ASM lifecycle. It emphasizes the need for exposure management to be threat-driven and risk-informed, ensuring that security efforts are focused on the most relevant and exploitable issues.
Why Is Attack Surface Management Important?
As IT environments grow more distributed and dynamic, maintaining visibility over all potential points of exposure becomes increasingly difficult. Attack surface management (ASM) helps security teams stay ahead of threats by identifying risks before they’re exploited.
Key reasons attack surface management is important:
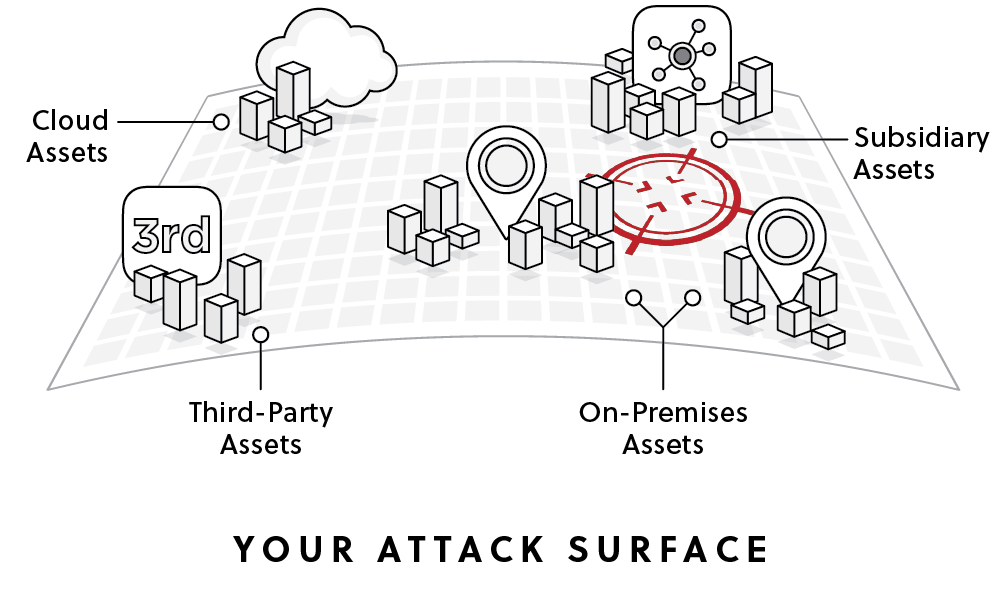
- Expanding asset footprint: Cloud adoption, remote work, and third-party integrations continuously introduce new, often unmanaged assets.
- Shadow IT and unknown assets: Employees or teams may deploy systems outside formal processes, creating blind spots for security teams.
- Continuous change: Environments evolve rapidly—assets appear, configurations drift, and new vulnerabilities emerge daily.
- Early threat detection: ASM helps identify exposed services, misconfigurations, or leaked credentials before attackers do.
- Prioritized remediation: By correlating exposure data with risk context, ASM enables teams to fix the most critical issues first.
- Compliance and governance: ASM supports audits and regulatory requirements by maintaining an up-to-date inventory and exposure map.
- Resilience against breaches: A well-managed attack surface reduces the number of exploitable paths, limiting the blast radius of successful intrusions.
The Attack Surface Management Process
Let’s review the ASM process, as guided by the CTEM framework.
1. Scope
The scope stage defines what the organization is trying to protect and why. It starts from business risk rather than technical findings. This means identifying critical services, applications, and data, and understanding how an attack would impact them.
Security teams set boundaries for which assets, environments, and attack surfaces will be assessed. They also define risk scenarios tied to business outcomes, align goals with regulatory needs, and document assumptions and constraints. This ensures the rest of the process focuses on what matters most to the organization.
2. Discovery
Asset discovery is a continuous process that identifies assets, exposures, and security gaps within the defined scope. It covers both internal and external environments, including cloud, on-premises, and SaaS systems.
Teams inventory internal and external assets, detect vulnerabilities and misconfigurations, and map how systems are exposed to attackers. This stage also includes threat modeling to connect technical findings with attacker behavior. Instead of isolated issues, discovery builds a view of possible attack paths and how adversaries could reach critical assets.
3. Prioritization
Prioritization determines which exposures require action based on real risk. Instead of relying only on severity scores, it considers exploitability, attacker reach, and business impact.
