What is CVE-2025-53521?
CVE-2025-53521 is an unauthenticated remote code execution vulnerability in F5's BIG-IP Access Policy Manager (APM). The flaw exists in the apmd process, the daemon responsible for processing live access policy traffic, and is triggered when a BIG-IP APM access policy is configured on a virtual server and the system receives specific malicious traffic. No credentials are required to exploit it.
The vulnerability carries a CVSS score of 9.8 and a CVSS score of 9.3. These scores reflect a pre-authentication attack requiring no user interaction and no special conditions on the attacker's side.
Successful exploitation enables an attacker to execute arbitrary code on the affected system. From that position, an attacker can establish persistence, deploy backdoors or webshells, move laterally into the internal network, and exfiltrate data accessible from the compromised segment. BIG-IP systems deployed in Appliance mode are also affected. The vulnerability is classified under CWE-770 (Allocation of Resources Without Limits or Throttling).
CVE-2025-53521 was initially disclosed on October 15, 2025, and classified as a denial-of-service issue. In March 2026, F5 reclassified it as a remote code execution vulnerability after new information became available.
F5 confirmed the vulnerability has been exploited in affected BIG-IP versions and has published indicators of compromise, including suspicious files, log anomalies, and HTTP/S traffic patterns associated with post-exploitation activity. CISA added the flaw to its Known Exploited Vulnerabilities catalog on March 27, 2026, and ordered US federal civilian agencies to remediate by March 30, 2026.
What assets are affected by CVE-2025-53521?
The vulnerability affects F5 BIG-IP APM across four version branches: 17.5.0 through 17.5.1, 17.1.0 through 17.1.2, 16.1.0 through 16.1.6, and 15.1.0 through 15.1.10. Systems running BIG-IP APM with an access policy configured on a virtual server are in scope; BIG-IP deployments without APM or without an access policy on a virtual server are not directly affected by this vulnerability. Appliance mode configurations are explicitly confirmed as vulnerable.
In practice, affected assets are enterprise-grade network appliances positioned at the perimeter or in front of application infrastructure. BIG-IP APM is commonly deployed to broker authentication and access for corporate VPNs, web application portals, APIs, and remote workforce access systems. These systems are routinely internet-facing by design — their purpose is to mediate external user access to internal resources — which makes them a high-value target for opportunistic and targeted attackers alike.
The reclassification from DoS to RCE, combined with a known prior compromise of F5's internal environment by a nation-state actor with access to BIG-IP source code, elevates the risk profile of any unpatched deployment.
Organizations that deprioritized remediation based on the original DoS classification may have left internet-exposed BIG-IP APM systems unpatched for an extended period. Internet-wide scanning for the BIG-IP REST API endpoint /mgmt/shared/identified-devices/config/device-info has been observed following CISA's KEV listing, indicating active reconnaissance activity in progress.
What does our data show about exposure patterns?
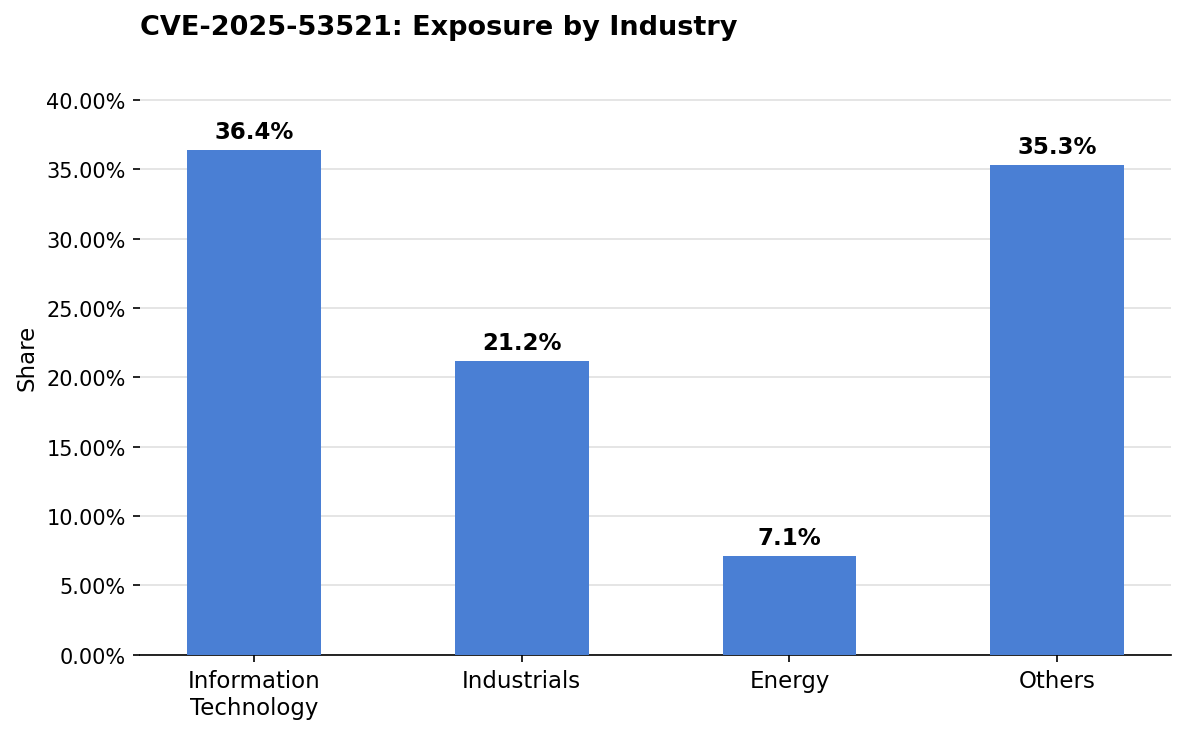
Exposure in this set is led by Information Technology at 36.4% of observed assets, with Industrials contributing 21.2%.
