What Is Attack Surface Reduction?
Attack surface reduction (ASR) is a proactive cybersecurity practice that minimizes an organization’s risk by identifying, monitoring, and reducing the total number of exploitable entry points, such as vulnerable software, unneeded services, and weak user permissions. It strengthens security by disabling unnecessary functions, and hardening configurations.
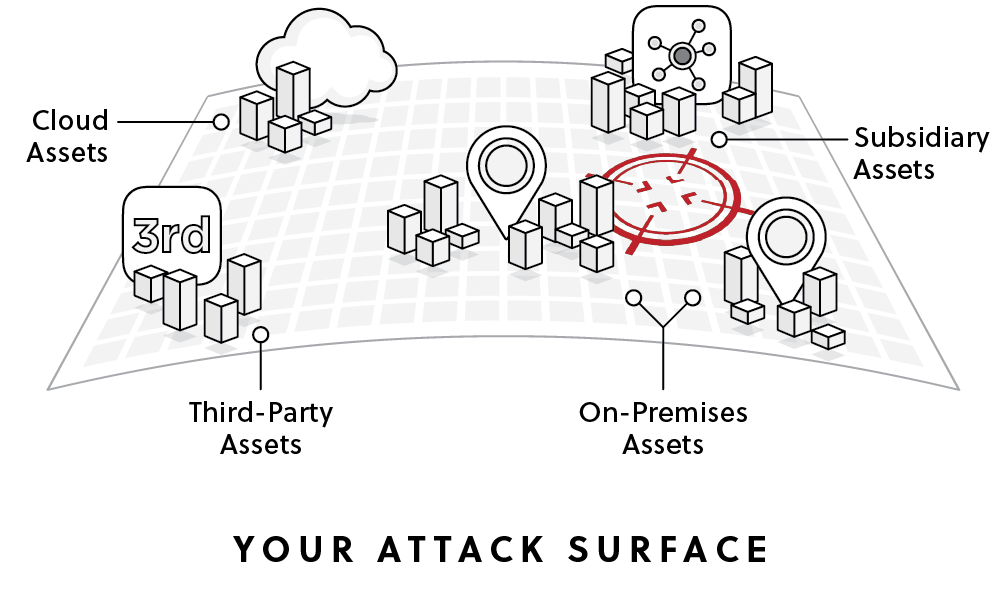
The “attack surface” addressed by ASR efforts includes all external-facing assets, exposed services, and accessible components—whether intentional (like public APIs) or accidental (like forgotten cloud storage buckets).
Attack surface reduction is a foundational strategy in modern cybersecurity, particularly for organizations with complex, hybrid, or cloud-based infrastructures. It emphasizes proactive control, allowing teams to reduce exploitable vectors before they can be leveraged by attackers.
Key Requirements for a Reduced Attack Surface
Effective attack surface reduction (ASR) depends on several core capabilities that help organizations understand and control their exposed assets. These requirements ensure security teams can see their entire attack surface, understand the risk each asset presents, and continuously monitor for new exposures.
- Comprehensive visibility: An organization must have visibility across its entire attack surface, including assets that are unknown, abandoned, or unmanaged. These overlooked systems often become easy entry points for attackers. Achieving this visibility typically requires scanning and reconnaissance across the full IT environment using an outside-in perspective, similar to how an attacker would view exposed systems.
- Business context: Security teams need to understand the importance of each asset to the business. This includes knowing what type of data the asset stores and what business processes it supports. By adding business context, teams can determine which exposures represent the greatest risk to operations or sensitive information.
- Asset attribution: Every asset should be clearly linked to an owner within the organization. Teams must know which department or group manages the asset, which IT environment it belongs to, and whether it is connected to a partner or third-party network. Clear ownership ensures that vulnerabilities can be addressed quickly and accountability is established.
- Identification and prioritization: Organizations must be able to identify potential attack paths across their exposed systems and rank them by risk. Prioritization allows security teams to focus on the vulnerabilities that present the highest likelihood of exploitation or the greatest potential impact.
- Continuous security monitoring: Attack surfaces change constantly as new services, systems, and integrations are added. Continuous monitoring ensures that new exposures are quickly detected and that the organization maintains an up-to-date view of its internal and external assets and potential attack vectors. This ongoing visibility is essential for maintaining an effective attack surface reduction strategy.
Related content: Read our guide to attack surface analysis
Tips from the Expert

Dima Potekhin, CTO and Co-Founder of CyCognito, is an expert in mass-scale data analysis and security. He is an autodidact who has been coding since the age of nine and holds four patents that include processes for large content delivery networks (CDNs) and internet-scale infrastructure.
