Passive DNS: Active discovery from your organization's DNS history
The traditional Domain Name System (DNS) is a real-time distributed database system where queries to DNS servers and resolvers translates hostnames into IP addresses and vice versa so that humans don’t have to remember IP addresses and specific URLs to see their favorite cat videos. 😸
DNS is the epitome of “quick and dirty” – it is optimized for quick retrieval in real-time of the nearest server (e.g., so that consumers can find what they are looking for quickly on Amazon and Netflix), and it has no “memory” in that it doesn’t maintain an historical record of what happened in the past. So, before passive DNS replication (or passive DNS) was presented to the world in 2005, once a DNS record was modified, and after a few hours of DNS propagation, there was no way to recover the old DNS record values.
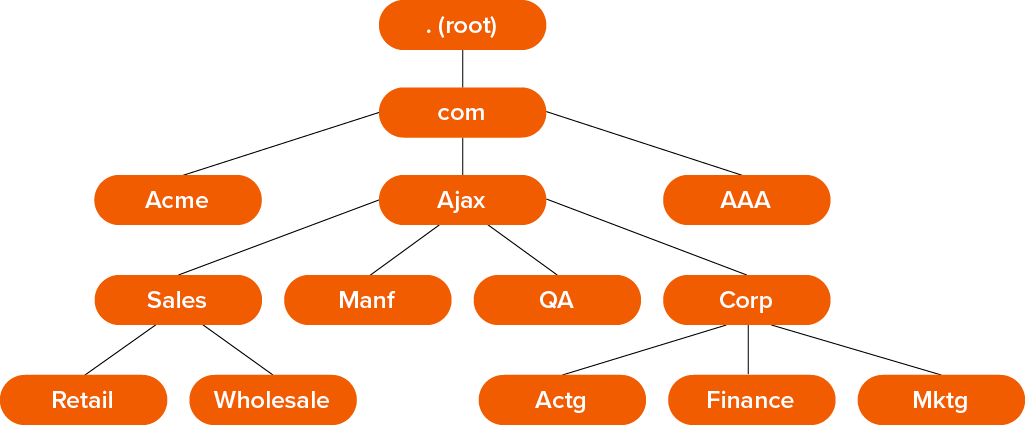
Figure 1. Example Domains & Subdomains
In contrast, passive DNS replication captures DNS queries on the network and stores them for later retrieval, which basically means there is an historical record of DNS communications that can be accessed by security researchers later. This represents a valuable font of information in this era of big data because of what it can tell us about what is being sought and what can be found on the internet.
Without a passive DNS record, DNS is really the wild west.
In passive DNS, DNS queries, IP address lookups, and stats about everything related to the domains, servers and IP addresses involved in the common DNS communications are saved in a database for later analysis. This is what converts the live DNS results into passive DNS data.
The initial intentions for passive DNS were mainly focused on mitigating malware, protecting brands, mitigating phishing and email policy violations, and data recovery and research.
Fifteen years later there are many ways to use passive DNS to do effective attack surface reconnaissance using this historical data, and we are going to discuss five of them here and how it can be utilized for mapping your attack surface.
1. Discover DNS Domain Historical Data
By possessing historical DNS Domain data you can analyze old DNS records, check for new values, compare differences, and find possible attack vectors. An attacker with this information (which can be passively sniffed from network traffic) can see where and when your organization has changed. Perhaps you added a subsidiary, changed a brand name and orphaned some cloud servers, or simply forgot that data center existed. If these systems are connected to your infrastructure and unsecured, if you don’t know about them and attackers do, the consequences could be costly.
2. Explore and Discover Subdomains
Have you ever wondered how many subdomains your organization has? Well, attackers do too. And they can use the data from passive DNS to find out. As an example, an organization like Facebook can have over 10,000 subdomains.
By exploring subdomains, a motivated attacker can sometimes find unsecured areas of websites and development platforms, and test and research areas that might map to adjacent, similar areas in the production environment. Perhaps these systems don’t have valuable data within them, but they may guide an attacker into using a cross-site scripting attack against your production server because it’s great granddad precursor is sitting forgotten in a subdomain no one is managing.
Some subdomains may be low value (to you) and entirely unmanaged and forgotten, but they can still be valuable to a remote attacker from a proof of concept and reconnaissance perspective.
3. Relate WHOIS History to DNS Domain History
WHOIS is another ancient protocol born of a simpler age when a few trusting academics and scientists were running ARPANET (the precursor to the internet). In 1982 the Internet Engineering Task Force published a protocol for a directory service for ARPANET users. Initially, the directory simply listed the contact information that was requested of anyone transmitting data across the ARPANET.
As the Internet grew, WHOIS began to serve the needs of different stakeholders such as domain name registrants, law enforcement agents, intellectual property and trademark owners, businesses and individual users. WHOIS stores the registered users or assignees of an Internet resource, such as a domain name, an IP address block or an autonomous system assigned to an organization. In addition to being useful to legitimate users for attack surface mapping, it’s a treasure trove for attackers.
When WHOIS history is correlated with passive DNS records, an attacker can see when an organization changed their WHOIS IP and domain information, who their previous technicians were, identify the administrative and general contact information for the IT organization and discover their name servers—a pretty important set of details that may map to hosting provider, subsidiaries, acquisitions, or disgruntled employees with inside information.
Further finding of associated domains is made easy by combining IP information extracted from the passive DNS database with historical WHOIS database records.
4. Detect Open Ports
As we all know, scanning open ports is one of the first steps taken when you’re in the process of performing full reconnaissance and intel gathering research, but it is also a rather noisy and an obvious way to proceed. Any countermeasure designed to detect a port scan should be able to easily identify and mitigate a scanner coming from a dedicated IP.
But with passive DNS, a port scan is not required to detect popular open ports like 21, 22, 80 or 443. For ports like those, and even for the more esoteric protocols and services, there will be Service (SRV) records in the passive DNS database that effectively enumerate exposed ports that are ready for exploitation.
5. Find Domains from IPs
As an attacker is mapping an attack surface, they will no doubt identify IPs that may not be definitively associated with a given organization. This could be simply because the IP was never owned by the organization, or it could be owned by the organization and not mapped properly to DNS, or perhaps it was once mapped properly and has since been forgotten. Passive DNS can provide an historical record for the organization's DNS queries and whether the IP ever featured in them, giving an attacker and you an idea of the IP’s origins and ownership.
Conclusion
Passive DNS data is a valuable source of security intelligence focused on DNS queries that shows records that allows you to discover domain names used in the past, explore and discover subdomains, relate individuals with IPs and hostnames, detect open ports, track down spoofed domains, and map your attack surface without resorting to time-consuming manual scanning.
In the coming weeks and months you’ll see more information about the novel ways CyCognito is blending passive DNS replication with Threat Intelligence to not only discover your entire attack surface but detect the paths of least resistance used by attackers.



