What Is CTEM?
Continuous Threat Exposure Management (CTEM) is a structured, iterative approach to identifying, validating, prioritizing, and reducing an organization’s exposure to cyber threats. Rather than relying on periodic scans or static assessments, CTEM operates as a continuous cycle that reflects how environments and attacker behavior change over time. It integrates asset discovery, exposure assessment, validation, and remediation into a single workflow focused on real, exploitable risk.
CTEM shifts security programs away from volume-based vulnerability management toward outcome-driven risk reduction. It emphasizes understanding how exposures can be chained together, whether they can actually be exploited, and what impact they would have on critical assets. By aligning technical findings with business context and attacker behavior, CTEM enables organizations to focus remediation efforts on the smallest set of actions that meaningfully reduce risk.

Operationalizing CTEM Through External Exposure Management
CTEM breaks when it turns into vulnerability chasing. Too many issues, weak proof, and constant escalation…
This whitepaper offers a practical starting point for operationalizing CTEM, covering what to measure, where to start, and what “good” looks like across the core steps.

What Vendor Categories Enable a CTEM Program?
Attack Surface Management
Attack Surface Management (ASM) solutions form the foundation of a CTEM program by enabling continuous discovery and visibility across the entire attack surface. This includes external (EASM) and internal (CAASM) assets such as cloud workloads, SaaS applications, identities, APIs, and unmanaged devices.
Gartner emphasizes that CTEM begins with discovery, which requires organizations to maintain an accurate, real-time inventory of all assets and their exposures—not just known systems, but also shadow IT and third-party dependencies.
ASM tools continuously map this expanding environment from an attacker’s perspective, identifying:
- Unknown or unmanaged assets
- Misconfigurations and exposed services
- Weak identity and access controls
- Third-party exposure risks
By doing so, ASM establishes the scope and visibility layer required for all downstream CTEM activities, ensuring organizations understand what can be attacked before trying to secure it.
Security Validation
Security validation technologies align with CTEM’s validation phase, where organizations move beyond theoretical risk to determine whether exposures are actually exploitable in real-world conditions.
Gartner formalized this space through the Adversarial Exposure Validation (AEV) category, which combines:
- Breach and Attack Simulation (BAS)
- Automated penetration testing
- Red teaming and adversary emulation
These tools simulate attacker behavior to:
- Test if vulnerabilities can be exploited in the current environment
- Identify gaps in security controls (e.g., missing EDR, weak segmentation)
- Validate detection and response capabilities
This phase is critical because CTEM is designed to reduce real exposure, not theoretical risk. Validation provides evidence-based prioritization, ensuring remediation efforts are focused only on exposures that can actually lead to compromise.
Threat Intelligence
Threat intelligence enhances CTEM by adding external context about the threat landscape, enabling organizations to align their exposure management efforts with real-world attacker activity.
Threat intelligence answers these key questions:
- Is this vulnerability being actively exploited in the wild?
- Are there known exploit kits or ransomware campaigns targeting it?
- Which threat actors are relevant to our industry or geography?
Within CTEM, threat intelligence feeds directly into prioritization and validation, enriching exposure data with:
- Exploit availability and weaponization status
- Indicators of compromise (IOCs)
- Tactics, techniques, and procedures (TTPs)
- Industry-specific threat targeting
Gartner’s broader Threat Exposure Management (TEM) concept emphasizes integrating threat intelligence to ensure that exposure management is aligned with current attacker behavior, not just internal findings.
This allows organizations to prioritize exposures that are most likely to be exploited now, rather than those that are merely severe on paper.
Remediation Orchestration
Remediation orchestration supports CTEM’s mobilization phase, which focuses on turning insights into coordinated, measurable action across the organization.
Gartner highlights that remediation cannot be fully automated—it requires cross-functional collaboration between security, IT, DevOps, and business stakeholders.
Remediation orchestration platforms enable this by:
- Integrating with ticketing systems (e.g., Jira, ServiceNow)
- Automating workflows and task assignment
- Tracking remediation progress and SLAs
- Providing prioritization-driven remediation guidance
These tools reduce friction in the remediation lifecycle and ensure that validated, high-risk exposures are:
- Assigned to the right teams
- Fixed in a timely manner
- Verified and closed
Ultimately, they operationalize CTEM by transforming insights into consistent, repeatable remediation processes.
What Platform Capabilities Should You Look For?
Gartner’s CTEM framework outlines several critical platform capabilities that facilitate a successful CTEM program. In many cases, organizations combine multiple tools to achieve all these capabilities.
Continuous Asset Discovery and Inventory
A CTEM platform must continuously discover and maintain an up-to-date inventory of assets across the entire environment. This includes internal systems, external-facing assets, cloud resources, identities, and third-party dependencies.
Modern exposure management relies on continuous visibility rather than periodic scanning. Attack surface management and exposure assessment capabilities work together to identify both known and previously unknown assets, including unmanaged or shadow IT.