Security teams rank findings by how likely they are to be used in an attack and the damage they could cause. This reduces large volumes of issues into a focused list of actions. Ownership, urgency, and remediation feasibility are also defined to ensure teams can act efficiently.
4. Validation
Validation confirms whether identified exposures are actually exploitable. It uses adversarial testing methods such as simulation or automated penetration testing to verify real-world risk.
This step helps distinguish between theoretical vulnerabilities and those that can be used in practice. It also evaluates existing security controls, measures detection and response capabilities, and reduces false positives. The result is a clearer understanding of actual attack paths and potential impact.
5. Mobilization
Mobilization turns validated findings into concrete remediation actions. This includes patching systems, fixing misconfigurations, and implementing new controls.
Actions are assigned to responsible teams and tracked over time to ensure progress. Remediation is continuous, not one-time, as new exposures emerge. Results from this stage feed back into earlier stages, improving future scoping, asset discovery, and prioritization efforts.

Operationalizing CTEM Through External Exposure Management
CTEM breaks when it turns into vulnerability chasing. Too many issues, weak proof, and constant escalation…
This whitepaper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.

Types of Attack Surface Management Tools
External Attack Surface Management (EASM)
External attack surface management focuses on identifying and securing digital assets exposed to the public internet. These are the assets attackers can see and target without any internal access, making them high-priority vectors.
Common components of the external attack surface include:
- Public-facing web applications and APIs
- Domains, subdomains, and associated DNS records
- Cloud storage buckets and content delivery networks (CDNs)
- Email servers and marketing platforms
- SSL/TLS certificates and misconfigured HTTPS endpoints
- Developer environments, staging servers, or admin panels exposed externally
External attack surface management solutions typically rely on passive and active discovery techniques to emulate attacker reconnaissance. This includes DNS and IP space scanning, certificate transparency analysis, web crawling, and leveraging open-source intelligence (OSINT) to map the organization’s digital footprint.
Because external assets can be spun up by multiple teams, contractors, or M&A activity, many are unknown to security, making shadow IT, legacy systems and other kinds of unknown or forgotten assets a major focus of EASM. These tools provide continuous discovery to catch changes like new subdomains, exposed ports, or leaked credentials in real time.
Internal Attack Surface Management
Internal attack surface management focuses on identifying, assessing, and monitoring internet facing assets and exposures that exist inside an organization’s network perimeter. While external ASM looks at what attackers can see from the outside, internal ASM addresses internal risks—often those that become critical during lateral movement in post-compromise scenarios.
This includes systems behind the firewall, internal APIs, development environments, shared file systems, network infrastructure, and endpoint devices. It also covers misconfigurations, legacy systems, excessive permissions, and unmonitored communications that can be leveraged by attackers once inside.
Internal attack surface management solutions typically integrate with endpoint detection and response (EDR), vulnerability management platforms, and identity systems. They also use techniques like agent-based scans, log analysis, and configuration reviews to detect gaps that may not be visible externally.
CSPM
Cloud security posture management (CSPM) is a class of tools that continuously assess cloud infrastructure for security misconfigurations and compliance violations. As cloud environments grow more complex, CSPM helps enforce security best practices and detect risks caused by drift, misconfigured services, or overly permissive access.
CSPM tools integrate with cloud service providers’ APIs to analyze infrastructure-as-code (IaC), service configurations, network settings, identity and access policies, and logging practices. They identify issues such as exposed S3 buckets, open security groups, disabled logging, and unencrypted storage.
Most CSPM solutions provide predefined policy checks aligned with standards like CIS Benchmarks, NIST, or PCI-DSS, as well as the ability to customize policies for internal governance. Findings are prioritized based on risk severity and compliance impact, and remediation guidance is often built-in or automated.
DRPS
Digital risk protection services (DRPS) help security teams detect and respond to external threats that originate outside their managed infrastructure. These threats include brand impersonation, credential leaks, phishing campaigns, exposed data, and malicious mentions on the dark web or social media.
DRPS platforms use a combination of open-source intelligence (OSINT), dark web monitoring, and threat intelligence feeds to discover risks associated with an organization’s digital presence. This may include rogue domains, cloned websites, leaked employee credentials, or stolen data for sale.
Once attack vectors are identified, DRPS tools support response actions such as takedown requests, domain blocking, or alerting affected users. Some solutions also integrate with security operations centers (SOCs) or incident response platforms for faster remediation.
