



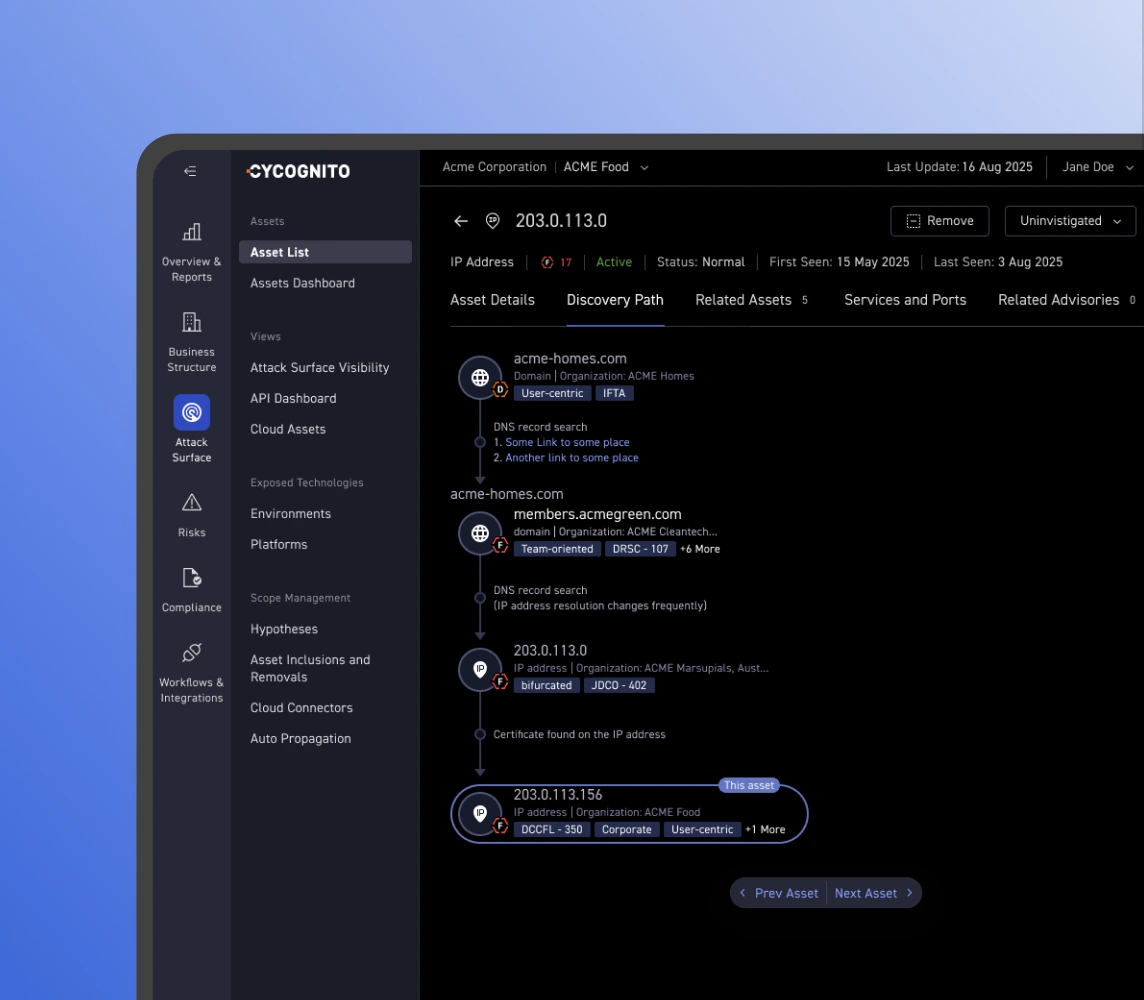
CyCognito maps in-the-wild threat activity to your external exposures. The result: a risk queue grounded in what attackers are actually doing, specific to your attack surface.
Get the demo
Trusted by leading global enterprises.










































