What Is Continuous Threat Exposure Management (CTEM)
Continuous Threat Exposure Management (CTEM) is an operating model for continuously reducing an organization’s security risk by managing exposure across the entire enterprise attack surface.
Shifting away from point-in-time testing and futile vulnerability management, CTEM runs as a repeatable cycle: define what outcomes matter, discover relevant exposure, prioritize what to address based on likelihood and impact, validate with real-world testing where needed, and drive remediation across owners and teams. The goal is steady, measurable risk reduction by focusing effort on the exposures that matter most, then proving they were reduced.
A CTEM program consists of interconnected processes that unify external and internal asset discovery, threat intelligence integration, prioritization based on business risk, active validation of defenses, and orchestrated remediation. By integrating these components, organizations can anticipate potential attack paths, address security gaps quickly, and measurably lower their exposure over time.
From Vulnerability Chasing To Exposure Management
Traditional vulnerability management programs break down at scale: point-in-time assessments, siloed validation, and severity-first prioritization create massive backlogs and limited real-world impact.
CTEM emerged as a continuous, business-aligned approach that connects what is exposed to what matters, validates what is real, and mobilizes remediation across the teams that can fix it.
Key drivers include:
- Shift From Vulnerability Management To Exposure Management: Moving beyond scanning and patching based on severity scores, toward contextual risk, exploit intelligence, and business impact, with prioritization grounded in validated evidence and deep understanding of what would materially affect the business.
- Expansion Of The Modern Attack Surface: Cloud infrastructure, SaaS, identity sprawl, external-facing services, and supply chain interdependencies.
- Need For Continuous Validation Of Real-World Risk: Ongoing validation of exploitability and control effectiveness so identified exposures represent realistic cyber threats.
- Demand For Business-Aligned Risk Prioritization: Scoping around critical business functions and measuring security efforts through demonstrated risk management .
- Integration Of Discovery, Prioritization, Validation, And Mobilization: CTEM unifies these activities into a structured, repeatable five-step cycle.
- Failure of patch-only models: Patching alone can’t keep pace with attackers, especially as time-to-exploitation (TTE) continues to shrink (accelerated by AI), making continuous exposure prioritization and validation mandatory, not optional.
CTEM Market and Adoption Indicators