Identity Attack Surface Management (IASM)
Identity attack surface management focuses on securing identities and access paths that attackers commonly exploit to gain initial access or escalate privileges. This includes user accounts, service accounts, roles, credentials, and authentication mechanisms across on-premises and cloud environments.
IASM examines how identities are created, managed, and used. It identifies risks such as excessive permissions, dormant accounts, weak authentication policies, credential exposure, and misconfigured identity federation. It also maps relationships between identities and resources to uncover privilege chains that could enable lateral movement.
These tools integrate with identity providers (IdPs), directory services, and access management platforms to collect data on authentication activity, role assignments, and policy enforcement. They often use graph-based analysis to model identity relationships and detect risky access paths that are not obvious in isolation.
Cyber Asset Attack Surface Management (CAASM)
Cyber asset attack surface management focuses on providing visibility into all known and unknown assets, across an organization’s environment, regardless of where they reside. Unlike EASM, which looks outward, CAASM aggregates internal data to help security teams understand what exists, what’s at risk, and where gaps in coverage or controls may be.
CAASM solutions ingest data from existing tools such as CMDBs, EDRs, cloud platforms, vulnerability scanners, identity providers, and configuration management databases. The goal is not to replace these tools, but to unify their outputs into a centralized view that supports asset inventory, risk prioritization, and remediation workflows.
Key use cases include:
- Building an up-to-date, queryable inventory of all digital assets
- Identifying security gaps (e.g., unmanaged systems, missing agents, unscanned assets)
- Correlating vulnerabilities with asset context (ownership, criticality, exposure)
- Enabling faster incident response by connecting assets with their owners and telemetry
- Monitoring for changes across environments, including ephemeral assets
CAASM is especially valuable in complex, cloud-native, and hybrid environments where internet facing assets assets are dynamic and distributed. It helps answer foundational questions like “What do we own?”, “Is it secured?”, and “Is it being monitored?”, which are essential for reducing risk and improving security operations.Learn more in our detailed guide to attack surface management tools
Tips from the Expert

Dima Potekhin, CTO and Co-Founder of CyCognito, is an expert in mass-scale data analysis and security. He is an autodidact who has been coding since the age of nine and holds four patents that include processes for large content delivery networks (CDNs) and internet-scale infrastructure.
In my experience, here are tips that can help you better operationalize and mature attack surface management beyond the basics:
- Treat ephemeral assets as first-class citizens: Most attack surface management programs still miss short-lived external assets (e.g., containers, preview environments). Tap into CI/CD pipelines and infrastructure events (like Kubernetes API or cloud audit logs) to capture assets at creation time.
- Build an “asset confidence score”: Not all discovered assets are equal. Assign confidence levels based on discovery source (e.g., DNS + TLS + HTTP fingerprint = high confidence). This helps reduce time wasted chasing false positives or misattributed assets.
- Demand exploitability evidence, not detection lists: Most tools report what they observe: a service version, a configuration flag, a matched signature. That’s assumed issue, not validated risk. A capable ASM program actively tests exposed assets to simulate attack scenarios and validate exploitability, so findings arrive as verified findings rather than research assignments.
- Use attacker path choke points instead of asset criticality alone: Rather than only prioritizing crown jewels, identify “choke points” (e.g., SSO portals, VPN gateways, shared APIs). Weaknesses here often collapse multiple attack paths at once.
- Continuously diff your attack surface: Track deltas (what’s new, changed, or disappeared) between scans. New exposures are disproportionately risky because they haven’t been hardened or reviewed; this is where attackers win.
- Map “ownership drift” as a risk signal: When digital assets lack clear ownership, or ownership frequently changes, it’s often a leading indicator of poor maintenance and higher vulnerability density. Treat this as a prioritization factor.
Use Cases of Attack Surface Management
Securing Web Applications
ASM helps secure web applications by discovering all external facing assets (e.g., exposed apps and APIs) including those not tracked in internal inventories. It uses continuous black-box testing to identify and actively validate for security issues such as common web vulnerabilities, exposed data, and authentication weaknesses.
It also maps the full application footprint from an attacker’s perspective, including shadow apps, forgotten environments, and orphaned pages. Continuous testing runs across many categories of weaknesses, ensuring issues are identified as soon as they appear rather than during periodic scans.
Beyond detection, ASM reviews the security posture and validates whether controls actually work in real conditions. Findings are prioritized based on business context, such as applications handling sensitive data, helping teams focus on the exposures that create the most risk.