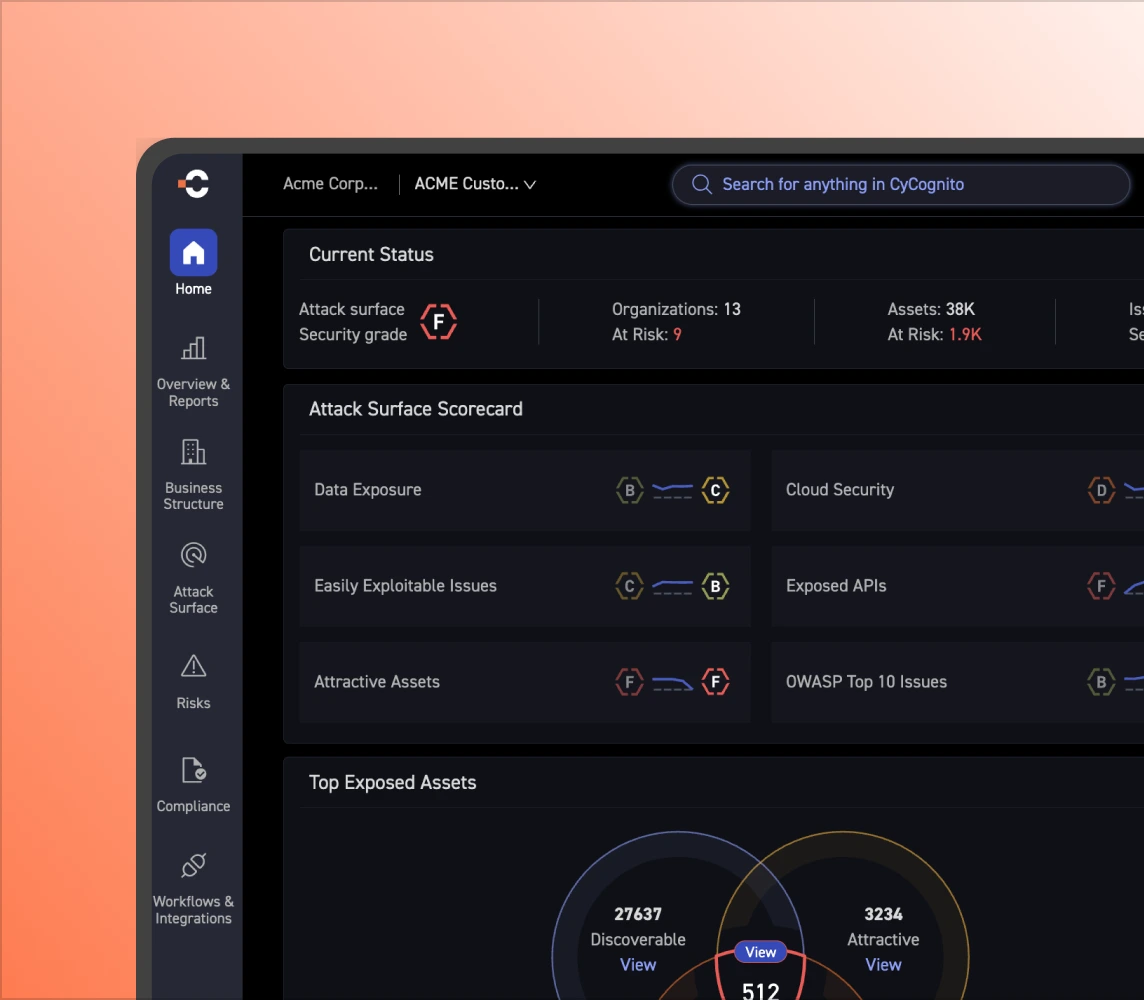
CyCognito cross-references active exploit validation findings with its proprietary attractiveness and discoverability risk model. The output is a tightly focused risk queue that shows where risk accumulates.
CyCognito links real attacker campaigns and MITRE ATT&CK TTPs to your external attack surface. Your risk queue reflects what is being exploited right now.
CyCognito runs 100,000+ active tests across 35+ threat categories. Exploit kits let your team verify every finding independently and confirm that remediation
More about adversarial validation
CyCognito became a cornerstone of our security set-up by solving multiple pain points with automatic detection of assets, continuously analyzing for vulnerabilities, and by providing an easy-to-use and comprehensive platform to manage these issues.
 Berlitz
Stefan Romberg ・ Global CISO
Berlitz
Stefan Romberg ・ Global CISO
When a critical CVE drops, CyCognito automatically maps it to your assets. Your team knows which assets are protected and which need remediation.