This inventory is not just a list of assets. It must include business and security context such as ownership, criticality, and dependencies. This context allows teams to understand which assets matter most and ensures that exposure prioritization reflects real business impact rather than just technical severity.
Continuous Exploitability Validation
Continuous exploitability validation ensures that identified exposures are tested to determine whether they can actually be exploited in the current environment.
Adversarial exposure validation (AEV) technologies provide automated and repeatable validation by simulating real-world attack scenarios. These tools combine techniques such as attack simulation, penetration testing, and red teaming to demonstrate whether exposures can bypass existing controls.
This capability is critical because CTEM focuses on real risk, not theoretical findings. Validation provides evidence of attack feasibility, helping organizations confirm which exposures are truly dangerous and require immediate action.
Attack-Path and Blast-Radius Mapping
Attack-path mapping models how an attacker could move through an environment to reach critical assets. It connects individual exposures into realistic attack scenarios rather than treating them as isolated issues.
This capability creates a representation of assets and their relationships, highlighting likely paths attackers could use for lateral movement. It allows security teams to identify “stepping stone” assets that may appear low risk in isolation but are critical in an attack chain.
Blast-radius analysis builds on this by estimating the potential impact of a successful attack. It shows how far an attacker could propagate and what systems, identities, or data could be affected. This helps quantify business impact and supports better prioritization and communication with stakeholders.
Threat Intelligence and Adversary Context Enrichment
Threat intelligence enriches exposure data with external context about attacker behavior, campaigns, and targeting patterns.
Within exposure management architectures, threat context is a key input into prioritization. It includes exploit availability, active attack campaigns, targeted industries, and adversary tactics and techniques.
By integrating this intelligence, organizations can focus on exposures that are actively being exploited or are likely to be targeted. This shifts prioritization from static severity scores to dynamic, threat-informed decision-making aligned with the current threat landscape.
Beyond-CVSS Risk Scoring
Traditional severity scoring models such as CVSS are insufficient for CTEM because they do not reflect real-world risk.
Modern platforms apply contextual risk scoring that combines multiple factors, including exploit likelihood, asset criticality, compensating controls, and business impact. This requires aggregating and normalizing data from multiple sources, then applying analytics to produce a more accurate risk score.
Advanced approaches may also incorporate predictive models and threat intelligence to estimate the probability of exploitation. The result is a prioritized view of exposures that reflects actual risk to the organization, not just theoretical severity.
Remediation Orchestration and Workflow Automation
Remediation orchestration capabilities translate CTEM insights into coordinated action across teams.
These platforms integrate with IT service management systems and automate workflows such as task assignment, prioritization, and tracking. They ensure that exposure findings are routed to the correct owners and progress is monitored through structured processes.
Automation plays a key role in reducing delays, but it is used to support, not replace, cross-functional collaboration. Effective orchestration standardizes remediation intake, enforces accountability, and accelerates resolution through predefined workflows and integration with existing tools.
Program Analytics, Continuous Monitoring, and Integrations
A CTEM platform must provide continuous monitoring and analytics to track exposure risk over time and measure program effectiveness.
This requires integrating data from multiple sources, including vulnerability assessment tools, attack surface management, threat intelligence, and security controls, into a consolidated view. Aggregation, normalization, and correlation of this data enable consistent analysis and reporting.
Program analytics should focus on measurable outcomes such as risk reduction, remediation velocity, and exposure trends. Continuous monitoring ensures that changes in the environment, threat landscape, or asset inventory are reflected in near real time, enabling the CTEM cycle to operate as an ongoing, iterative process rather than a point-in-time assessment.
Tips from the Expert

Dima Potekhin, CTO and Co-Founder of CyCognito, is an expert in mass-scale data analysis and security. He is an autodidact who has been coding since the age of nine and holds four patents that include processes for large content delivery networks (CDNs) and internet-scale infrastructure.
In my experience, here are tips that can help you better evaluate and operationalize CTEM platforms:
- Start with attack-chain compression, not finding volume: Look for vendors that can collapse hundreds of related findings into one remediable attack chain. The best platforms reduce noise by showing the smallest set of fixes that breaks the most paths to critical assets.
- Score fixes by risk-reduction yield: Do not just prioritize the “most critical” exposure. Measure which single action removes the most downstream attacker options, such as disabling a stale admin path, fixing a trust relationship, or removing a public route to a sensitive workload.
- Validate exposures against control drift: A finding is more urgent when a compensating control silently stopped working. Ask whether the platform can detect drift in EDR coverage, segmentation rules, MFA enforcement, WAF policies, and service account restrictions before re-scoring exposure.
- Treat identity as the fastest-moving attack surface: Most CTEM programs still over-index on CVEs. Favor tools that model ephemeral privilege, token abuse, federation trust, excessive SaaS grants, machine identities, and dormant accounts because attackers often pivot through identity faster than infrastructure.
- Build a crown-jewel reverse map: Instead of mapping outward from every asset, map backward from your most sensitive systems, data stores, and identity providers. This exposes the true stepping stones attackers need and makes scoping much more precise for mobilization.