CTEM adoption is being accelerated by executive pressure for business-aligned risk reporting, translating technical exposure into measurable business outcome so CISOs can justify investments and mobilize non-security teams.
Gartner strategic planning assumptions cited in the draft illustrate the direction of travel:
- By 2026, organizations that prioritize security investments using a continuous exposure management program will be three times less likely to suffer a breach compared to those relying on traditional approaches.
- By 2028, more than 50% of threat exposure findings will stem from nontechnical vulnerabilities (identity weaknesses, SaaS misconfigurations, third-party risk, and business process gaps).
- By 2028, organizations that implement CTEM with strong cross-business mobilization will experience at least a 50% reduction in successful cyberattacks.
The CTEM Lifecycle (Five Stages)
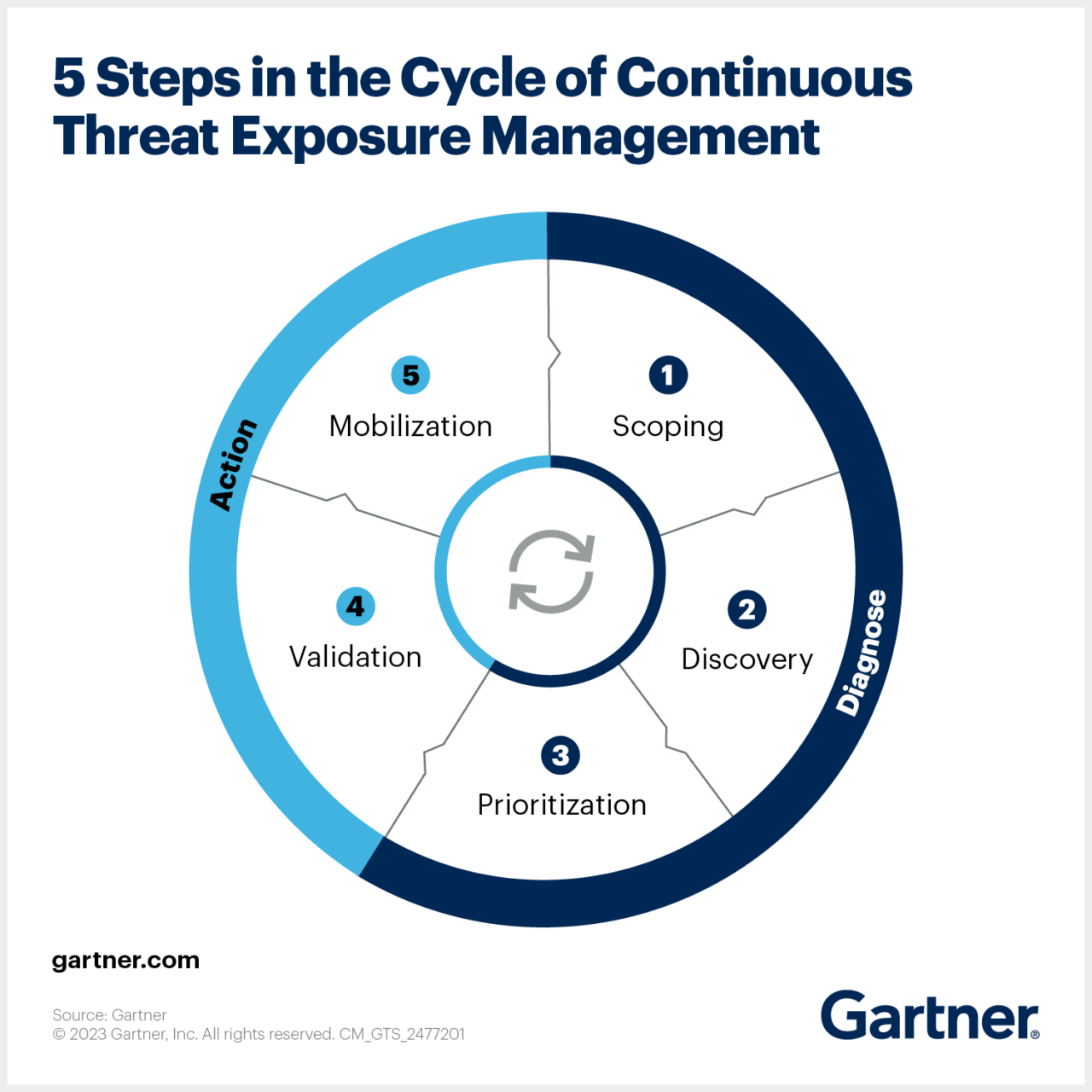
CTEM is an ongoing process that involves five stages: scoping, discovery, prioritization, validation, and mobilization.
1) Scoping
Scoping is the foundational step of the CTEM lifecycle and defines what the organization is trying to protect. Rather than starting with tools or vulnerabilities, it begins with critical business services, the technologies that support them, and the attack surfaces they expose.
The scoping stage defines what the organization will assess and why. Instead of starting from vulnerability severity, scoping starts from business risk. The objective is to identify which business processes, assets, and outcomes would be most affected by a successful attack, and to use that context to define the boundaries of threat exposure.
Key activities:
- Identify critical business services, applications, and data
- Define critical risk scenarios based on potential business impact
- Establish scope boundaries for assets, environments, and attack surfaces
- Align assessment goals with business and regulatory priorities
- Document assumptions, constraints, and success criteria
2) Discovery
CTEM requires continuous discovery of assets and security controls across dynamic, hybrid environments where infrastructure changes frequently. Continuous discovery identifies newly deployed systems, misconfigured services, shadow IT, and control gaps across on-premises, cloud, and SaaS environments.
The discovery stage focuses on identifying and inventorying assets, exposures, and threat conditions within the defined scope. This includes mapping internet-facing and internal assets, identifying vulnerabilities, misconfigurations, and weaknesses, and understanding how attackers could observe or reach these assets.
Discovery also incorporates threat modeling to connect technical findings with attacker behavior. By identifying likely threat actors, capabilities, and objectives, organizations can map potential attack paths rather than treating findings as isolated issues.
