Stop by and learn how you can create an EASM exposure management program built for scale that focuses your team’s attention on the most critical vulnerabilities that are known to be exploitable. The CyCognito platform makes it easy to know you are focused on the right risks, and helps you to find and remediate the paths of least resistance most vulnerable to threat actors.
Come visit us at booth 455 for information and enter our raffle for a chance to win an exclusive bottle of whiskey.
Schedule a meeting to stop by and connect with one of our experts. Let’s discuss your team’s external attack surface management needs and provide you with the right tools and resources to kick-start your external attack surface management project.
Book a meeting in advance to meet with CyCognito’s executive team at the Gaylord. Speak 1:1 with our CEO and co-Founder, Rob N. Gurzeev, or our CSO, Anne Marie Zettlemoyer, and gain insight into how you can start the journey to ruling your risk!
Engage with the Co-founder and CEO of CyCognito as he explores the top five prerequisites for successfully controlling external risk. As organizations adapt to the structural changes imposed by digital transformation, they find it difficult to identify, classify, and test all of their internet-facing assets, leading to significant risk from external attack.
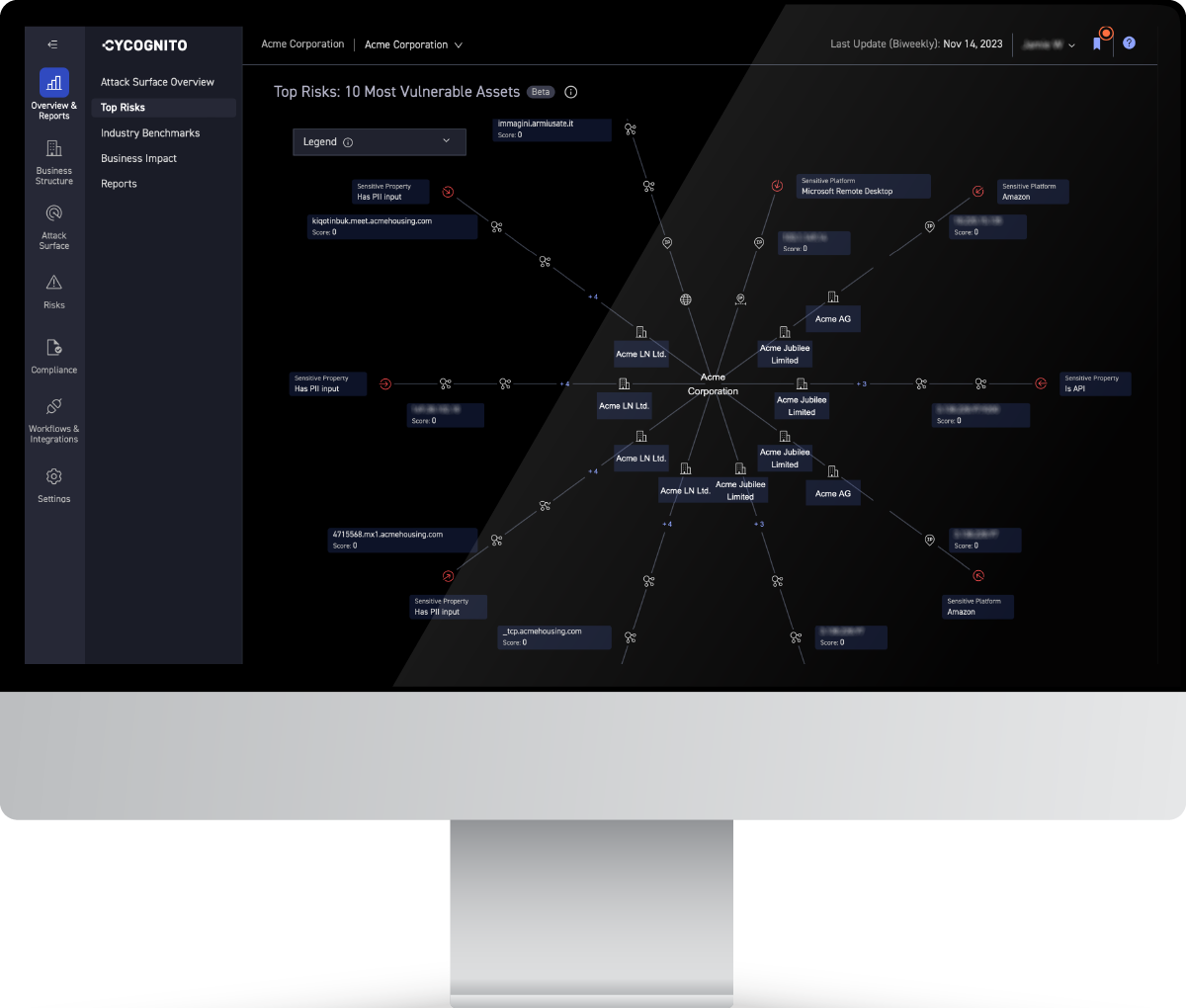
Deploying an external attack surface management program helps organizations discover all their IT assets exposed to the internet, identify each asset's business context, continuously test for vulnerabilities, prioritize the most critical risks, and accelerate mean-time-to-remediation. Launching an EASM program blocks the path of least resistance that can be exploited by threat actors.
Request a personalized walkthrough of the CyCognito platform to see how we can help your company identify all its internet-exposed assets, focus on which are most vulnerable to attacks, and accelerate your time to remediating critical risks.