Sr. Technical Marketing Manager
May 19, 2025
Security teams are under constant pressure to find and fix vulnerabilities faster, but traditional approaches to security testing often create delays. In this blog, we explore why active security testing, despite its perception for being slow and resource intensive, is the key to achieving faster and more confident fixes. You will learn how accurate testing results drive smarter remediation decisions, how fully automated testing at scale overcomes common operational challenges, and why reducing your window of exposure requires moving beyond passive scanning. If your organization is struggling with long remediation cycles and hidden risks, this is the blueprint for accelerating your security outcomes.

Was Chief Marketing Officer
November 18, 2024
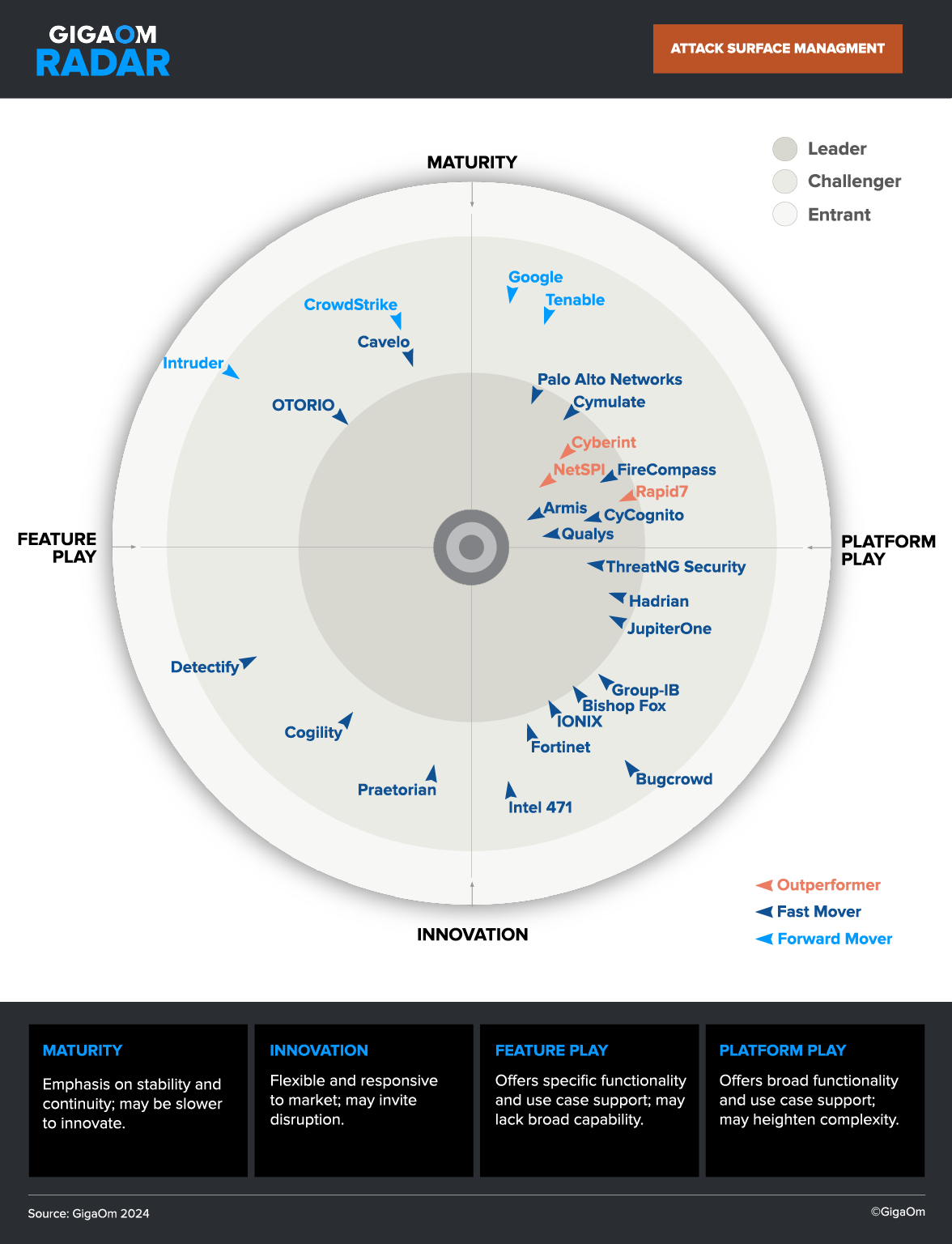
External Attack Surface Management (EASM) is crucial for reducing risks associated with unknown and unmanaged digital assets, which are responsible for over 65% of breaches. This post provides practical guidance on budgeting for EASM, including cost ranges, staffing requirements, and justifications based on risk reduction, labor savings, and operational efficiencies. Learn how EASM can optimize your security investments while improving your organization’s overall cybersecurity posture.

Product Marketing Manager
November 11, 2024
Savvy security leaders are moving from the legacy framework of vulnerability management to the emerging framework of exposure management. To learn more about common challenges security teams might face on their journey to exposure management, check out this report: “Vulnerability Management to Exposure Management: A Roadmap for Modernizing Your Application Attack Surface Security.”

Sr. Technical Marketing Manager
September 16, 2024
Gaps in security testing involve more than missed assets – infrequent and inaccurate security testing can be just as big. This blog provides a five-step plan to help you find testing gaps and tighten your testing program, improving risk management, decision-making, and cost efficiency. A must-read for anyone looking to strengthen their security across their external attack surface.

Product Marketing Manager
September 6, 2023
Have you ever wondered just how much the average external attack surface changes every month?

Was a Senior Product Marketing Manager at CyCognito
August 24, 2023
Vulnerability prioritization is the process of identifying and ranking vulnerabilities in order to focus efforts on the most important vulnerabilities.

Was Sr. Director, Product Marketing at CyCognito
November 23, 2021
Everything that is exposed to the internet, including your security tools and appliances, must be cataloged and tested for security gaps and weaknesses.

Was Director of Technical Product Marketing at CyCognito
April 1, 2021
With the Accellion breach not all disclosures were public or full or timely. Learn why this is a bigger problem than this one supply chain attack.

Was Director of Technical Product Marketing at CyCognito
March 16, 2021
Microsoft Exchange Vulnerabilities – a perfect example why using old technology impacts your security posture today.

Was Vice President of Marketing at CyCognito
February 25, 2021
Zero Trust has implications for every element of your IT infrastructure. See how attack surface management fits into a Zero Trust approach to security.