Key activities:
- Discover and classify internal and external assets
- Identify vulnerabilities, misconfigurations, and weak controls
- Perform attack surface discovery and security testing
- Conduct threat modeling and attacker path analysis
- Correlate technical findings with asset criticality
3) Prioritization
Rather than relying solely on severity scores like CVSS, CTEM strategy prioritizes exposures based on how likely they are to be exploited and the potential business impact if they are. It incorporates threat findings, exploit availability, attacker behavior, asset criticality, and exposure context into prioritization decisions.
The prioritization stage determines which exposures require action. Rather than addressing every identified issue, it ranks exposures based on exploitability, likelihood, and business impact, narrowing focus to the exposures most likely to be used in successful attacks against critical assets.
Key activities:
- Rank exposures based on likelihood and business impact
- Assess exploitability and attacker reachability
- Evaluate remediation effort and feasibility
- Reduce large finding sets to a manageable action list
- Define ownership and urgency for prioritized items
4) Validation
A core differentiator of CTEM is validation of security controls through adversarial testing techniques such as breach and attack simulation (BAS), automated penetration testing, and emulation. This step verifies whether identified exposures are actually exploitable in real-world conditions and moves security programs from assumed protection to proven effectiveness.
The validation stage confirms to the security teams whether prioritized exposures represent real, identified threat. It involves verifying that an attacker can realistically exploit the exposure and reach a critical asset, rather than relying on theoretical risk or static severity scores.
Key activities:
- Validate exploitability of prioritized exposures
- Blast radius and attack path analysis
- Assess effectiveness of existing security controls
- Measure detection and response readiness
- Reduce false positives and de-prioritize theoretical risk
5) Mobilization
Mobilization focuses on turning validated findings into sustained risk reduction. Remediation must be coordinated across security teams, IT, cloud, and application teams, supported by clear ownership, workflow integration, and automation where possible. Over time, this loop feeds lessons learned back into scoping, control design, and operational processes.
The mobilization stage executes remediation actions based on validated findings. This includes deploying technical controls, fixing configurations, patching systems, or adjusting processes. Mobilization is continuous rather than episodic. As environments change and new exposures emerge, actions are reprioritized and repeated.
Key activities:
- Assign remediation actions to responsible teams
- Implement security controls or configuration changes
- Track remediation progress and SLAs
- Re-test and validate fixes
- Feed results back into ongoing CTEM cycles
Tips from the Expert

Dima Potekhin, CTO and Co-Founder of CyCognito, is an expert in mass-scale data analysis and security. He is an autodidact who has been coding since the age of nine and holds four patents that include processes for large content delivery networks (CDNs) and internet-scale infrastructure.
Here are practical tips to help you operationalize and mature a CTEM program, based on experience working with large enterprises:
- Build an exposure graph, not just a vulnerability list: Model relationships between identities, assets, privileges, network paths, SaaS roles, and data sensitivity in a graph structure. Attackers chain weaknesses, and you should think the same way. Graph-based modeling surfaces toxic combinations and reachable critical assets that linear dashboards rarely reveal.
- Establish integrations for a holistic exposure view: Build integrations that automatically correlate exposure data across internal and external environments, cloud, SaaS, and other attack surfaces. The goal is one consistent view of exposure and attack paths, not isolated tools producing disconnected findings.
- Prioritize from the attacker’s point of view: Bias toward reachability, exploitability, and path-to-impact over raw severity. Ask, “Can an attacker actually reach this? What does it unlock? What is the fastest path to a meaningful outcome?” This keeps effort focused on exposures that are most likely to matter.
- Shift from point-in-time testing to continuous refresh and validation: If your program relies on periodic pen tests or scheduled assessments, evolve the mindset to continuous discovery and ongoing validation. Refresh inventory continuously and validate exploitability (at least across a subset of critical assets) on a daily basis, so coverage stays current as environments change.
- Integrate change management signals into prioritization: Tie CTEM to infrastructure-as-code commits, major releases, M&A events, and SaaS onboarding. Exposure spikes often follow business change. Risk scoring that adapts to business realities is key.
Technologies Enabling a CTEM Program
Different CTEM programs use a different mix of security platforms. Common solution categories include:
Asset Management
Provides visibility into the organization’s digital estate and identifies assets, their exposure level, and accessibility to potential attackers (internal, external, cloud, end-user, and digital assets).
