What are CVE-2026-3055 and CVE-2026-4368?
On March 23, 2026, Cloud Software Group (Citrix) published a security bulletin disclosing two vulnerabilities in NetScaler ADC (formerly Citrix ADC) and NetScaler Gateway (formerly Citrix Gateway). Both affect customer-managed on-premises deployments; Citrix-managed cloud services and Adaptive Authentication instances have been updated automatically.
CVE-2026-3055 is an out-of-bounds read resulting from insufficient input validation in NetScaler ADC and NetScaler Gateway. With a CVSS v3.1 score of 9.3 and an attack vector of AV:N/AC:L/PR:N/UI:N, the flaw requires no authentication and no user interaction to trigger.
Exploitation is contingent on the appliance being configured as a SAML Identity Provider (SAML IDP); default configurations are not affected. A successful attack allows an unauthenticated remote attacker to read sensitive content from the appliance's memory — including, under some conditions, active session tokens — without executing arbitrary code on the device.
CVE-2026-4368 is a race condition carrying a CVSS v3.1 score of 7.7. It affects appliances configured as a Gateway (SSL VPN, ICA Proxy, CVPN, or RDP Proxy) or as an AAA virtual server, and is additionally constrained to build version 14.1-66.54.
The flaw can cause user session mix-up: under the right timing conditions, an authenticated session may be associated with the wrong user's context. This can translate to unauthorized access to another user's resources or authenticated state, without requiring the attacker to hold elevated privileges.
Neither vulnerability has confirmed in-the-wild exploitation or a publicly available proof-of-concept as of the date of this writing. CVE-2026-3055 was identified internally by Citrix during a security review. However, the low attack complexity and the pattern established by prior NetScaler memory-read vulnerabilities — including CVE-2023-4966 ("CitrixBleed") and CVE-2025-5777 ("CitrixBleed2"), both of which saw rapid weaponization after disclosure — make timely remediation a priority.
What assets are affected by CVE-2026-3055 and CVE-2026-4368?
Both vulnerabilities affect NetScaler ADC and NetScaler Gateway versions 14.1 before 14.1-66.59, 13.1 before 13.1-62.23, and 13.1-FIPS / 13.1-NDcPP before 13.1-37.262. CVE-2026-4368 carries an additional constraint: it only affects build version 14.1-66.54 specifically.
NetScaler ADC is a widely deployed application delivery controller used to improve performance, availability, and security of enterprise applications. NetScaler Gateway is the remote access component, providing SSL VPN and identity brokering for internal applications. Both products are commonly positioned at the network edge, directly internet-facing, and frequently configured to handle authentication traffic — including SAML federation and single sign-on workflows that serve as the precise configuration trigger for CVE-2026-3055.
Deployments spanning hybrid environments, partner integrations, and legacy network segments are especially common in sectors with distributed infrastructure. SAML IDP configuration, which is required for CVE-2026-3055 to be exploitable, is a standard setup for organizations using centralized identity providers, making the affected population larger than the default-configuration caveat might initially suggest.
Organizations can verify whether their appliances are in scope by inspecting the NetScaler configuration for add authentication samlIdPProfile (CVE-2026-3055) or add vpn vserver / add authentication vserver (CVE-2026-4368).
What does our data show about exposure patterns?
