When bad guys want to break into software systems, they follow a set of structured, consistent processes with key stages to find and exploit vulnerabilitiesץ For this reason, the good guys must also adhere to a standardized, systematic approach when testing systems for security flaws.
Hence the importance of penetration testing phases. The entire process is designed to uncover weaknesses and security gaps before attackers do. By breaking the pen testing process down into a regular set of structured, predictable phases, cybersecurity professionals boost their ability to discover flaws before attackers do.
Read on for details as we break down everything security teams need to know about penetration testing phases, including why they’re important, what the main pen testing phases are, limitations of the phased model for penetration testing, and how to get the most out of a phased approach to pen testing.
This is part of a series of articles about penetration testing.
What are penetration testing phases?
Penetration testing phases are discrete stages within the penetration testing process. To understand fully what penetration testing phases mean, let’s step back a bit and talk about penetration testing in general.
Penetration testing (or pen testing for short) is a simulated attack against a software system. Penetration tests are carried out by security professionals who use their expertise to discover vulnerabilities and other risks within an organization’s software and IT systems. The organization can take steps to fix the issues and improve its security posture before attackers find and exploit the identified vulnerabilities.
The penetration testing process can (and should) be broken down into distinct steps or stages. These are what security professionals mean when they refer to the stages of penetration testing. The stages of penetration testing are also designed to validate the effectiveness of existing security measures, such as firewalls and intrusion detection systems.

Operationalizing CTEM Through External Exposure Management
CTEM breaks when it turns into vulnerability chasing. Too many issues, weak proof, and constant escalation…
This whitepaper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.

The importance of phases in the penetration testing process
Phases play an important role in penetration testing because they help to keep the overall process structured and methodical. This is valuable because consistency helps ensure that testers check for every potential vulnerability and risk.
Without a phased approach, penetration testing has a tendency to become more ad hoc. The result is less consistent testing methods and a higher chance of gaps or oversights.
Structuring penetration testing into phases is all the more important given that pen testing (unlike vulnerability scanning) is a primarily manual activity. Pen testing teams may use penetration testing tools to automate certain parts of their operations (like discovering open network ports or scanning file systems to identify valuable data assets), but they perform other work by hand. Manual processes are more prone to inconsistency because different professionals may carry them out in different ways. By breaking the testing process into discrete stages that all teams adhere to, organizations are able to achieve higher levels of consistency in testing methods and coverage, no matter who happens to perform the tests.
How many penetration testing phases are there?
The exact number of penetration testing phases can vary depending on which methodology a team chooses to follow. However, the industry commonly recognizes either five or seven key stages or phases as essential to the penetration testing process.
There is not actually a major difference between five-phase and seven-phase approaches to penetration testing because they each include the same core stages. The main distinction is that the five-phase methodology doesn’t treat pre-engagement or clean-up as distinct phases; it instead blends them into the planning and post-remediation phases, respectively.
So, ultimately, the number of key stages that an organization chooses to recognize is less important than ensuring thoroughness and consistency during each of the phases it implements.
Tips from the Expert

Dima Potekhin, CTO and Co-Founder of CyCognito, is an expert in mass-scale data analysis and security. He is an autodidact who has been coding since the age of nine and holds four patents that include processes for large content delivery networks (CDNs) and internet-scale infrastructure.
Pen testing has been around for decades, but even the most seasoned testing teams may have room to improve. Here are my tips on optimizing the impact of penetration testing across all phases:
- Don’t define processes too rigidly: It’s important to follow a consistent overarching structure when pen testing, but it’s equally important to give pen testers leeway to operate in whichever ways make most sense to them. Balancing structure with flexibility allows penetration testers to adapt their methods and better simulate how true hackers would proceed. To this end, ensure that penetration testing processes are flexible enough to accommodate varying strategies and techniques.
- Don’t overlook social engineering attacks: It’s not just through technical exploits that attackers can break into systems. They can also use social engineering strategies, like posing as executives and asking employees for login credentials. To get ahead of this risk, factor social engineering liabilities into relevant penetration testing phases.
- Consider agentic pen testing: Increasingly, organizations are drawing on AI agents to help carry out pen tests. They’re not a substitute for human experts, but they can also automate aspects of pen testing (such as information gathering and vulnerability assessment) that previously required extensive manual effort.
- Think like outsiders: When organizations source pen testers from within their own company, it can be tempting for the ethical hackers to draw on insider knowledge when attempting to break into a system. But this is a bad idea because real attackers don’t usually possess this kind of insight – unless they are malicious insiders, of course, but factoring in how the latter type of attacker might operate is only relevant if assessing malicious insider risks is part of the pen testing project scope.