CyCognito collects first-party attacker data and enriches it with threat intelligence insights (e.g., MITRE ATT&CK). Both are linked directly to your external exposures, so remediation reflects bad actor behavior, not theoretical severity.
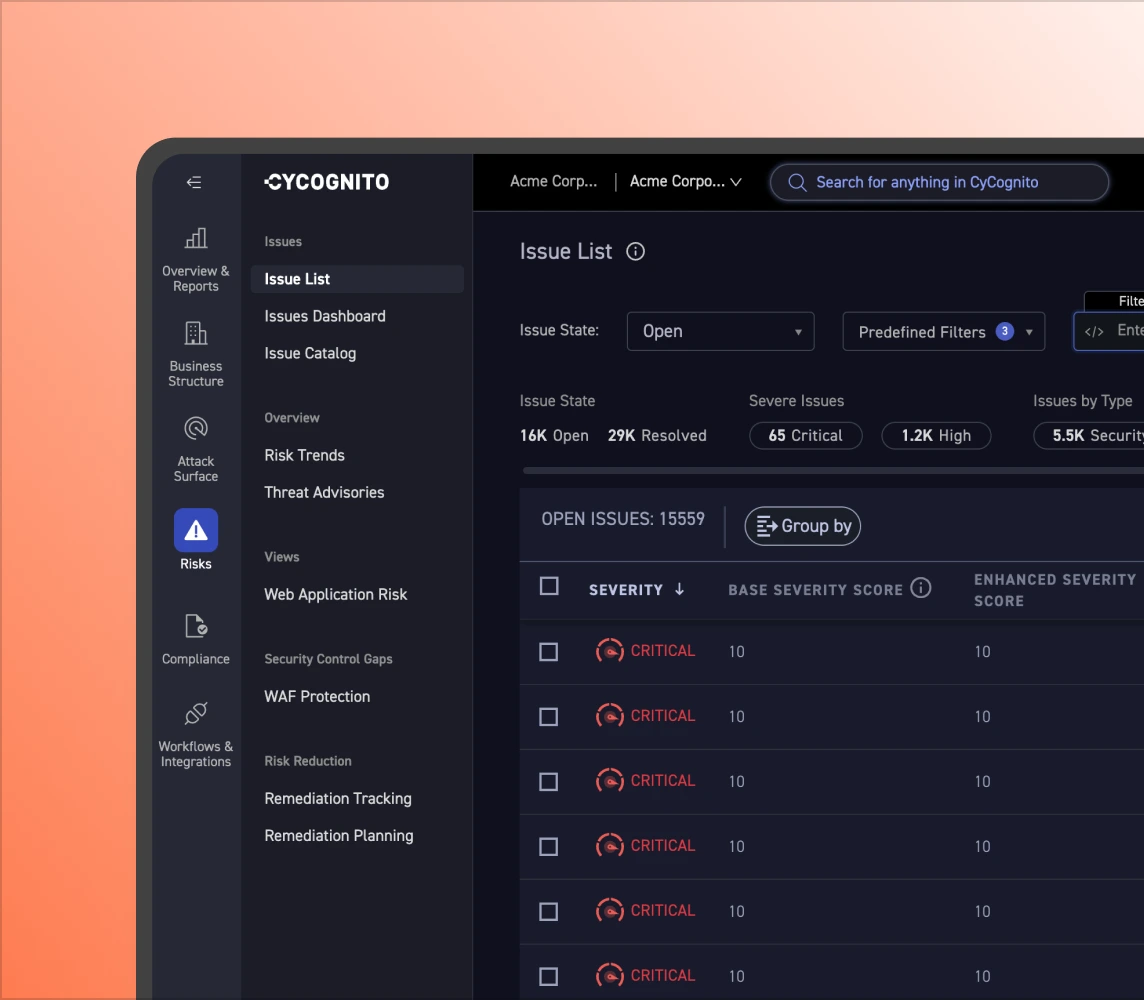
Not every CVE deserves a war room. CyCognito's active validation accounts for your deployed controls to confirm what is genuinely exploitable in your environment.
Exploit Intelligence feeds directly into CyCognito’s prioritization engine. Threat activity, confirmed exploitability, and business context are combined so your team focuses on the risks that matter most.