In my experience, here are tips that can help you better operationalize attack surface reduction (ASR) programs and uncover exposures most teams miss:
- Track certificate transparency logs for shadow assets: Monitor CT logs for newly issued TLS certificates tied to your domains. Teams often discover forgotten subdomains, staging systems, or third-party services this way before attackers do.
- Use DNS entropy analysis to detect suspicious infrastructure: High-entropy or algorithmically generated subdomains can indicate temporary infrastructure, automated deployments, or attacker-controlled assets. Monitoring DNS patterns helps identify unknown assets early.
- Apply “time-to-live” policies for temporary infrastructure: Development environments, test APIs, and temporary cloud workloads should automatically expire after a defined TTL. Many attack surface issues originate from environments that were meant to be temporary but never removed.
- Continuously enumerate OAuth and API token relationships: SaaS integrations frequently create hidden access paths through OAuth grants and long-lived API tokens. Periodically audit which applications have delegated access to corporate platforms (GitHub, Google Workspace, Slack, etc.).
- Monitor certificate and domain reuse across environments: If the same certificates, domains, or wildcard DNS records are reused across staging and production, attackers can pivot through weaker environments. Separate trust boundaries and certificates between environments.
Attack Surface Reduction Technologies
Attack Surface Management (ASM) Platforms
ASM platforms are the main tools used to support attack surface reduction. It provides continuous visibility into an organization’s external-facing assets and helps security teams identify exposures that could be exploited by attackers. ASM solutions scan the internet from an outside-in perspective to discover infrastructure, domains, cloud resources, APIs, and services that belong to the organization.
Unlike traditional asset inventories, attack surface management focuses on what is actually reachable and visible to attackers. It continuously maps these assets, identifies misconfigurations or vulnerabilities, and highlights exposures that increase risk. This allows teams to quickly reduce their attack surface by removing unnecessary assets, securing exposed services, or correcting unsafe configurations.
Modern ASM platforms typically include several core capabilities:
- Continuous discovery: ASM continuously scans the internet to identify new or previously unknown assets associated with the organization. This includes shadow IT, forgotten subdomains, exposed cloud resources, and newly deployed services. Continuous discovery ensures the asset inventory stays current as environments change.
- Exploit validation: ASM platforms analyze discovered vulnerabilities and exposures to determine whether they are realistically exploitable. By combining vulnerability intelligence, exposure context, and attacker techniques, ASM helps teams focus on issues that present real attack paths rather than theoretical weaknesses.
- Owner-linked mobilization: Effective remediation requires clear ownership. ASM solutions map assets to business units, teams, or service owners and route findings directly to the responsible group. This shortens remediation time and ensures that exposures are addressed by the people who manage the affected systems.
Conceptually, more and more ASM offerings align themselves with the Continuous Threat Exposure Management (CTEM) framework, in which attack surface reduction becomes an ongoing motion.
Network Security
Firewalls, intrusion prevention systems (IPS), and network segmentation technologies help enforce boundaries and reduce unnecessary exposure. By controlling traffic flow and restricting communication between different network zones, organizations can isolate critical assets and limit lateral movement.
Network access control (NAC) can enforce policies based on device posture and identity, ensuring that only compliant and authorized systems can access specific segments. Additionally, microsegmentation within virtualized and cloud environments adds fine-grained control over communication paths, further reducing the network attack surface.
Vulnerability Scanners
Vulnerability scanners identify known weaknesses across systems, applications, and infrastructure components. By correlating these vulnerabilities with asset exposure data, teams can prioritize patching efforts based on actual risk.
Scanners can assess both internal and external attack surfaces, including open ports, outdated software versions, insecure configurations, and missing patches. Integrated vulnerability management platforms often link scanner results with threat intelligence and exploit likelihood, helping teams focus on exposures most likely to be targeted.
Endpoint and Host Hardening
Endpoint protection platforms (EPP), endpoint detection and response (EDR), and system hardening baselines work together to reduce attack vectors at the host level. Controls include disabling unnecessary services, enforcing strong authentication, applying secure configurations, and restricting user privileges.
Technologies like Microsoft Defender’s attack surface reduction rules or application control mechanisms (e.g., AppLocker, Windows Defender Application Control) prevent execution of unauthorized code. System hardening standards, such as CIS Benchmarks or DISA STIGs, provide prescriptive guidance for minimizing host-level vulnerabilities.

Operationalizing CTEM Through External Exposure Management
CTEM breaks when it turns into vulnerability chasing. Too many issues, weak proof, and constant escalation…
This whitepaper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.