A deep dive into the seven penetration testing phases
Now that we’ve covered the essentials of what penetration testing phases mean, let’s look at each phase in detail.
1. Pre-engagement
The pre-engagement phase of penetration testing is, in many ways, about project management. It’s the time when an organization defines the scope and goals of a penetration testing operation. This is critical because effective pen testing requires a clear focus; otherwise, testers can end up checking the wrong systems or performing the wrong types of vulnerability assessments.
The pre-engagement phase also offers an opportunity for pen testers to gain relevant permissions to carry out their operations. Obtaining formal permission helps mitigate legal liability. It also alerts cybersecurity teams to the tests so that they know they may detect signs of intrusion that are not actually signs of a problem; in this way, pre-engagement planning helps avoid false positive alerts that could distract the organization’s security personnel from true risks.
2. Information gathering (reconnaissance)
The information gathering or reconnaissance phase is where teams gather extensive information about the target system to lay the groundwork for the entire assessment. This phase involves both passive reconnaissance – collecting data from publicly available sources without direct interaction – and active reconnaissance, which includes directly engaging with the target network to obtain more detailed information.
During the reconnaissance phase, penetration testers collect intelligence such as IP addresses, domain information, network topology, network services, operating systems, applications, and user accounts. Identifying the target’s vulnerabilities and potential entry points is a key goal at this stage, as it helps testers plan effective penetration strategies. This phase lays the foundation for understanding the target network and planning the subsequent phases of the penetration test.
Importantly, testers don’t actually attempt to exploit information during this penetration testing phase. They simply use this data to understand their target environment and begin planning ways to break in.
3. Scanning and vulnerability assessment
Scanning and vulnerability assessment is the phase during which penetration testing teams actively look for security vulnerabilities. This is distinct from information gathering because vulnerabilities are flaws that attackers can exploit, whereas information is just that – information about the state of a system.
Virtually every system is bound to have vulnerabilities, and not all of them can necessarily be exploited. For this reason, the pen testers will perform careful vulnerability assessments of the risks they discover to determine how severe each one is and which ones they can most easily exploit.
4. Exploitation
The exploitation phase is the one in which ethical hackers try to exploit identified vulnerabilities to simulate real-world attacks and gain unauthorized access to the target system. This process mimics the tactics used by malicious actors in real-world attacks, allowing organizations to better understand their security posture. After gaining initial access, privilege escalation is often attempted to move laterally within the environment and access sensitive data.
Exploitation could be a simple or very challenging process depending on the nature of the vulnerability assessment and whether publicly available exploit code (meaning code that attackers can use to capitalize on a specific vulnerability) exists; if it doesn’t, the team will need to create its own exploits from scratch.
In many respects, the exploitation phase is the most important within the overall penetration testing process because it’s the one where the team demonstrates how real-world attacks could compromise sensitive data. Totally eradicating vulnerabilities from software systems is unrealistic in most cases, but organizations should strive to close risks that can open the door to serious attacks. By attempting to carry out exploits, pen testers highlight the vulnerabilities that matter most within a given system or environment.
5. Post-exploitation
The post-exploitation phase begins after testers have successfully gained access to the target system by exploiting a vulnerability. During this phase, they evaluate the extent to which they are able to move laterally within the exploited system by escalating their privileges or gaining access to other, adjacent resources or environments. Post-exploitation aims to determine the value of the compromised system while evaluating the attacker’s ability to maintain access for an extended time.
The insights generated by this phase are crucial because a strong security posture includes internal controls that mitigate attackers’ ability to expand the scope of attacks once they’ve breached a system’s perimeter. If a pen test reveals significant post-exploitation risks, the organization knows it has work to do to contain attackers once they’re inside systems.
6. Reporting and analysis
During the reporting and analysis phase, the penetration testing team formally assesses the results of its operations and produces a comprehensive report. This report typically includes a detailed outline of uncovered vulnerabilities, a business impact assessment, and remediation advice.
Ideally, reports will not only identify which vulnerabilities and risks the tests uncovered, but also provide recommendations on how to mitigate the issues. It’s also helpful for reports to describe what the team did not look for, and any other limitations associated with the test. Explaining which penetration testing tools they used is valuable as well.
Put together, this information allows the organization not just to manage risks, but also to hone its penetration testing strategy over time by running additional tests to fill the gaps of the initial one.
7. Clean-up and remediation
The final stage in the penetration testing process focuses on cleaning up the testing environment. The goal during this phase is for the testing team to remove all traces of its activities. This is important for ensuring that the pen testing operation doesn’t leave behind signs of an intrusion that could distract the security team. It also minimizes the risk that actual attackers carry out malicious activities by taking advantage of any active exploits created by the testing team.
