By now I’m sure that most everyone has heard of the Microsoft Exchange vulnerabilities, and hopefully addressed them in their systems. Still, it's definitely worth looking at what these vulnerabilities and the age of the systems they were on says about the temporal complexity of today’s attack surface.
It’s easy to get caught up in the shiny, newness of the technology landscapes we create during this age of digital transformation. So this zero-day is a great reminder that while newness is certainly important—we also need to keep looking for those aging systems that may be tried-and-true, but need to be upgraded or replaced before they are forgotten paths of least resistance. And if they cannot be upgraded and replaced, put them behind a firewall or VPN gateway and supply some good agent-based monitoring or network intrusion prevention, or closely watched logging for anomaly detection. When old systems start doing new tricks it is probably not good.
What’s Old Is New Again
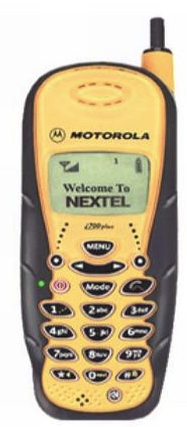
What first got me thinking this way was the fact that ever since October 2003 I’ve had a reminder in my calendar for the second Tuesday of every month. I recall setting it up in Lotus Notes, which was the collaboration software of choice back then with 46% of the market. I don’t even think my cell phone at the time was capable of telling me about this event, or if it was I hadn’t set that up, because that phone clipped on my belt looked like the one to the right.

I was reminded of this old technology and the long upgrade journey I’ve been on since then when my Patch Tuesday reminder chimed this week on my soon-to be-upgraded March 2018 Samsung Galaxy S9 after Microsoft sent an out-of-band notification to its vast user base of a set of critical vulnerabilities on Tuesday, March 2nd, a week earlier. This reminder traveled through time from past Jim to future Jim through at least a dozen laptops and at least as many phones with who-knows-how-many hours of updates transmitted via wires and wireless, and on so many different operating systems, to get to me today. Like deja vu, what’s old is new again.
Microsoft Exchange Vulns: Old Technology Impacts the Present
The latest vulnerabilities, CVE-2021-26855, CVE-2021-26857, CVE-2021-26858 and CVE-2021-27065, are all Remote Code Execution Vulnerabilities that allow an authenticated (or trusted) attacker with access to a 2010, 2013, 2016, or 2019 Exchange (MSE) server to write a file to any path on the server. It’s important to note that 2010 MSE support ended on October 13, 2020. We can estimate that this unknown “zero-day” has been around since MSE 2010 was released on November 9, 2009, so if we look at the days since then, these are actually T-minus-4131-day vulnerabilities and counting
According to plenty of reporting on this subject, exploitation of the flaws was first noticed at the beginning of January, and since that time the traffic has increased by orders of magnitude. A sophisticated group of attackers out of China dubbed Hafnium initially used these vulnerabilities, but now it’s a free-for-all as other groups attempt to grab MSE real-estate and launch further attacks from these persistent, sometimes mission-critical beachheads.
What is also pretty amazing about this activity is how quickly it moved from unknown to automatically breached. Over a matter of days the number of potential victims went from 30,000 to 60,000 or more, and organizations are still scrambling just to identify the targets in their attack surface to protect them, all while the malicious actors leverage automated scanners and scripts to easily find and exploit targets.