Best Practices for Reducing the Attack Surface
Here are some of the security measures that organizations can use to improve their attack surface reduction (ASR) strategy.
Identify and Map All Assets and Entry Points
A complete inventory of digital assets is central to attack surface reduction. Organizations must identify all internet-exposed systems, services, domains, APIs, and cloud instances, as well as assets such as development environments, third-party integrations, and remote access points. This includes managed and unmanaged assets across subsidiaries, cloud accounts, and business units.
Mapping relationships and data flows between assets helps uncover potential attack paths. Automated discovery tools and continuous asset monitoring help maintain an up-to-date view of the environment.
Validate Risk and Exploitability
Not all exposed assets represent equal risk. Once the attack surface is mapped, organizations must assess which components are most likely to be exploited. This involves evaluating known vulnerabilities, misconfigurations, exposed credentials, and weak authentication mechanisms. Publicly available exploit code, vulnerability severity (e.g., CVSS scores), and asset criticality should all factor into this assessment.
Prioritize remediation based on exploitability, not just exposure. Tools like attack path analysis, threat modeling, and penetration testing help validate whether an attacker could realistically compromise a system. This validation step is key to focusing limited resources on the highest-impact risks.
Eliminate Unnecessary or Unused Services
Every exposed service or application expands the attack surface. Systems should be reviewed regularly to identify and disable non-essential components, open ports, default accounts, legacy protocols, or test environments no longer in use.
This process should be part of change management and decommissioning workflows to ensure services are not left running unintentionally. Removing unused services reduces exposure and the number of systems that require patching and maintenance.
Enforce Strong Access Controls and Authentication
Access to critical systems and data must be tightly controlled. Implement least privilege by granting users and systems only the access they need to perform their functions. Use role-based access control (RBAC) to simplify administration and limit scope.
Multi-factor authentication (MFA) should be enforced for remote access, privileged accounts, and cloud services. Where possible, enforce strong authentication for APIs and service-to-service communications. Misconfigured identity and access controls are common attack vectors, so periodic access reviews are necessary.
Secure Cloud, APIs, and External-Facing Services with Configuration Management Tools
Cloud environments and public APIs often introduce complex exposures. Misconfigured storage buckets, overly permissive security groups, and exposed development APIs are common sources of breaches. Use cloud security posture management (CSPM) tools to audit configurations and enforce security baselines.
APIs should require authentication, enforce rate limiting, and avoid exposing sensitive data. Web-facing applications must be kept up to date and protected by web application firewalls (WAFs) and secure development practices. Regular testing, such as dynamic application security testing (DAST), helps uncover vulnerabilities in these components.
Introduce Security Hygiene Best Practices
Maintaining basic security hygiene significantly reduces attack surface exposure. Systems must be kept up to date with security patches, particularly for internet-facing services. Automated patch management and vulnerability scanning help identify outdated components and accelerate remediation.
Disable default credentials, enforce strong password policies, and ensure encryption is used for data in transit and at rest. Secure configuration baselines should be applied consistently using infrastructure-as-code templates or configuration management tools. Regular audits and adherence to security benchmarks (e.g., CIS benchmarks) help enforce hygiene across environments.
Ensure Continuous Monitoring and Risk Assessment
Attack surfaces are dynamic. Assets are added, configurations change, and new vulnerabilities emerge. Continuous monitoring is required to detect changes in exposure, such as newly opened ports, expiring certificates, or outdated components.
Combine external attack surface monitoring with internal threat detection and vulnerability management. Risk scoring and prioritization should drive remediation workflows. By integrating monitoring data into SIEMs or security orchestration tools, teams can respond quickly and reduce time to mitigation.
Attack Surface Reduction with CyCognito
Attack surface reduction minimizes exposed assets and hardens configurations to limit entry points. But most programs rely on periodic scans and incomplete inventories, which miss unknown assets and don’t confirm real exploitability. This leaves gaps between perceived and actual exposure.
CyCognito complements attack surface reduction practices by adding continuous external discovery and active exploitability validation. If you already use ASM platforms, vulnerability scanners, and CSPM tools, CyCognito strengthens your program by:
- Discovering unknown internet-facing assets using a 60,000+ node global discovery network without manual input
- Validating exploitability through always-on testing across 90,000+ tests, including authentication bypass and data exposure
- Continuously re-testing assets and controls to detect new exposures and verify fixes
- Prioritizing issues using attack-path logic and business context, mapped to asset owners
This shifts ASR from periodic visibility to continuous, validated exposure. Teams can focus on what is actually exploitable, not just what is visible.
If you want to see CyCognito in action,click here to schedule a 1:1 demo.