Relevant capabilities:
- Seedless asset discovery
- Continuous monitoring
- Contextual association
- Evidence of ownership (chain-of-discovery)
Vulnerability Assessment
Identifies known weaknesses such as unpatched software, insecure configurations, and exploitable application flaws.
Relevant capabilities:
- Vulnerability scanning
- PI-based vulnerability assessments
- Dynamic application security testing (DAST)
- Passive and active testing
Exposure Prioritization
Determines which findings matter most because organizations cannot remediate everything.
Relevant capabilities:
- Aggregation, deduplication, and normalization
- Prioritized threats (beyond generic risk scoring)
- Threat context (TI)
- Architecture context
- Business context
Adversarial Exposure Validation
Provides evidence of exploitability. Rather than assuming a vulnerability is exploitable, it tests whether an attack scenario works in the real environment.
Relevant capabilities:
- Exploitability validation
- Attack simulation (BAS)
- Red teaming
- Compensating controls
Exposure Remediation And Mitigation
Operationalizes risk assessment by using prioritized and validated findings to eliminate or reduce exposure through remediation or mitigation. It commonly relies on tickets, workflow automation, and IT service management (ITSM) coordination.
Key capabilities:
- Ticketing and workflow orchestration (ITSM integration)
- Ownership assignment and escalation paths
- Remediation tracking (status, SLAs, aging)
- Re-testing and closure validation
Exposure Analytics And Risk Quantification
Aggregate data from discovery, threat intelligence (TI), and validation to provide a unified view of exposure and risk, translating technical findings into business-relevant metrics for consistent prioritization and executive reporting.
Key capabilities:
- Exposure aggregation and normalization across sources
- Cross-domain correlation (assets, identities, controls, attack paths)
- Mapping to business priorities (services, applications, criticality)
- Risk assessment and prioritization analytics
- Trend reporting and executive dashboards (risk metrics over time)

Operationalizing CTEM Through External Exposure Management
CTEM breaks when it turns into vulnerability chasing. Too many issues, weak proof, and constant escalation…
This whitepaper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.

Getting Started with a CTEM
Organizations adopting CTEM often begin from one of three starting points: add external exposure management to an existing internal program, extend an existing external capability beyond detection, or start building a Continuous Threat Exposure Management program from scratch.
1) Add External Exposure Management To An Existing Internal Program
Integrate external asset discovery with internal inventories, leverage integrations to auto-correlate external exposure management with internal asset inventories business context, add attacker reachability and exploitability analysis to prioritize, and establish workflows for coordinated remediation. The end goal should be a holistic view of your entire attack surface.
2) Extend An Existing External Capability Beyond Detection
Simulate attack techniques to confirm exploitability and business impact, applying business context and threat modeling to prioritize, build automated remediation workflows, and implement metrics to track exposure reduction.
3) Start From Scratch
Begin with external asset discovery and mapping, identify and classify exposed assets and misconfigurations, use continuous discovery and organizational context to estimate risk, laying in internal data and validation findings about real-world exploitability.
Best Practices For Execution
1) Start With Threat Scenarios, Not Assets
CTEM should be anchored in how adversaries operate, not static asset catalogs or generic vulnerability lists. Start with high-probability, high-impact scenarios that could realistically disrupt critical business services, then work backward to identify enabling assets, identities, misconfigurations, and control failures.
2) Scope Narrowly, Then Expand Intelligently
Avoid enterprise-wide CTEM coverage at the outset. Start with one or two critical business services, a limited set of environments, or a specific threat scenario, then expand based on demonstrated success and stakeholder confidence.
3) Integrate Identity Early
Identity is a dominant factor in modern attack paths analysis, especially in hybrid and cloud environments. CTEM is no different. Integrate identity exposure early to improve attack path modeling and surface critical risks that asset-centric approaches miss.
4) Add An Emerging Threats Motion
Build an emerging threat process that compresses the cycle: match the threat to your environment, find all instances, confirm exploitability (not just severity), and route remediation by critical service impact, accounting for protective layers already in front of the asset.
5) Automate Ruthlessly, Govern Carefully
Continuous threat exposure management cannot scale without automation across discovery, validation, prioritization, and remediation, but automation needs governance: clear ownership, approval thresholds, and rollback processes.
