



Practical guides, research, and insights to help security teams manage external exposure with clarity and control.
CTEM breaks when it turns into vulnerability chasing. This white paper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.
Read more about Operationalizing CTEM through External Exposure Management
Download the white paper to learn about CTEM's core components and how they contribute to cybersecurity resilience, how CTEM addresses the challenge of managing risk on attack surfaces, and how CyCognito's capabilities align with CTEM's requirements.
Read more about Understanding Continuous Threat Exposure Management (CTEM)
The fundamental approach to pen testing has not changed much since the first test over 50 years ago. Is it still sufficient for securing today’s IT environment? Download the white paper to uncover the challenges with pen testing and an alternative path forward.
Read more about Rethinking Penetration Testing
In May 2022, Dark Reading surveyed 103 cybersecurity and IT professionals. The results are clear: monitoring your external attack surface should be a priority.
Read more about Threat and Vulnerability Data: Risk Reduction Opportunities Examined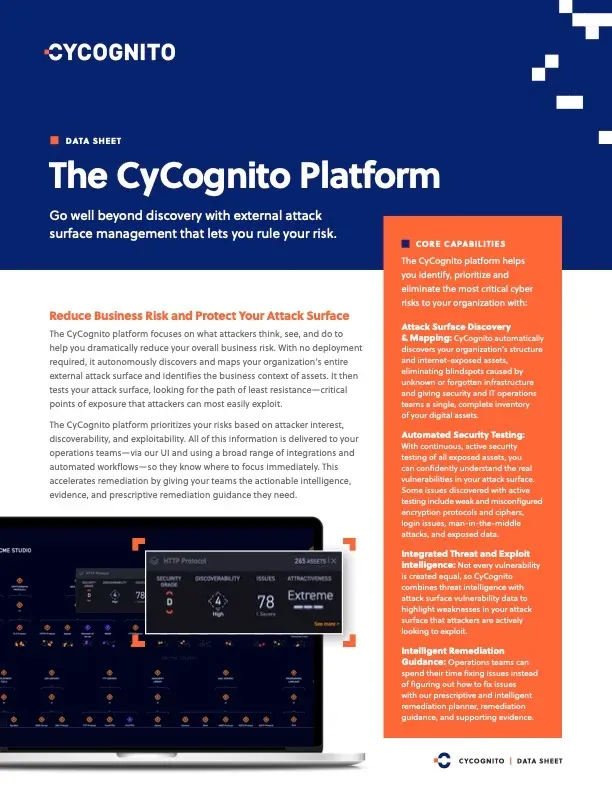
See how our discovery engine uses graph data modeling to map your organization’s full attack surface. Review our core capabilities, key features and what differentiates us from legacy security tools.
Read more about The CyCognito Platform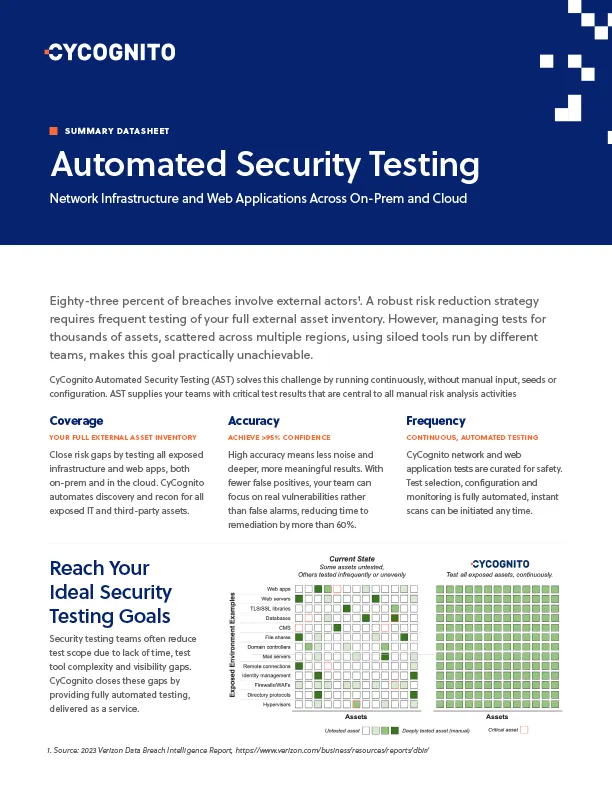
Download our quick two-page datasheet to explore how AST can simplify your testing process and enhance your security posture.
Read more about Automated Security Testing
Learn how you can uncover your full organizational structure with high accuracy, enterprise scale, details, and evidence so that you can properly understand who owns and manages each digital asset exposed to the internet.
Read more about Discovery and Contextualization
Download CyCognito's Prioritization and Remediation Technical Datasheet to uncover the benefits of risk-based prioritization in streamlining your remediation efforts.
Read more about Prioritization and Remediation
Shift from a reactive to proactive exposure management process using CyCognito’s attack surface management platform.
Read more about Exposure Management
A technology checklist for implementing exposure management in your organization.