The Information Technology concentration is consistent with the role BIG-IP APM plays in enterprise access infrastructure. Software and services companies — along with technology hardware vendors — routinely deploy BIG-IP to secure developer portals, SaaS environments, customer-facing APIs, and internal tooling.
These environments tend to maintain a high volume of virtual servers and access policies, increasing the surface area of affected deployments. At the same time, distributed development teams and multi-cloud architectures can introduce delays between patch availability and verified remediation across all deployed instances.
The cross-sector spread, particularly the proportion falling into the Others bucket, reflects a pattern common to widely-deployed enterprise infrastructure: BIG-IP APM is not sector-specific. Organizations that acquired or inherited these deployments through mergers, partner integrations, or cloud migrations may have reduced visibility into whether access policies are configured on all virtual servers, or whether affected version branches remain in production.
Are fixes available?
Patches are available. F5 released fixes for CVE-2025-53521 as part of its October 2025 Quarterly Security Notification. The fixed versions are 17.5.2, 17.1.3, 16.1.7, and 15.1.11, corresponding to each affected branch. Organizations should identify their current deployed version and upgrade to the appropriate fixed release.
F5 has confirmed that the October 2025 patches address the underlying vulnerability and that customers who applied them promptly may have avoided compromise. However, the advisory does not specify when active exploitation began, only that it was confirmed in March 2026. Organizations that patched but have not verified their systems against F5's published indicators of compromise should conduct that assessment. F5's indicators include file anomalies in /run/bigtlog.pipe, hash or size mismatches on /usr/bin/umount or /usr/sbin/httpd, and suspicious localhost iControl REST API access in audit logs.
The patch status for end-of-technical-support (EoTS) versions has not been evaluated by F5. Organizations running BIG-IP APM versions outside the supported branches should consult F5 directly and should not assume patch coverage without explicit confirmation from the vendor.
Are there any other recommended actions to take?
Organizations should apply the F5-issued patches immediately and, where patching cannot occur during an active change window, isolate BIG-IP APM management interfaces from untrusted networks using ACLs or firewall policy.
All internet-accessible BIG-IP APM systems should be reviewed against F5's published indicators of compromise, including file integrity checks and audit log review — to assess whether a prior compromise occurred before the patch was applied.
Management self-IP access should be restricted to trusted internal subnets or bastion hosts, and any unauthorized configuration changes, new accounts, or suspicious scripts discovered during review should be treated as indicators of active post-exploitation activity pending further forensic analysis.
How can CyCognito help your organization?
CyCognito published an Emerging Threat Advisory for CVE-2025-53521 in the CyCognito platform and is actively researching enhanced detection capabilities for this vulnerability.
To learn how CyCognito can help your organization reduce external exposure and manage emerging threats more effectively, contact us to request a demo.