Cloud Security
Attack surface management extends cloud security by adding an outside-in perspective that reveals assets and exposures not visible through cloud provider APIs. It identifies unknown or unmanaged cloud resources and shows how they are exposed to the internet.
It also highlights the paths attackers are most likely to take by identifying which cloud assets are easiest to discover and access. This provides a clearer picture of real attack paths rather than isolated misconfigurations.
Continuous testing validates whether detected cloud issues are exploitable in practice. By combining reachability, asset context, and criticality, ASM helps teams prioritize the cloud risks that have real-world impact instead of relying only on configuration findings.
Vulnerability Management
Attack surface management improves vulnerability management by focusing on exploitable risk rather than large volumes of theoretical findings. It combines external discovery with active testing to confirm which vulnerabilities can actually be used by attackers.
This reduces alert noise significantly by filtering out issues that are not reachable or exploitable. Instead of long lists of CVEs, teams get a small, prioritized set of validated risks that require action.
ASM also maps how vulnerabilities connect across digital assets, showing real attack paths. This allows teams to fix issues in a way that breaks multiple paths at once, improving remediation efficiency and reducing overall risk faster.
Shadow IT and Managed Services
Attack surface management covers assets that organizations are not aware of, including shadow IT, unmanaged services, and systems introduced by subsidiaries or third parties. It uses continuous discovery to find assets without relying on predefined inputs.
This includes cloud resources, web applications, and external services that may sit outside traditional asset inventories. Many of these assets are created by different teams or vendors and are often left unmonitored.
By mapping these assets back to the organization and identifying ownership, ASM provides the context needed to take action. This helps bring unknown assets under governance and reduces the risk of hidden exposure.
Support for Ethical Hacking and Penetration Testing
Attack surface management supports ethical hacking by replacing point-in-time testing with continuous, automated security testing. It combines reconnaissance and validation to simulate attacker behavior on an ongoing basis.
With large-scale automated testing coverage, ASM can continuously assess a wide range of weaknesses across the attack surface. This provides broader and more consistent coverage than periodic manual testing.
As a result, organizations can reduce reliance on repeated pentests and bug bounty efforts. Security teams and ethical hackers can instead focus on deeper, high-value scenarios that require human expertise.
Third-Party and Supply-Chain Risk Mitigation
Attack surface management helps identify risks in third-party software, open-source components, and external dependencies. It continuously monitors applications and assets to detect vulnerable or misconfigured components.
It provides visibility into dependencies across the organization, including those introduced through subsidiaries or external partners. This is critical, as many organizations rely on a large number of third parties that can introduce risk.
By combining deep asset discovery with active exploitability validation, ASM identifies weak links in the supply chain and validates their impact. This allows teams to prioritize and address risks before they are exploited in real attacks.
Adversarial Exposure Validation (AEV)
AEV continuously emulates attacker tactics, combining automated penetration testing, breach and attack simulation, and red team techniques, to confirm which weaknesses in an organization’s environment can actually be exploited, rather than which ones theoretically match a known pattern.
The practical consequence is a dramatic compression of the finding list. Active testing filters out the majority of issues that passive scanning flags as critical but that real-world conditions render unexploitable — organizations typically see what appears critical drop from roughly 25% of findings to under 1% (and as low as 0.1%) once exploitability is confirmed. What remains is mapped to specific attack paths and business context, so remediation teams are acting on verified risk rather than probability estimates.
AEV also changes the cadence of security testing. Because validation runs continuously, a new service or configuration change is tested as it appears — not in the next scheduled engagement. Organizations that previously relied on annual or quarterly penetration tests to answer “can this actually be exploited?” now have that answer updated in near real-time as the environment changes.
Security Controls Validation
Attack surface management validates whether security tools are functioning, running active security tests against to confirm controls perform as configured against real-world attack vectors. This includes controls like WAFs, authentication systems, and access restrictions.
Instead of assuming protection based on configuration, ASM verifies how controls behave when exposed to actual attack techniques. This helps identify gaps in coverage or misconfigurations that reduce effectiveness.
Continuous validation ensures that controls remain effective as the environment changes. It provides clear evidence of where protections are working and where additional action is needed.
M&A and Subsidiary Risk
Attack surface management provides immediate visibility into the security posture of acquisition targets and subsidiaries. It maps their external attack surface, identifies exposed assets, and evaluates risk without requiring deployment.