6) Expect Organizational Resistance
Adoption of a CTEM strategy represents a cultural and operational shift. Plan for pushback, and address it through executive sponsorship, clear communication of business outcomes, alignment on risk appetite and early wins that demonstrate how your security efforts contribute to proactive risk management.
How To Measure CTEM Success
Measure Success By Demonstrated Risk Reduction
CTEM success is defined by measurable reduction of material business risk, not the volume of vulnerabilities discovered. The emphasis is on proving that exposure management activities meaningfully reduce the likelihood or impact of disruption to critical business functions.
- Risk-impact reporting: Demonstrate how exposure mitigation lowers risk to revenue-generating systems, operational continuity, regulatory obligations, or strategic initiatives.
- Business alignment: Define CTEM scopes around critical business services and measure improvement within those defined boundaries rather than across the entire technical estate indiscriminately.
Use Outcome-Driven, Business-Tuned Metrics
CTEM metrics should support decision-making beyond the security team by translating technical findings into performance indicators that leadership can understand and act upon.
- Outcome-driven measurement: Track improvements in exposure posture tied to business outcomes, not tool-generated activity metrics.
- Executive-level clarity: Present exposure trends in language aligned to business operations rather than technical severity scores.
- Shared accountability metrics: Establish joint KPIs across security, IT, and business stakeholders to reinforce collective ownership of exposure reduction.
Validate Exploitability And Control Effectiveness
A core differentiator in CTEM is validation, proving whether exposures are realistically exploitable and whether security controls actually prevent real risk.
- Validated exposure reduction: Measure decreases in exposures that are confirmed as exploitable in the organization’s real-world environment.
- Control performance validation: Assess whether preventive and detective controls successfully block or detect realistic attack scenarios.
- Prioritization accuracy improvement: Track how validation improves prioritization precision and reduces noise from theoretical risk.
Track Remediation Velocity And Exposure Life Cycle
CTEM is iterative and operational. Measuring how quickly validated exposures are addressed is central to evaluating program maturity.
- Mean time to resolution improvements: Monitor reductions in time required to remediate or contain high-risk exposures.
- Exposure life-cycle tracking: Track exposures from identification through remediation, mitigation, or formal risk acceptance.
- Cycle consistency: Measure completion and cadence of the full CTEM cycle (scoping, discovery, prioritization, validation, mobilization) to ensure sustained execution.
Measure Coverage And Scope Maturity
CTEM expands beyond traditional vulnerability management into cloud, SaaS, identity systems, supply chain dependencies, and other external-facing assets. Success includes progressively broadening and refining coverage.
- Attack surface inclusion growth: Track expansion of CTEM coverage across business-critical assets and digital environments.
- Inventory quality improvement: Measure improvements in asset visibility and accuracy over time.
- Continuous reassessment frequency: Monitor how often exposures are re-evaluated as environments evolve.
Operationalizing CTEM With CyCognito
Continuous threat exposure management (CTEM) aims to reduce risk continuously, but most programs still rely on scoped, periodic threat detection that fall out of sync with environments that change every day. When discovery, validation, and mobilization run on different cadences, teams end up prioritizing theoretical severity instead of what attackers can actually exploit.
CyCognito anchors CTEM in external exposure management by starting from the attacker’s perspective (what is discoverable, reachable, and actionable from the outside) and carrying that signal through validation and mobilization so CTEM runs on proof of what is actually exposed and exploitable, not point-in-time assumptions.
CyCognito operationalizes CTEM by:
- Continuously discovering externally reachable assets and linking them to the right owners
- Validating exploitability and security control effectiveness from the outside in
- Identifying risk conditions beyond CVEs (misconfigurations, auth gaps, data exposure, etc.)
- Providing clear evidence that teams can self-verify (chain of discovery and supporting artifacts)
- Prioritizing what to fix using exploitability findings and TI signals (including activity in the wild)
- Managing the end-to-end remediation cycle (routing, guidance, tracking, re-validation)
By grounding CTEM in external attack surface management and validated proof, CyCognito helps teams reduce noise, focus remediation on what matters, and show measurable progress in exposure reduction.
If you want to evaluate your environment from an attacker’s perspective, request a 1:1 demo.