Notable CTEM Vendors
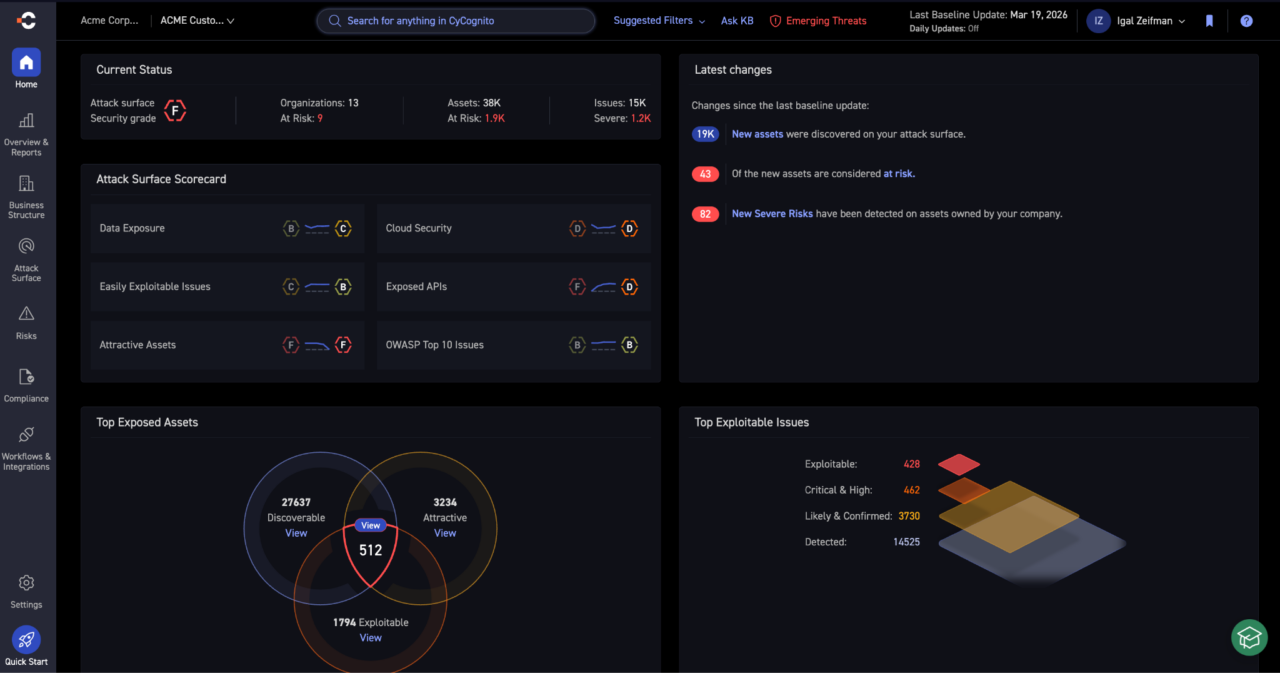
1. CyCognito

CyCognito is an external exposure management platform that runs every stage of the CTEM cycle — scoping, discovery, prioritization, validation, and mobilization — against the internet-facing attack surface.
The platform takes the attacker’s perspective. It maps an organization’s full external footprint without seeds or agents, then actively tests every discovered asset for exploitability rather than inferring risk from software versions.
Key features include:
- Black-box discovery: Continuously discovers and maps internet-facing assets across the enterprise, including unknown and inherited infrastructure
- Business-aligned scoping: Aligns coverage to business units, subsidiaries, and critical functions
- Active security testing: Tests every discovered asset with 100,000+ payload-based modules across 30+ exposure categories (OWASP weaknesses, authentication bypass, data exposures)
- Application and control validation: Includes DAST and security control validation across web applications, APIs, and exposed services
- Attack path validation: Maps how external exposures chain together and, through integrations, traces paths from internet-facing assets to internal crown jewels
- Risk-based prioritization: Combines business context, exploitability evidence, and threat intelligence, going beyond CVEs and CVSS
- Remediation orchestration: Attributes findings to owners and integrates with ITSM tools to track remediation through closure
Pros:
- Outside-in discovery of unknown and inherited assets
- Active testing across all exposures, with pentesting-like depth
- Risk-based prioritization beyond CVEs
Cons:
- Internal exposure data sourced via integrations
- AD and identity graph less developed than peers
- Black-box testing only; no static or instrumented coverage
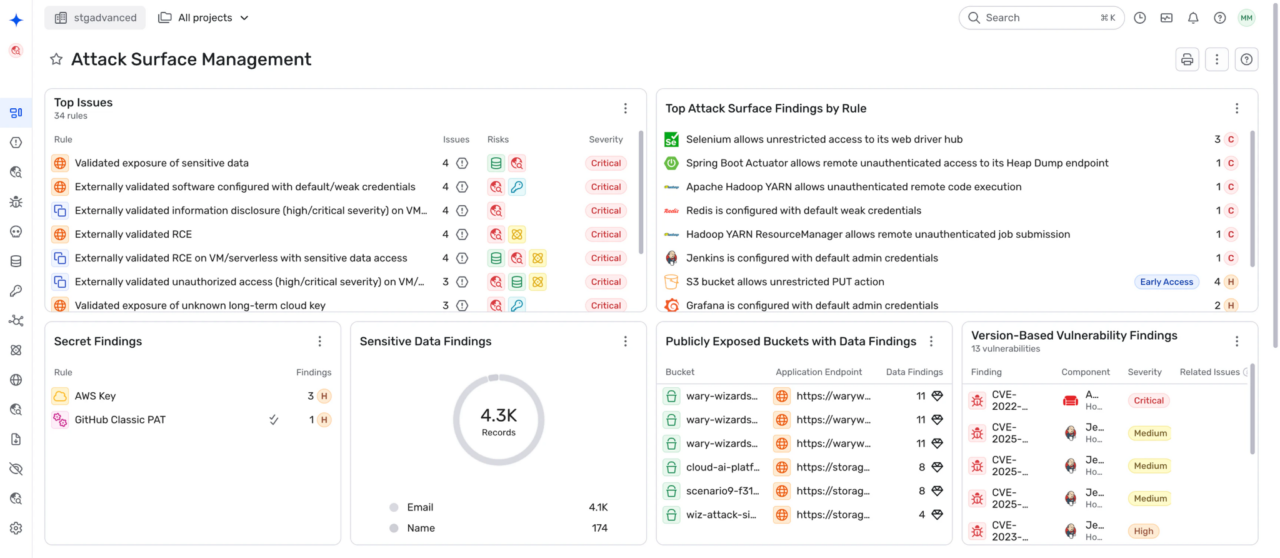
2. Wiz