It builds a structured view of the organization, including business units and associated assets, allowing teams to understand what they are acquiring. Risk can be compared across entities to quickly identify problem areas.
ASM also provides validated findings with clear remediation steps and ownership context. This enables informed decision-making during due diligence and supports faster integration and risk reduction after acquisition.
Cyber Insurance Premium Reduction
Attack surface management contributes to improved risk posture by continuously identifying, validating, and reducing exploitable exposures. It provides a quantified and prioritized view of risk across the attack surface.
By focusing on verified issues and tracking remediation progress, organizations can demonstrate measurable improvements in their security posture. This includes reducing critical findings and shortening remediation timelines.
This level of evidence and continuous monitoring supports stronger risk assessments. It helps organizations communicate their security maturity and exposure reduction to insurers more effectively.
Compliance and Governance
Attack surface management supports compliance by maintaining an up-to-date inventory of exposed assets and continuously testing them against security requirements. It provides visibility into where assets exist and how they are exposed.
Findings are mapped to relevant frameworks and standards, linking each issue to specific controls and evidence requirements. This simplifies understanding of compliance gaps and required actions.
Automated evidence collection and continuous monitoring reduce manual effort during audits. Teams can track progress over time, prioritize the most important issues, and approach audits with a clear and current view of their compliance posture.
Key Challenges of Attack Surface Management
Incomplete Starting Points
Many ASM programs begin with incomplete or outdated inventories. Relying on internal CMDBs or manual documentation often misses assets deployed outside traditional channels, especially in fast-moving environments with cloud services, contractors, and DevOps pipelines.
Without a comprehensive baseline, asset discovery tools may not cover all domains, IP ranges, or business units. This leads to blind spots where risks go undetected. An effective ASM program must account for the likelihood that security teams don’t know everything they own, and design discovery processes accordingly.
Rapid Attack Surface Changes
Modern IT environments change constantly. Cloud resources spin up and down, new services are deployed, and developers push code multiple times per day. These rapid shifts make static or periodic assessments insufficient.
If ASM can’t keep pace with these changes, newly introduced risks may remain undetected until exploited. Continuous monitoring and automated discovery are critical to identify exposures in near real-time and prevent outdated attack surface views from creating gaps in protection.
Fragmented Environment
Organizations often operate across multiple environments, on-premises, public cloud, private cloud, SaaS platforms, and remote endpoints. Each environment has its own tools, configurations, and visibility challenges.
This fragmentation complicates discovery and analysis. Assets may be duplicated across tools, inconsistently labeled, or monitored with varying levels of fidelity. ASM must integrate diverse data sources and normalize them to present a coherent and accurate view of the attack surface.
Unclear Ownership
When an exposure is discovered, it’s not always obvious who is responsible for fixing it. Both internal and external assets may be owned by different teams, contractors, or subsidiaries, some of whom may not be aware the asset exists at all.
Lack of clear ownership delays remediation and increases dwell time for risks. Effective ASM tools need to correlate internet facing assets with business context, such as system owners or business units—and enable fast routing of issues to the right teams.
Too Much Noise Due to Lack of Validation
ASM can produce large volumes of findings, especially during early deployment. Without proper validation, many of these may be false positives or low-impact issues, overwhelming teams and diluting focus.
Automated validation helps confirm which findings are actually exploitable. This reduces noise and prioritizes real risks. ASM solutions must filter out non-actionable issues and focus attention on exposures that attackers can realistically exploit.
Hard-to-Verify Remediation
Fixing an exposure doesn’t always mean it’s gone. Teams may patch a system or change a configuration, but verifying that the fix worked and closed the attack path can be difficult.
ASM should re-test exposures after remediation to confirm they’re no longer exploitable. This feedback loop is essential for maintaining confidence in fixes and demonstrating progress. Without verification, the same issues can reappear or remain exploitable without detection.
Best Practices for Effective Attack Surface Management
Take the Attacker’s Perspective
Effective ASM starts by viewing your environment the way an attacker would. This means looking externally first, identifying exposed digital assets without relying on internal documentation or assumptions. Discovery should mimic attacker reconnaissance, using passive and active techniques to map your internet-facing footprint.
This perspective helps uncover shadow IT, forgotten environments, and misconfigurations that may not appear in internal inventories. It also highlights unintended exposure, such as test systems, backup interfaces, or misconfigured access controls that attackers often exploit first.
