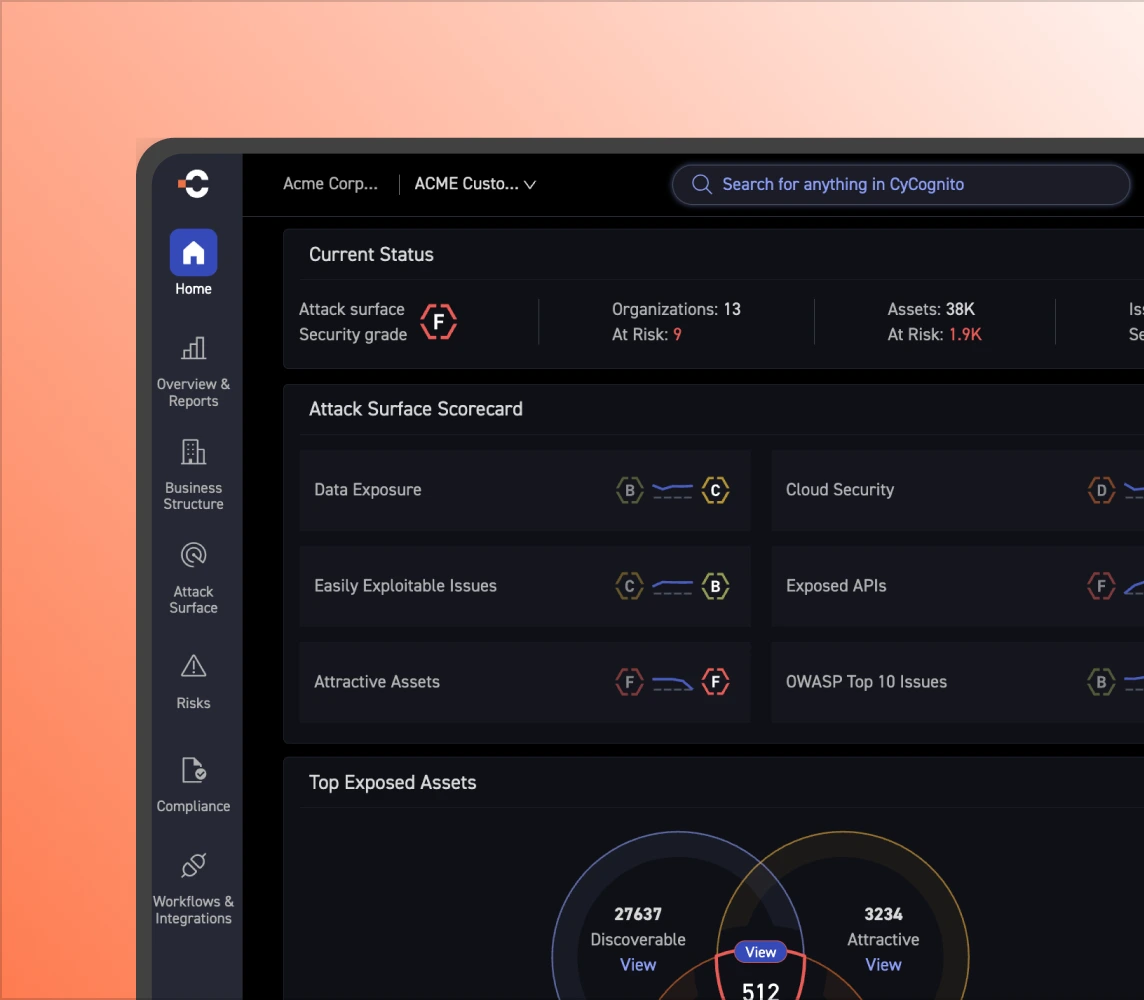
See your attack surface the way attackers do.
CyCognito discovers every external asset tied to your organization, validates exploitability across, and surfaces the small set of risks that demand action now.
Get the demo
Trusted by leading global enterprises.













































Where are you on the curve?
Most organizations see a fraction of their external surface and test even less. CyCognito delivers full visibility and continuous validation, with remediation measured in days.
Every exposure tested.
Every risk confirmed.
CyCognito validates exploitability across your external footprint. Abandoned assets, authentication bypass, OWASP and more, covered continuously with no manual scoping.