Wiz is a unified exposure management platform that aggregates and correlates risk signals across cloud, code, and on-prem environments. It focuses on connecting fragmented findings into a single contextual view, enriched with business and security metadata. By combining asset discovery, attack surface mapping, and exploitability analysis, Wiz helps organizations prioritize exposures based on real-world risk and assign ownership for remediation across teams.
Key features include:
- Cloud asset discovery: Identifies assets across environments using native scanners and external integrations, enriched with business context
- Exploitability-focused detection: Evaluates vulnerabilities, misconfigurations, and exposures to determine what can be realistically exploited
- Context-driven prioritization: Correlates and deduplicates alerts using a security graph to highlight high-impact risks
- Attack path analysis: Connects exposures into attack paths to show how risks can be chained to reach critical assets
- Ownership and accountability mapping: Identifies resource owners and assigns remediation tasks directly within workflows
- Integrated remediation workflows: Supports remediation with AI-assisted guidance and integrations to accelerate response
Pros:
- Agentless, API-based coverage across AWS, Azure, and GCP
- Security Graph maps cloud risk into attack paths
- Code-to-cloud context ties findings back to IaC
Cons:
- Coverage anchored in the cloud
- Validation focused on cloud workloads, not the broader internet
- External discovery depends on cloud API access
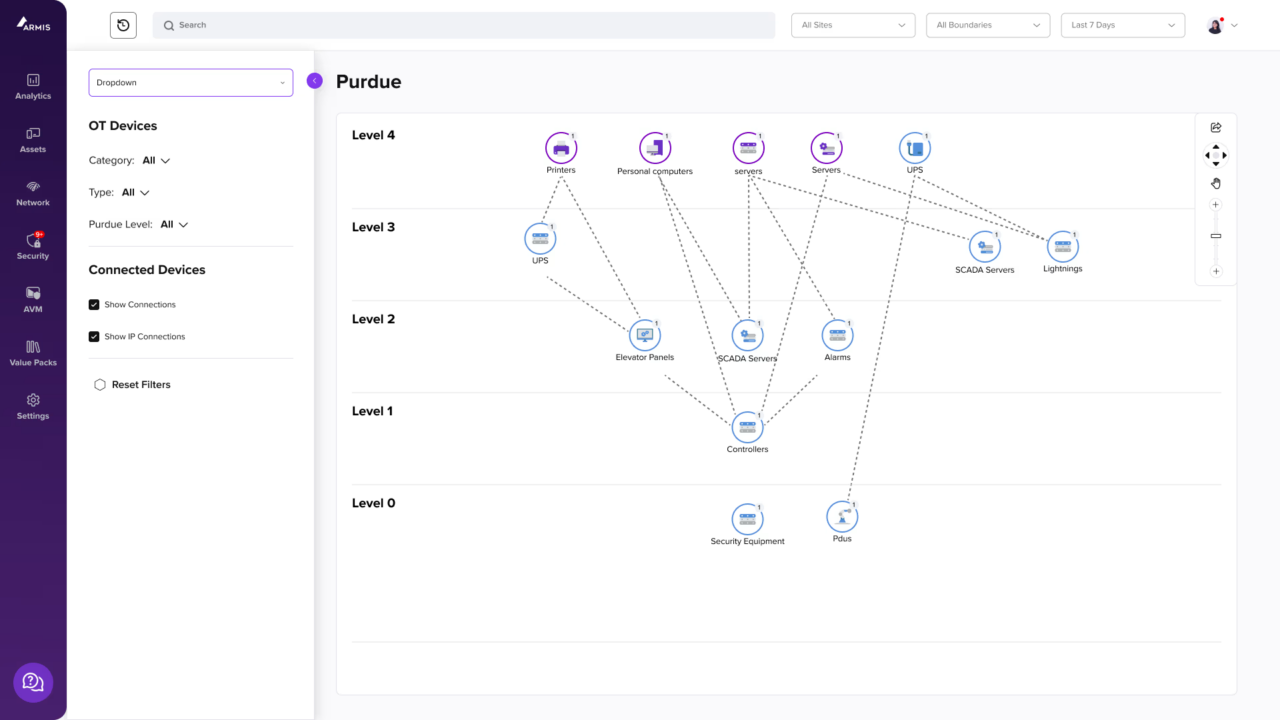
3. Armis

Armis provides a cyber exposure management platform focused on achieving complete asset visibility and prioritizing risks based on real-world context. It continuously discovers and classifies assets across hybrid environments, including unmanaged and shadow assets, and enriches them with behavioral and risk-based insights.