Penetration testing phases in practice: A real-world example
To illustrate what a phased approach to penetration testing looks like in actual practice, consider the following scenario: A finance company has developed a new user-facing banking app. To identify potential security weaknesses in the app and defend against targeted attacks and evolving cyber threats posed by malicious actors, the company organizes a penetration testing team, which then assesses the app using the following seven-phase process:
- Pre-engagement: To begin, the team determines which types of vulnerabilities, security gaps, and potential entry points for targeted attacks it will search for in the app. It communicates its plans to stakeholders across the business and gains the approvals necessary to begin testing.
- Information gathering: The testers collect as much data as they can about how the app works. To simulate how attackers, including malicious actors, would operate, they draw only on information available externally; they avoid using any “insider” knowledge (such as information from the app’s developers) about the app’s design or functionality.
- Scanning and vulnerability assessment: Using vulnerability scanners and penetration testing tools, the testers scan the app for vulnerabilities and security gaps, then identify ones that they will seek to exploit.
- Exploitation: The ethical hackers carry out exploit attempts aimed at taking advantage of the vulnerabilities identified in the previous phase, simulating targeted attacks that real-world malicious actors might use.
- Post-exploitation: Once inside the app, the attackers seek to exfiltrate as much data as possible and move laterally into other apps and environments, mimicking the actions that could lead to a data breach.
- Reporting and analysis: The testing team assesses the operation, then generates a report that summarizes its findings, including any security gaps or vulnerabilities that could be exploited by cyber threats.
- Clean-up and remediation: The team withdraws its tools from the penetration testing environment and restores the app to its pre-testing state.
A penetration testing operation like this presents an opportunity for the finance company to find major vulnerabilities and security gaps in its app before launching it to the public, helping to prevent data breaches and mitigate cyber threats. For that matter, the organization could also employ the same types of tests to check for vulnerabilities in an app that is already in production.
Limitations of the penetration testing phase model
While a phased approach to penetration testing can help keep the process efficient and effective, it’s not without drawbacks.
A major limitation is that teams that are strongly committed to following the phases in order may struggle to go back to an earlier phase in the event that they discover new information or choose to try different tactics. In this sense, the penetration testing phases don’t do an excellent job of mimicking how real-world attackers would operate, since the latter are not bound to rigid structures. Real-world attack scenarios often do not follow the structured pen testing process or entire process outlined in phased models, as adversaries adapt and shift tactics dynamically. They can always go back and gather more information, for example, if they fail to discover major vulnerabilities on the first scan attempt.
Along similar lines, the phased model has the effect of encouraging organizations to think of cybersecurity attacks as one-time events, and to assume that once they’ve discovered and fixed vulnerabilities, they’re safe. In the real world, of course, software systems have the potential to be under attack constantly. In addition, new vulnerabilities are discovered on a continuous basis. As a result, there is by no means a guarantee that a system that has “passed” all the pen testing phases can be considered secure.
Best practices for structuring penetration testing
To reap the full benefits from a phased, structured penetration testing, consider the following best practices:
- Define phase scope clearly: It’s easy at a high level to understand what should happen during each pen testing phase. But to avoid ambiguity or inconsistency, establish clear, written descriptions of the scope and goals of every stage of the process.
- Keep phases consistent and repeatable: To ensure that different pen testers can generate similar results from penetration testing, strive to keep each stage of the process consistent, so that it can be repeated across multiple pen testing projects.
- Automate penetration tests: Although not every penetration test procedure can be automated, organizations should take advantage of automation wherever possible. Not only does automation help keep pen testing efficient, but it also increases consistency and repeatability.
- Document phases and scope: Don’t leave it to testers to remember what they did during each phase of penetration tests. Document the process thoroughly so that everyone can follow it, and to avoid being dependent on specific testers to ensure a rigid testing structure.