More about adversarial validationThe 0.1% that matters.
CyCognito surfaces the exposures that are discoverable, attractive to attackers, and confirmed exploitable. That small set is where your team focuses.
More about exploit intelligence
I can’t point to another tool that does as thorough a job of exploring and exposing those assets that you didn’t even know you had. It’s so valuable.
 Light & Wonder
Kevin Kealy ・ Chief Information Security Officer
Light & Wonder
Kevin Kealy ・ Chief Information Security Officer
Know what attackers will find first
CyCognito's 60,000-node global network maps your full external footprint from your organization name alone. No seed data, no IP lists, no manual setup. Shadow IT, acquired infrastructure, and forgotten services included.
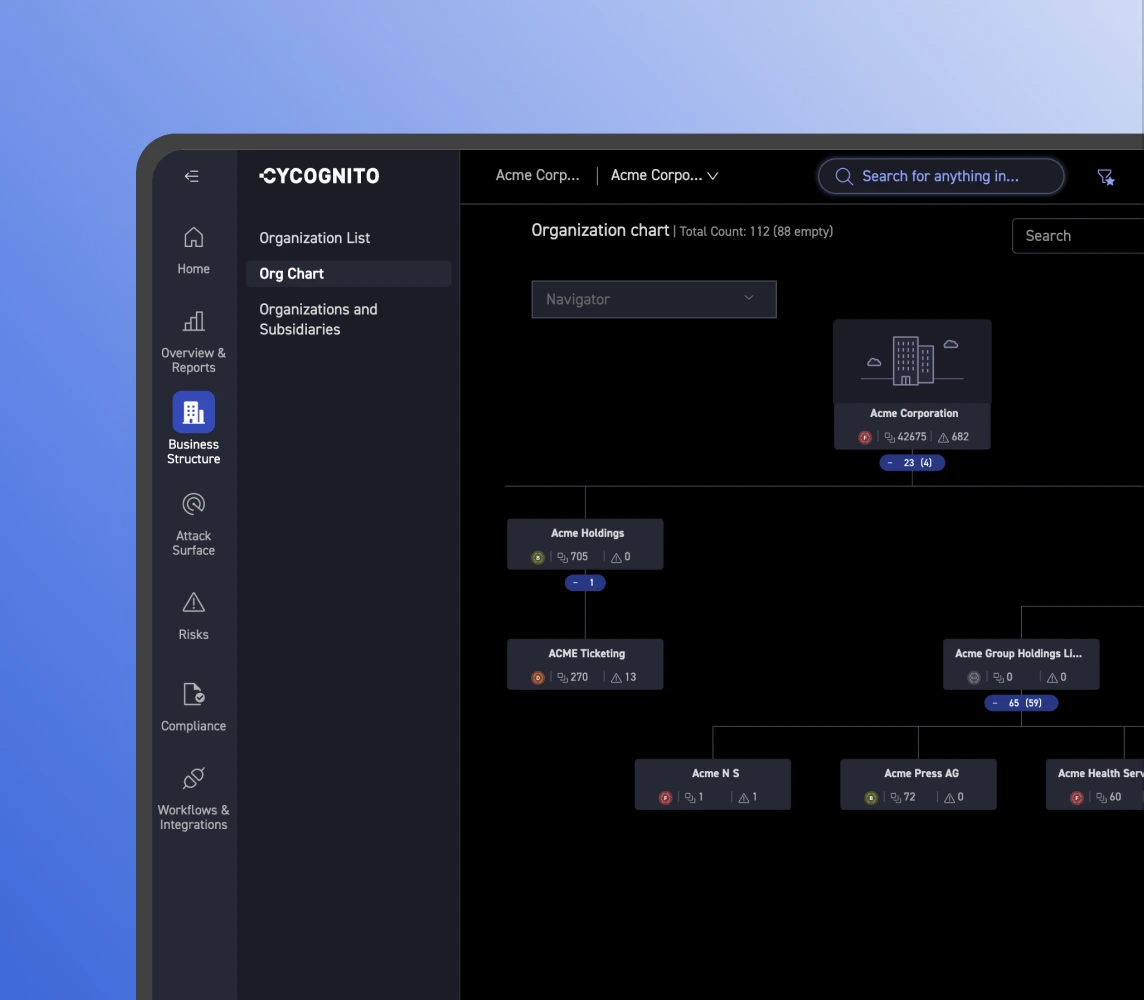
Link every asset to its owner
An unattributed asset belongs to no one. CyCognito's graph-based attribution connects every discovered asset to the right subsidiary, brand, or business unit. Evidence backs every relationship.