Key features include:
- Full asset visibility: Discovers and classifies all assets across on-prem and cloud environments, including unmanaged devices
- Contextual asset intelligence: Enriches assets with behavioral, risk, and business impact data for better decision-making
- Risk-based prioritization: Uses AI-driven scoring and threat intelligence to focus on exploitable and relevant vulnerabilities
- Anomaly and threat detection: Identifies abnormal behavior, policy violations, and active exploit patterns in real time
- Integrated threat intelligence: Incorporates external threat data to highlight actively weaponized vulnerabilities
- Remediation workflow orchestration: Automates assignment and tracking of remediation tasks across teams
- Ecosystem integrations: Connects with SIEM, SOAR, EDR, ITSM, and CMDB tools to enable closed-loop response
Pros:
- Agentless discovery of internal connected assets
- Purpose-built for converged and cyber-physical environments
- Low network impact suits sensitive OT and medical networks
Cons:
- Coverage limited to network-connected assets
- Exploitability is inferred, not tested
- Attack-path modeling is shallow
4. Cymulate
Cymulate improves continuous threat exposure management (CTEM) by integrating exposure discovery with automated threat validation, enabling organizations to focus on exploitable risks rather than theoretical ones. Its platform empowers security, red, and vulnerability management teams to work together, using offensive testing to validate exposures and improve threat resilience.
Key features include:
- Threat validation through continuous testing: Automates the validation of exposures using attack simulations powered by AI, helping organizations confirm which threats are actually exploitable in their environment.
- Integrated exposure discovery: Aggregates asset and vulnerability data from existing scanners and discovery tools to create a unified view of the threat landscape.
- Prioritization based on proven risk: Correlates discovered exposures with results from offensive testing to focus remediation on validated, high-impact threats.
- Threat resilience optimization: Enhances defenses by generating custom detection rules, triggering automated security control updates, and delivering actionable remediation plans.
- Business context scoping: Allows organizations to define testing scope based on asset importance (such as endpoints, applications, and data) ensuring CTEM efforts align with business priorities.
Pros:
- BAS across email, web, endpoint, and network
- No-code attack scenario builder
- Validates controls against known techniques
Cons:
- Discovery and prioritization depend on other tools
- Attack-path modeling is scenario-based
- Coverage anchored to control validation

5. Picus Security
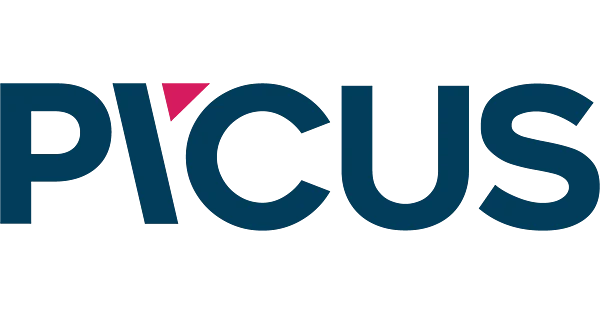
Picus Security enables organizations to implement and operationalize the full CTEM lifecycle with adversarial exposure validation. Its platform combines broad attack surface discovery, dynamic risk prioritization, and real-world exploitability validation to help security teams focus on exposures that truly matter. Picus goes beyond traditional vulnerability analysis by integrating with existing security tools and validating risks through simulated attacks.
Key features include:
- Flexible CTEM scoping: Supports validation across on-premises, cloud, and hybrid environments, allowing teams to tailor the CTEM scope from focused assessments to enterprise-wide programs.
- Comprehensive exposure discovery: Identifies known and unknown assets, integrating with vulnerability scanners and attack surface management tools to detect CVEs, misconfigurations, and insecure services. Highlights potential attack paths to critical assets.
