There is no “one size fits all” solution to the Apache Log4j issues yet, so at CyCognito we have implemented two CyCognito testing modules (one passive, one active). We have also performed an internal assessment on our exposure to these vulnerabilities in order to protect our customers’ data.
Based on our experience responding to these issues, advice from expert CISOs, and our community of customers, here are some steps for a simplified response plan you can use today and for future outbreaks. For a much more detailed response we recommend the CISA Apache Log4j Vulnerability Guidance.
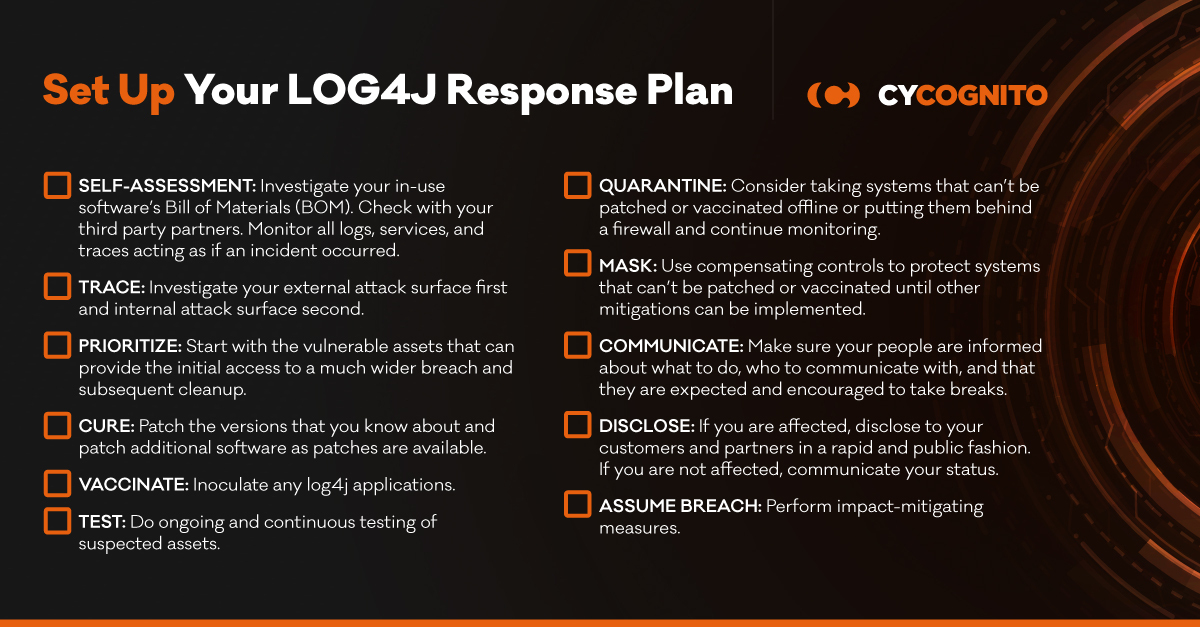
Our security research and analyst teams recommend performing the following immediately:
- SELF-ASSESSMENT: If you are a software or technology services vendor your first priority should be ensuring your customers’ data is secure.
- Investigate your Bill of Materials (BOM) in any software you provide.
- Check with your third party partners that they are not affected in a way that affects your software or service.
- Monitor all logs, services, and traces acting as if an incident did occur until you can be confident one did not.
- TRACE: Investigate your external attack surface first (with an external attack surface management platform like CyCognito) and internal attack surface second to understand if and where you are using specifically vulnerable software. Here’s a list of software we know about so far.
- PRIORITIZE: Start with the assets in your external attack surface that are vulnerable. An exploit to these vulnerable hosts can provide the initial access to a much wider breach and subsequent cleanup.
- CURE: Patch the Log4j versions that you know about in your external attack surface, and patch software which uses Log4j as patches are available in your internal attack surface.
- VACCINATE: Inoculate any log4j applications (use caution and read the details; this also requires a restart)
- TEST: Do ongoing and continuous testing of suspected assets for the vulnerability, including custom-built apps. Plan for this process to continue for years as this vulnerability is in a ubiquitous open source technology. New exploits will be disclosed and old images may be brought online.
- QUARANTINE: If you find systems that can’t be patched or vaccinated consider taking them offline or putting them behind a firewall and continue monitoring affected assets for signs of compromise.
- MASK: Another way to protect systems that can’t be patched or vaccinated is to use compensating controls like web application firewalls (WAF) and eXtended Detection and Response (XDR) that “virtually patch” vulnerable hosts until other mitigations can be implemented.
- COMMUNICATE - Risk teams need to be aware of current status; business and technical risk managers need up-to-date information on remediation plans and progress. Think about what to communicate to the CISO, Chief Risk Officer and business VP’s responsible for profit and loss. Daily email briefings can reduce the need for redundant one on one discussions.
- PEOPLE: Keep in mind that while this looks like a technology crisis it’s also a people problem. Make sure your people are informed about what to do, who to communicate with, and that they are expected and encouraged to take breaks, especially with the holidays approaching. Gratitude and appreciation for their efforts will go a long way!
- DISCLOSURE: Whether affected or not, your management team may need to do something in this regard if you are a provider of software or services.
- If you are affected, disclose to your customers and your partners in a rapid and public fashion so they can take precautions.
- If you are not affected, communicate your status and steps taken to ensure you were not affected.
- ASSUME BREACH: Log4j is an evolving situation and we do not yet understand all of the Tactics, Techniques and Procedures being used as we speak. Perform impact mitigating measures such as the following:
- Rotate security resources on affected systems, such as passwords, certificates, and tokens.
- Flag affected security resources listed above as potential Indicators of Compromise (IOCs), particularly with regards to North-South network flows.
- Continue to update SIEM solutions with evolving IOCs and run against historic logs
- Power cycle or redeploy affected resources to clear working memory without regard to initial investigation conclusions
If you’d like to connect with a CyCognito representative to see how we can help, please contact us.