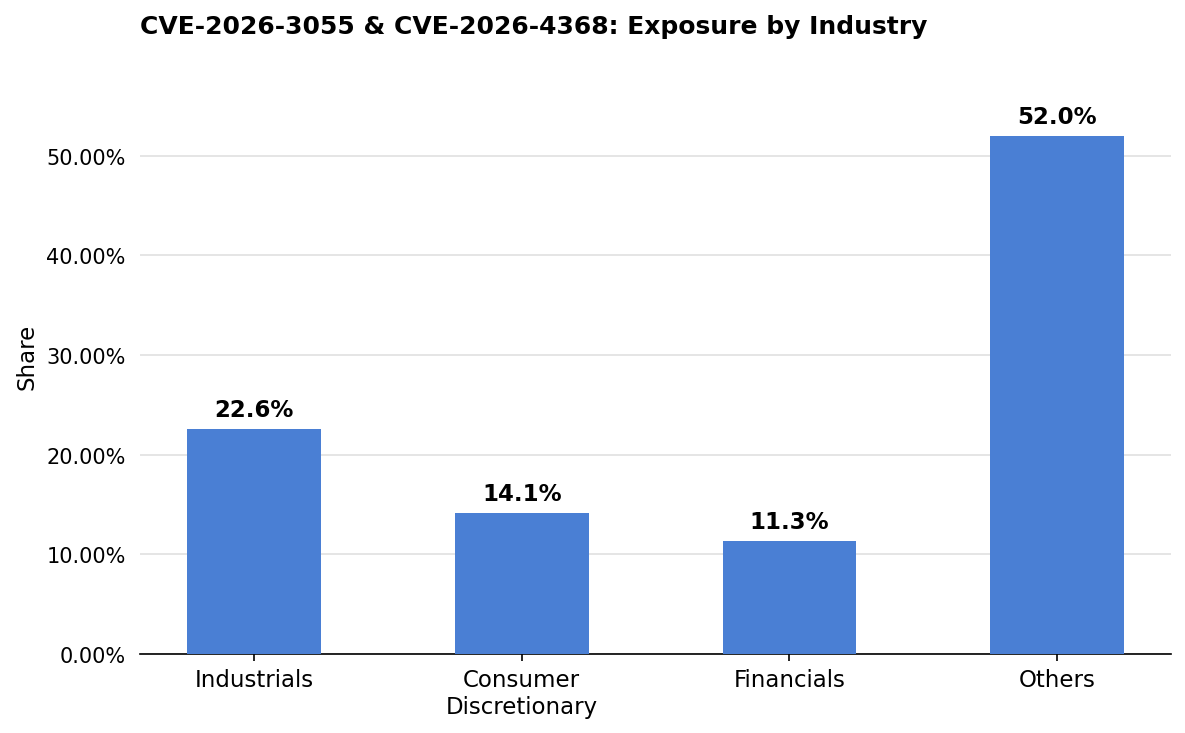
Exposure in this set is led by Industrials at 22.6% of observed assets, with Consumer Discretionary contributing 14.1%.
Industrial organizations — spanning capital goods manufacturers, logistics providers, commercial services firms, and professional services operations — tend to operate distributed networks with many distinct business units, partner integrations, and geographically dispersed sites. These characteristics support wide deployment of application delivery controllers and remote access gateways to normalize connectivity across diverse infrastructure, which in turn creates a broad footprint of NetScaler assets.
The combination of long hardware refresh cycles and multi-vendor complexity in industrial environments also means that version currency lags more than it does in pure-software sectors.
The cross-sector spread — with Financials, Health Care, and Information Technology each accounting for meaningful shares of observed assets — reflects the degree to which NetScaler ADC and Gateway have become standard infrastructure across enterprise environments.
The high "Others" share points to additional exposure in sectors not captured by the top GICS buckets, suggesting that no vertical has fully consolidated its edge authentication infrastructure or eliminated aging NetScaler deployments from its attack surface.
Are fixes available?
Patches are available. Cloud Software Group released fixed builds on March 23, 2026, as part of security bulletin CTX696300. The patched versions are 14.1-66.59, 13.1-62.23, and 13.1-NDcPP 13.1-37.262. Organizations running any version of NetScaler ADC or NetScaler Gateway in the affected ranges should upgrade to one of these builds immediately.
CVE-2026-4368 affects only build 14.1-66.54, which means organizations on earlier 14.1 builds that have not yet advanced to 14.1-66.54 are not exposed to that specific flaw — but they remain in scope for CVE-2026-3055 if they fall below 14.1-66.59. The practical guidance is to move directly to the latest fixed build regardless of current version.
Citrix-managed cloud services and Adaptive Authentication are already updated. Defender teams should not assume patch availability based on advisory databases alone, as status can vary by deployment type and version. Organizations should verify their exact build version and consult the Citrix bulletin directly to confirm the appropriate upgrade path.
Are there any other recommended actions to take?
Organizations should verify whether internet-facing NetScaler appliances are configured as SAML IDP or as a Gateway/AAA virtual server, and prioritize those for immediate upgrade. Until patching is complete, restricting network-level access to management interfaces and minimizing exposure of the appliance to untrusted networks can reduce the attack surface. Session activity on affected appliances should be monitored for anomalous behavior, particularly any signs of session token reuse or unexpected session context switching that could indicate exploitation of CVE-2026-4368.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for CVE-2026-3055 and CVE-2026-4368 in the CyCognito platform and is actively researching enhanced detection capabilities for these vulnerabilities.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