- Contextual risk prioritization: Adjusts risk levels dynamically by factoring in exploitability, attack complexity, and the business value of affected assets, helping teams focus on high-impact exposures.
- Adversarial exposure validation: Uses techniques like breach and attack simulation (BAS) and automated penetration testing (APT) to confirm real-world exploitability and test existing defenses.
- Actionable remediation and reporting: Provides reports with vendor-specific detection and prevention recommendations, integrates with ticketing systems for workflow automation, and re-validates fixes to confirm risk reduction.
Pros:
- BAS, pentesting, and validation in one platform
- Vendor-specific mitigation signatures
- 24-hour SLA for new threat content
Cons:
- Discovery relies on integrating other tools’ data
- Exploitability tested via simulation, not on live external assets
- Narrow scope outside validation use cases
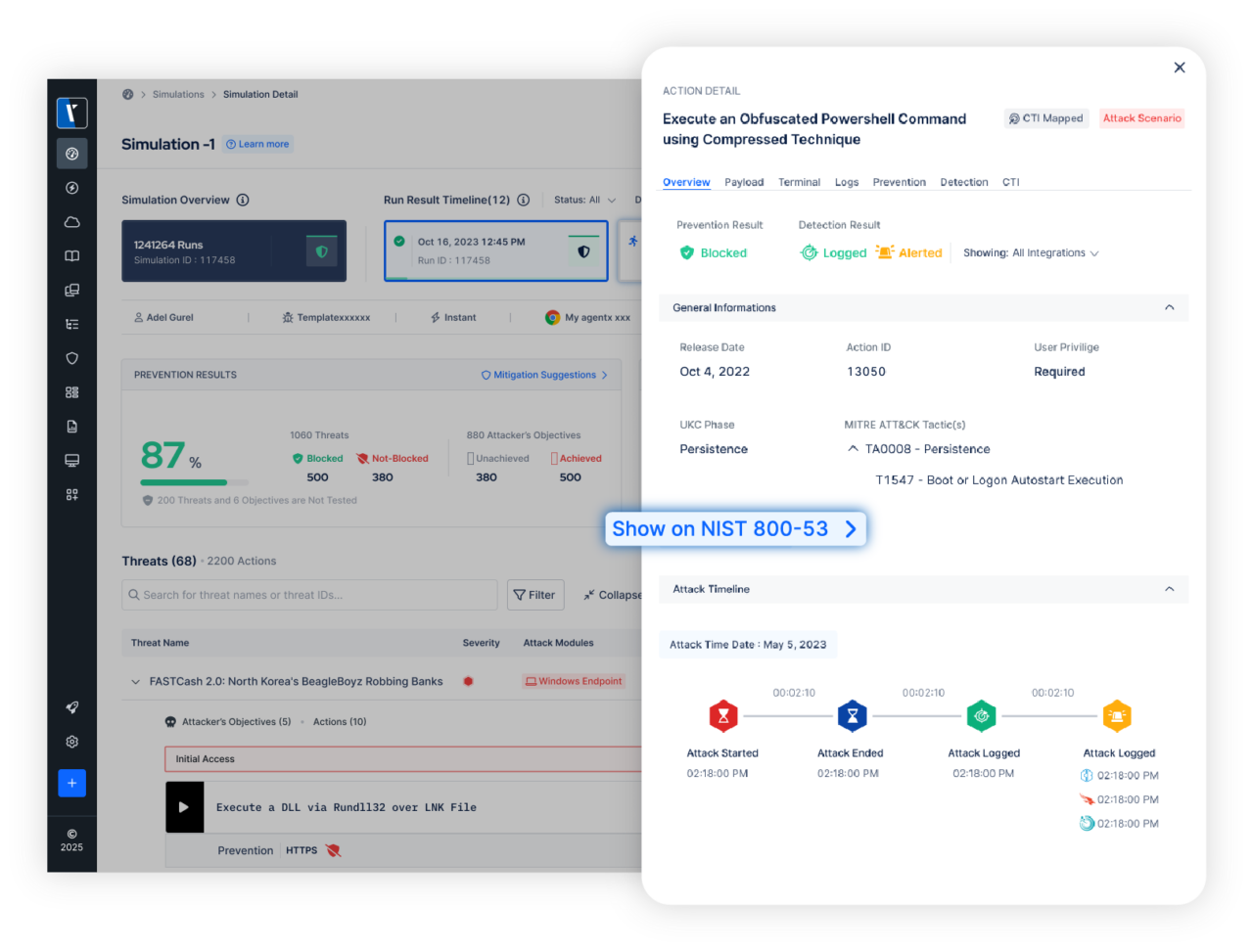
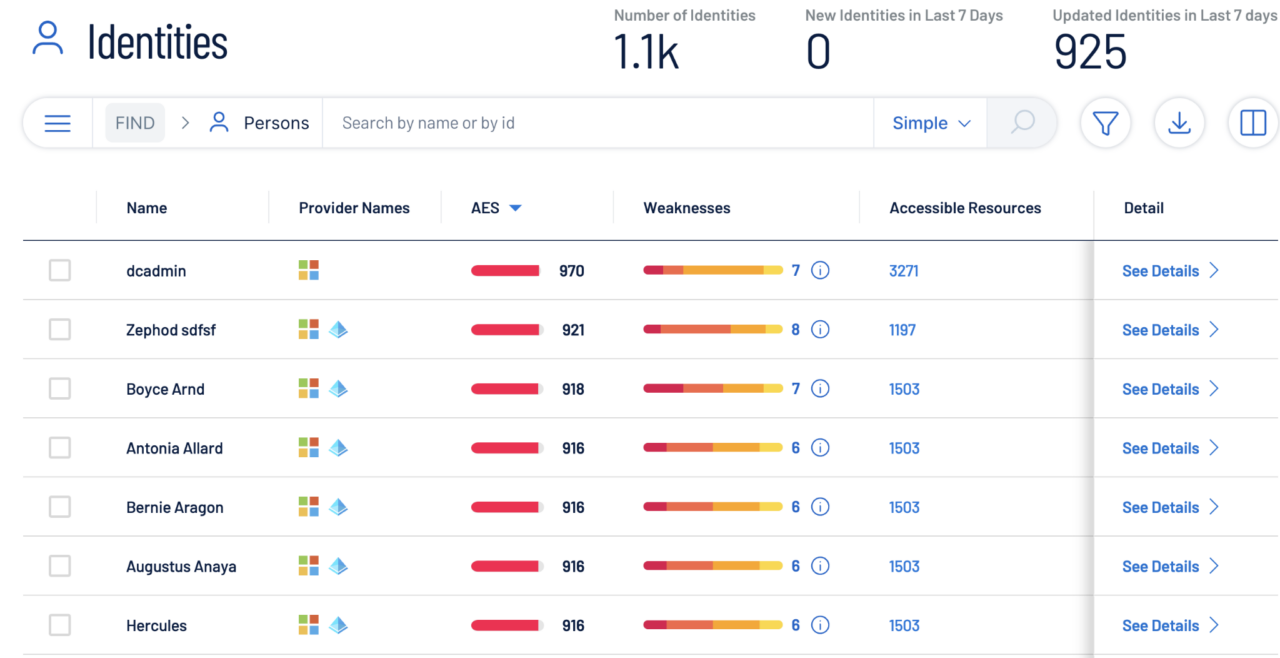
6. XM Cyber

XM Cyber offers an end-to-end continuous threat exposure management platform to help organizations identify, prioritize, and remediate exposures that lead to real risk. Its approach focuses on understanding how attackers can exploit interconnected exposures to reach critical assets, rather than treating vulnerabilities in isolation.
Key features include:
- Holistic exposure discovery: Identifies exposures such as CVEs, misconfigurations, over-privileges, credentials, behavioral risks, and control weaknesses across hybrid and multi-cloud environments using both agentless and agent-based methods.
- Context-based prioritization: Leverages asset labeling and custom scenarios to prioritize exposures based on their potential impact on business-critical assets, ensuring focus on what matters most.
- Attack graph analysis: Uses the proprietary XM Attack Graph Analysis™ to model how attackers can move laterally and chain exposures, revealing choke points where remediation yields the greatest risk reduction.
- Factual exploitability validation: Filters out theoretical risks by verifying which exposures are truly exploitable in the given environment, reducing noise and false positives.
- Detailed remediation guidance: Offers actionable remediation instructions, including alternatives for non-patchable issues, integrated with IT workflows through ticketing and messaging tools.
Pros:
- Attack graph maps exposure chains
- Strong on AD and identity risk
- Identifies choke points for remediation
Cons:
- Focus is internal attack paths
- Limited visibility into unmanaged external infrastructure
- Fit narrows outside hybrid AD estates
7. Tenable

Tenable delivers an exposure management platform that unifies visibility, prioritization, and remediation across attack surfaces. Its approach centers on aggregating data from multiple security tools into a shared data fabric, enriched with technical and business context. This enables organizations to understand true exposure, prioritize based on likely attack paths, and communicate risk effectively across stakeholders.
