



CyCognito combines validated findings, business context, and threat intelligence to surface the small set of external risks most likely to impact the business.
Get a Demo

Cut through VM and alert noise. Aligning real exploit data with business impact surfaces the small set of issues worth fixing first.

Continuous active testing keeps your risk profile current. New exposures are validated as threats evolve and your environment changes.

Attack surface classification, business context, testing data, and attacker activity are combined. Together they focus attention fast on the most critical risks.

There are thousands of threats out there, even an army of security staff can't address them all. CyCognito helps us focus our efforts on what's critical.
 Human API
Megan Bell ・ Chief Privacy and Security Officer
Human API
Megan Bell ・ Chief Privacy and Security Officer

Security teams should spend time on the handful of issues that drive the most risk. CyCognito narrows attention to the exposures that matter, so teams stop manually correlating noisy queues.
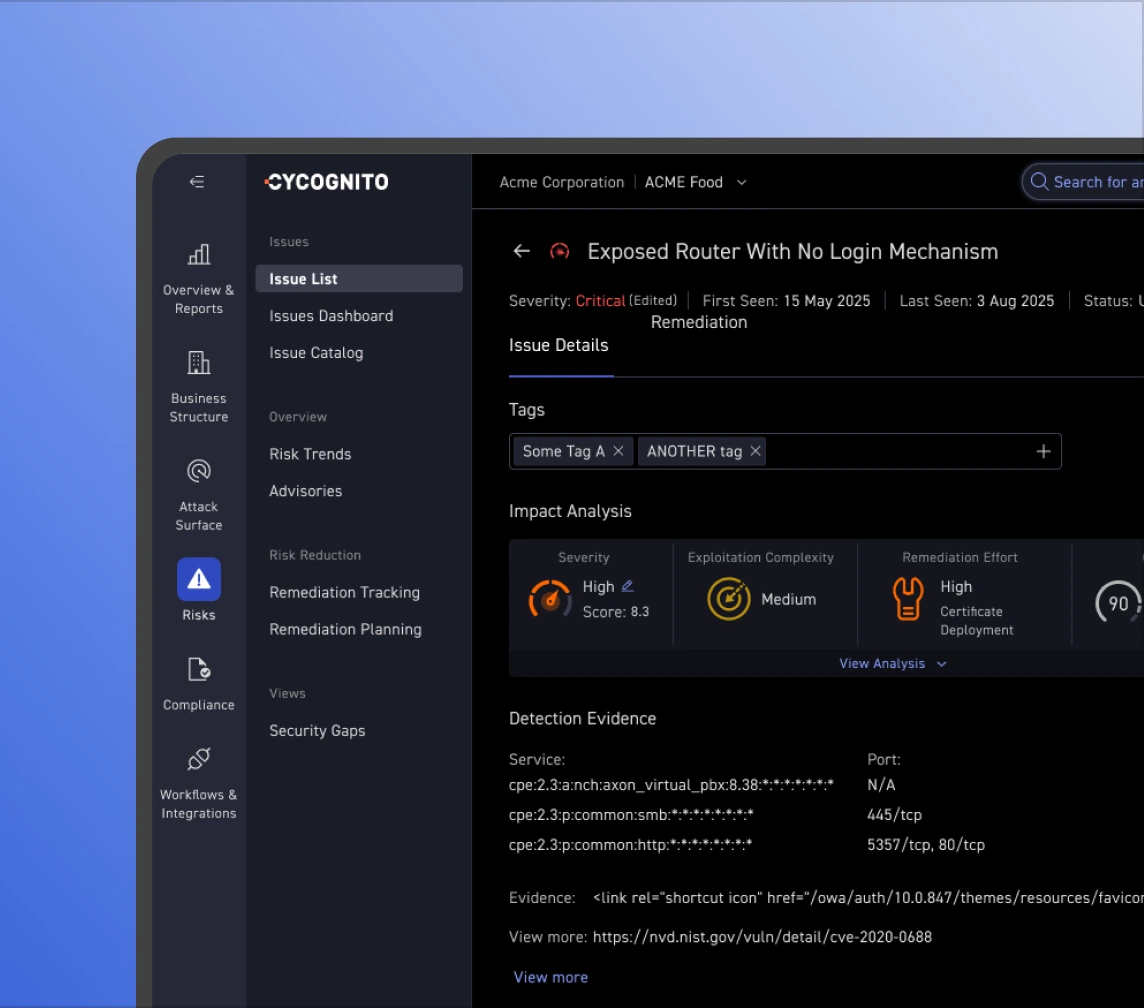
CyCognito weighs validated findings, asset classification, exploit intelligence, attractiveness, discoverability, and business context to rank what is truly urgent, not just what scores highest.

Risk is not static. Regular scanning and validation keep priorities aligned with new exposures, attacker behavior, and changes across the business, so teams are never working from a stale list.