Adopting an attacker’s mindset also improves decision-making. Instead of asking “what is vulnerable,” teams ask “what is reachable and exploitable.” This shift leads to more realistic risk assessments and better alignment with how real-world attacks are executed.
Continuous Cadence
Static or periodic assessments can’t keep up with the pace of change in modern environments. ASM should operate on a continuous, automated cadence, constantly discovering assets, validating exposures, and updating risk data as changes occur.
This ensures that newly introduced risks are detected quickly and don’t remain unnoticed between scheduled scans. For example, a newly deployed cloud service or exposed API can be identified and assessed within minutes rather than weeks.
A continuous cadence also improves trend analysis. Security teams can track how the attack surface evolves over time, measure the impact of remediation efforts, and identify patterns such as recurring misconfigurations or risky deployment practices.
Risk-Based Prioritization
Not all exposures are equal. ASM tools should prioritize issues based on context, not just severity scores. This includes factors like exploitability, attacker reachability, business criticality of the asset, and existing compensating controls.
For example, a medium-severity vulnerability on a public-facing system may pose more risk than a critical issue on an isolated internal asset. Risk-based prioritization accounts for these differences and ensures decisions reflect real-world conditions.
This approach reduces alert fatigue and helps teams focus on actionable findings. By narrowing thousands of potential issues into a small set of high-impact risks, organizations can respond faster and allocate resources more effectively.
Prioritized Risk Reduction
ASM is not just about visibility; it’s about reducing the attack surface. This means defining and executing a strategy for fixing validated, high-impact exposures in a structured and measurable way.
Prioritized risk reduction focuses on exposures that close multiple attack paths, affect critical systems, or are likely to be exploited. In many cases, fixing a single misconfiguration or exposed service can eliminate several downstream risks at once.
This practice also emphasizes measurable outcomes. Instead of tracking the number of vulnerabilities, teams track reduction in exploitable paths, exposure time, and overall risk posture. This provides a clearer picture of security improvement over time.
Full-Cycle Remediation Management
Discovery alone doesn’t improve security unless it’s tied to actionable remediation. ASM best practices include assigning ownership, tracking status, and verifying fixes across the full lifecycle of an exposure—from detection to closure.
This requires integration with ticketing systems, clear workflows for routing issues to responsible teams, and defined SLAs for remediation. Without these elements, findings can remain unresolved or be repeatedly rediscovered.
Automated retesting plays a key role in this cycle. After a fix is applied, ASM should confirm that the exposure is no longer exploitable. This closes the loop, prevents regression, and builds confidence that remediation efforts are effective.
Holistic/Integrated Approach
ASM works best when integrated with the broader security ecosystem. This includes combining data from vulnerability management, cloud security, identity systems, and asset inventories to get a complete view of risk.
A fragmented approach leads to blind spots and duplicated effort. Integration allows teams to correlate findings across tools, enrich them with context, and understand how different risks connect across the environment.
It also improves collaboration. By linking technical findings to business context, such as asset ownership, application purpose, or data sensitivity, ASM enables security, IT, and development teams to work from a shared understanding of risk. This alignment is essential for scaling security operations in complex environments.
Attack Surface Management with CyCognito
Managing an attack surface that spans cloud environments, subsidiaries, shadow IT, and third-party infrastructure requires more than continuous discovery — it requires knowing which of those assets carry weaknesses an attacker can actually use. CyCognito is a leading ASM platform that continuously discovers your full external footprint and actively validates exploitability across every asset it finds, starting from nothing more than your organization’s name.
- Discovers assets across cloud, on-premises, subsidiaries, and shadow IT without seeds, agents, or prior asset lists — finding what internal inventories structurally miss
- Maps every discovered asset to its business owner and environment so findings route to the right team immediately, not into a backlog nobody owns
- Actively validates exploitability on every discovered asset through continuous testing — reducing what appears critical from roughly 25% of findings to 0.1% confirmed as actually exploitable
- Prioritizes using attacker reachability, business context, and attack path analysis — not CVSS scores alone — so remediation effort concentrates where risk is real
- Tracks findings from discovery through verified fix, with integrations into ticketing and IT workflows, closing the loop between what is found and what is resolved
CyCognito typically uncovers an attack surface up to 20x larger than previously inventoried — then continuous validation reduces that universe to the 0.1% of findings confirmed as actually exploitable.If you want to see CyCognito in action, click here to schedule a 1:1 demo.