Key features include:
- Unified exposure data fabric: Consolidates data from disparate security tools into a centralized platform
- Comprehensive attack surface visibility: Covers IT assets, cloud resources, applications, containers, and identity systems
- Contextual risk prioritization: Combines technical findings with business context to identify high-risk exposures
- AI-assisted analysis: Uses analytics to accelerate decision-making and highlight the most impactful actions
- Exposure mapping: Visualizes vulnerabilities, misconfigurations, and access issues across the attack surface
- Cross-team risk communication: Enables consistent reporting of cyber risk to technical and business stakeholders
Pros:
- Scanner coverage across IT, OT, IoT, identity
- VPR scoring beyond CVSS
- Ingests third-party findings
Cons:
- Rooted in vulnerability management
- Exploitability inferred, not tested
- EASM is a secondary capability
8. Qualys

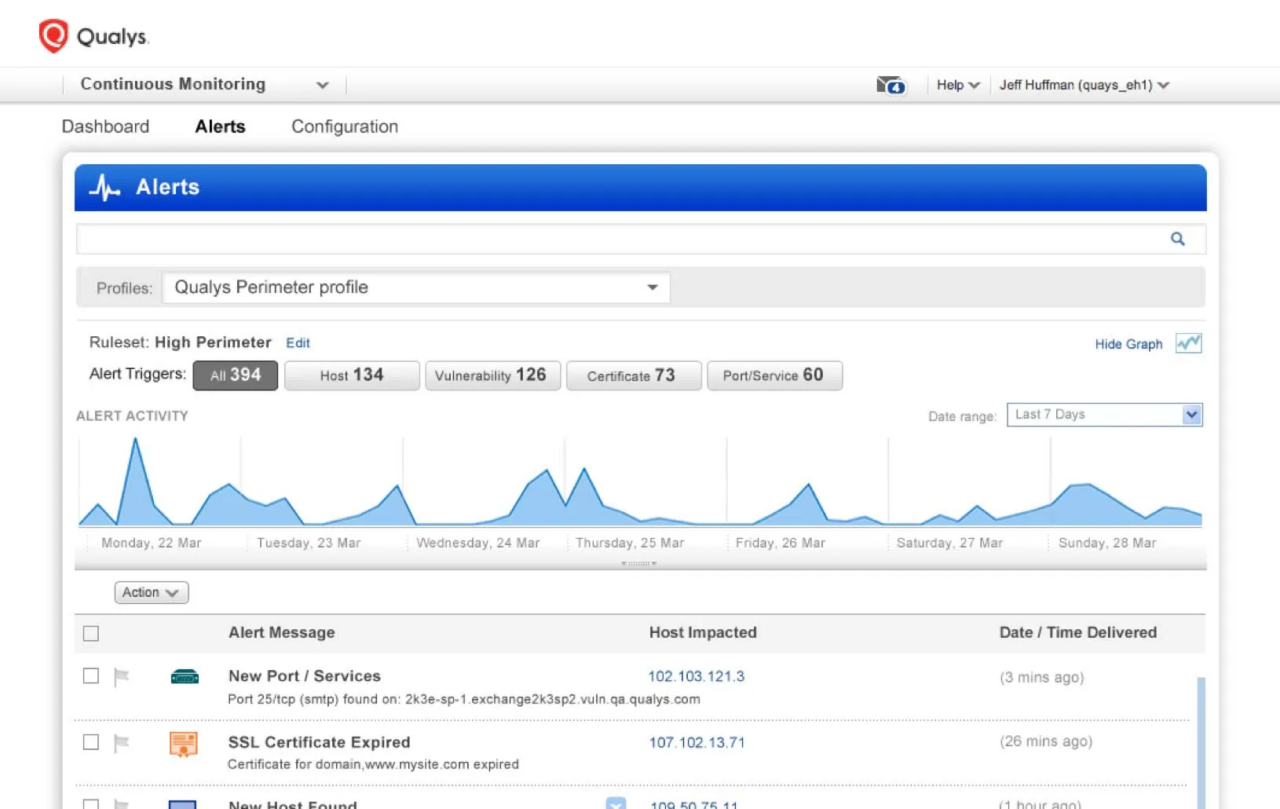
Qualys provides a unified CTEM platform through its Enterprise TruRisk Management (ETM) solution, which integrates asset discovery, risk prioritization, validation, and remediation into a continuous workflow. It aggregates data from multiple sources and applies business context and AI-driven analysis to prioritize exposures. The platform emphasizes continuous visibility and validation of exploitability to ensure that remediation efforts target meaningful risks.
Key features include:
- Unified asset and identity inventory: Consolidates asset and identity data across on-prem, cloud, and third-party sources
- Continuous exposure visibility: Aggregates and normalizes risk signals to maintain real-time awareness of the attack surface
- TruRisk scoring: Prioritizes exposures based on business impact, threat context, and likelihood of exploitation
- Exploitability validation: Confirms whether vulnerabilities are actually exploitable in production environments
- Integrated threat intelligence: Enriches exposure data with real-time threat insights and industry benchmarking
- Attack surface mapping: Connects exposures into attack paths to highlight critical risk scenarios
- AI-driven automation: Uses AI to automate prioritization, analysis, and remediation workflows across the CTEM lifecycle
Pros:
- Risk scoring with environmental context
- Ingests third-party signals
- Alternative mitigations for unpatchable issues
Cons:
- Rooted in vulnerability management
- Exploitability inferred, not tested
- Attack-path modeling is shallow
Conclusion
A CTEM program requires continuous visibility, validation, and prioritization of exposures across an evolving attack surface. Organizations must move beyond static assessments and adopt iterative processes that reflect real-world exploitability and business impact. By integrating discovery, validation, threat context, and remediation into a unified workflow, security teams can focus on reducing actual risk rather than managing large volumes of theoretical findings.