See where risk accumulates
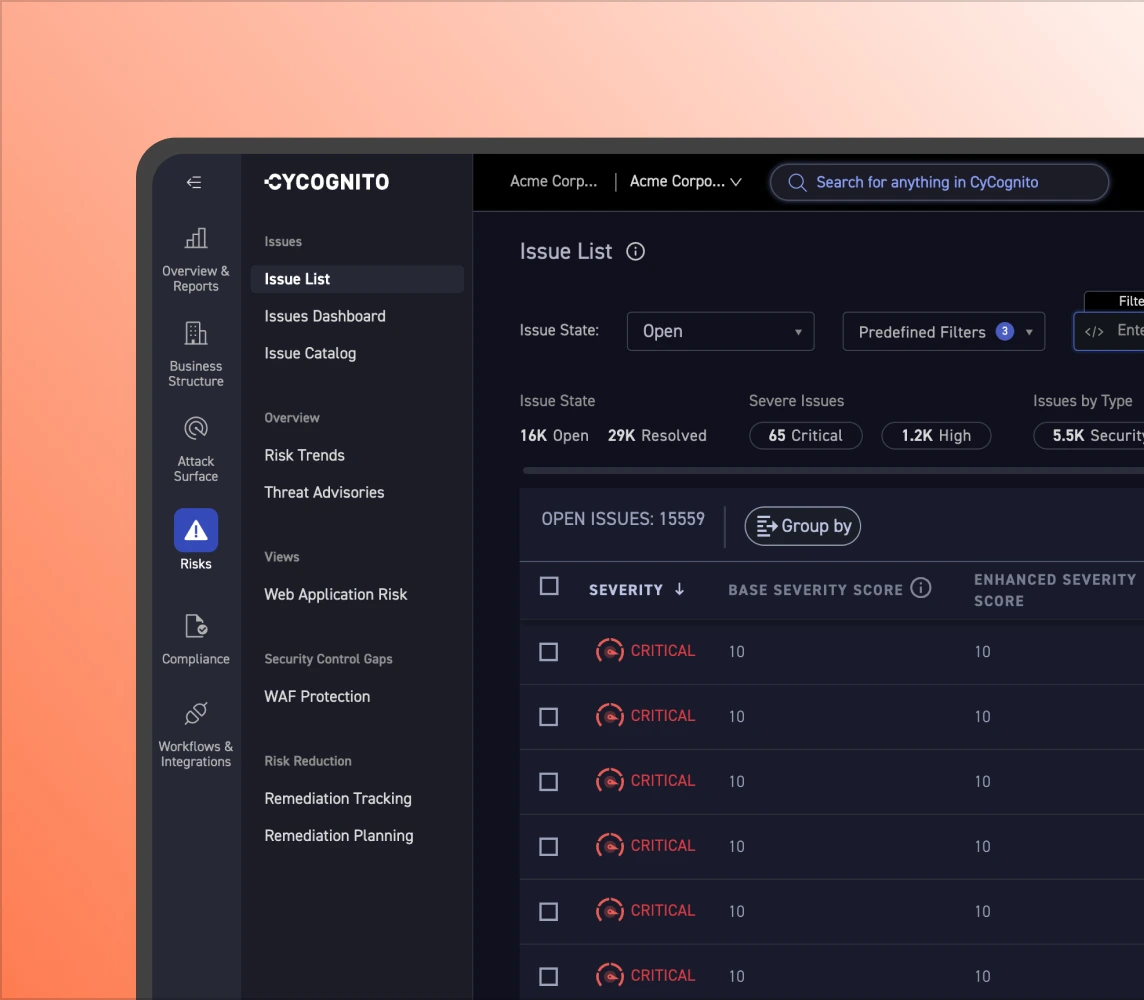
Visibility without validation is just noise. CyCognito runs continuous active security tests across your entire external footprint, confirming which exposures are genuinely exploitable and which are not.
More about adversarial validation
Focus on issues worth fixing
CyCognito combines validated findings, business context, and threat intelligence to surface the small set of external risks that actually matter. Your team acts on confirmed risk, not theoretical severity scores.
More about exploit intelligence