Penetration testing with CyCognito
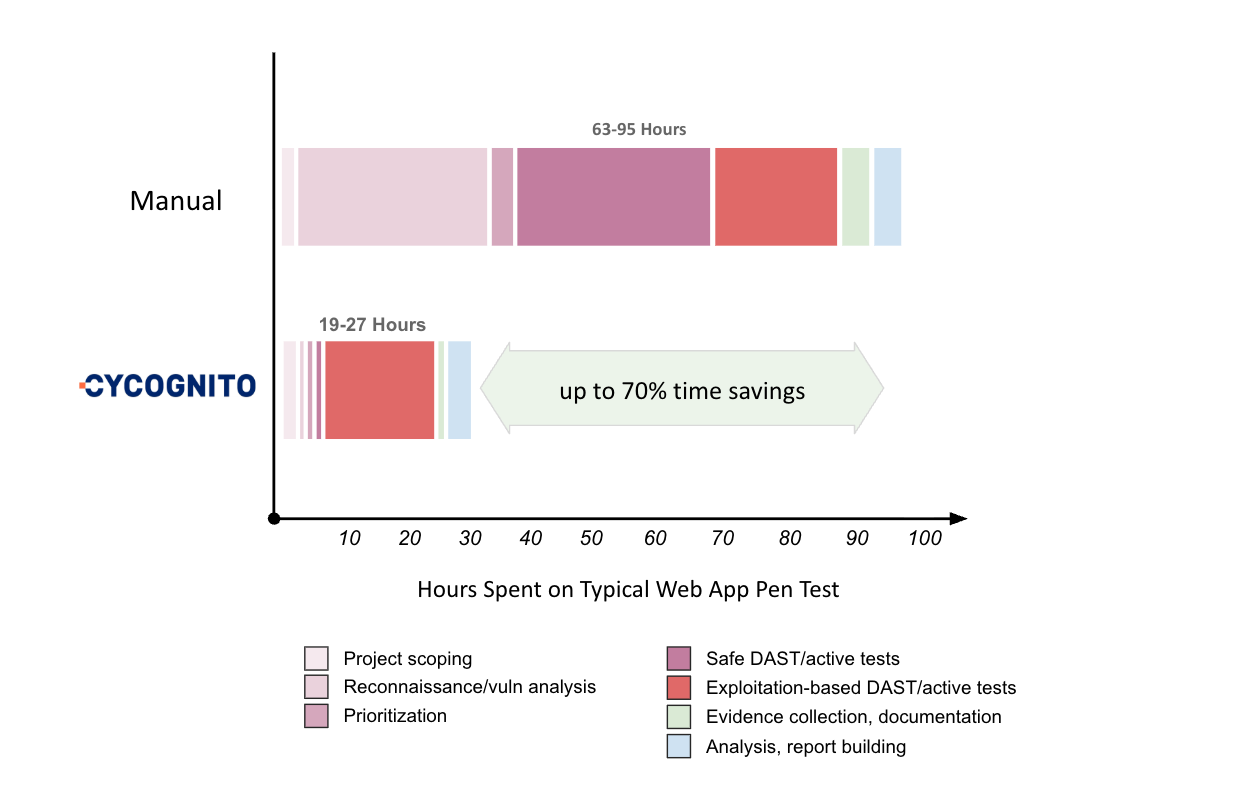
Traditional pen testing is slow, scope-bound, and frozen in time. Most of the hours go to recon, scanning, and prioritization before a tester ever attempts a real exploit.
CyCognito is a leading exposure management platform that automates those phases continuously across your entire external attack surface, so human testers spend their time on the work that actually requires human judgment.
- Automates the reconnaissance by discovering your full external footprint, including subsidiaries, shadow IT, and inherited assets, starting from nothing more than your organization’s name.
- Runs the scanning and vulnerability assessment phase continuously, with 100,000+ active tests across 35+ threat categories covering OWASP Top 10, CVEs, authentication bypass, misconfigurations, and more.
- Routes findings to asset owners with remediation guidance and verifies fix completion at the platform level, turning the reporting phase into closed-loop action.
CyCognito automates the reconnaissance, scanning, and prioritization phases , cutting engagement time by up to 70%. This frees human testers to focus on complex exploitation, logic flaws, and the business-context decisions automation cannot make.
If you want to see CyCognito in action, click here to schedule a 1:1 demo.
Frequently asked questions
What tools and techniques are used during the scanning phase?
During the scanning phase, testers use a mix of port scanners, network analyzers, and vulnerability scanners to identify open ports, examine network traffic, and fingerprint services running on the target system. Tools like Nmap, Nessus, and Burp Suite are common choices. The goal is to build a technical map of what is reachable and what is running so the team can plan the next phases.
Why is the scanning phase so important to the rest of the pen test?
Scanning is what makes deeper testing possible. A well-executed scan often surfaces misconfigurations, exposed services, and unpatched software before any exploitation attempt begins. That early visibility tells testers where the real opportunities are, and it prevents wasted effort on hardened components that aren’t likely to yield results.
What is the goal of the post-exploitation phase?
Post-exploitation is about answering two questions: how valuable is the compromised system, and how long could an attacker stay inside undetected? Testers escalate privileges, pivot to adjacent systems, and attempt to maintain access. This phase demonstrates the realistic damage a breach could cause, which is far more useful to leadership than knowing that a vulnerability exists in isolation.
What makes a penetration testing report effective?
A useful pen test report doesn’t stop at listing technical findings. It translates each issue into business-relevant language: what the risk means to operations, customers, and revenue, and what specific steps will resolve it. When reports connect technical detail to business impact, security teams get the support they need to actually fix the problems, not just file the document.