Read more about Demystifying Continuous Threat Exposure Management (CTEM)
Download this brief to learn about the common problems that exist today within asset discovery and contextualization and how CyCognito can be implemented as a solution.
Read more about Discover and Contextualize
Learn about today's common problems within risk prioritization and remediation and how CyCognito can be implemented as a solution.
Read more about Prioritize Risk and Accelerate Remediation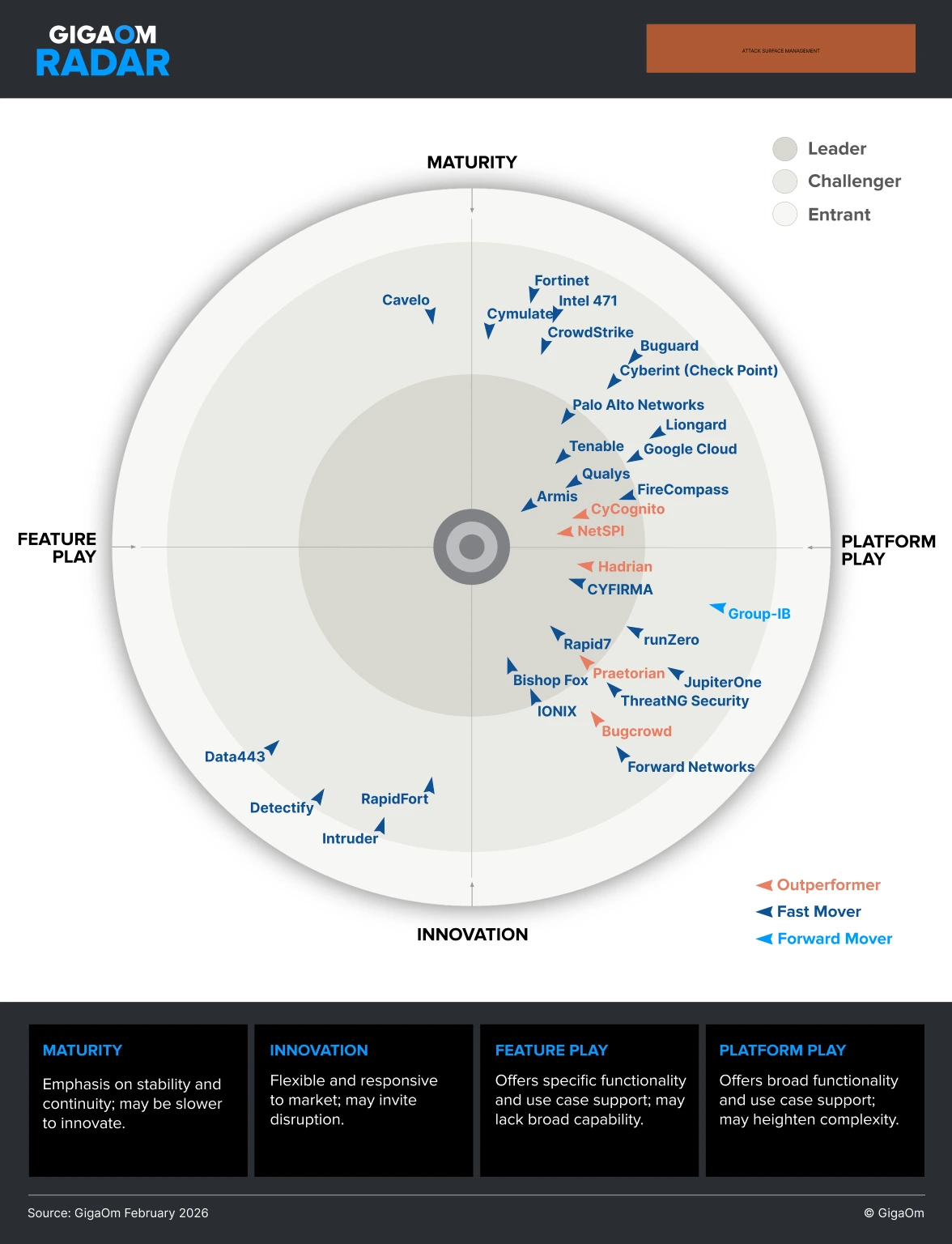
The expansion of an organization's attack surface continues to present a critical business challenge. Download the GigaOm Radar for Attack Surface Management to get an overview of the available ASM solutions, identify leading offerings, and evaluate the best solution for you.
Read more about GigaOm Radar for Attack Surface Management 2026
Download the report now to stay ahead of emerging threats and strengthen your organization’s security posture for 2024.
Read more about State of External Exposure Management, Summer 2024 Edition
The 2024 State of Web Application Security Testing report analyzes responses from hundreds of cybersecurity professionals in both the US and the UK, providing valuable insights into the current state of web application security testing.
Read more about 2024 State of Web Application Security Testing
Learn how leveraging automation through modern EASM technology can help bridge the gap between attackers and defenders, making it possible for defenders to improve their security and risk posture.
Read more about The State of External Attack Surface and Risk Management