While tech sector media coverage on cybersecurity has primarily focused in recent years on trends such as ransomware attacks, vulnerabilities in the DevOps chain, and the growing role of AI in combating threats, a quiet but significant development has been advancing under the radar on several fronts: we refer to the more assertive stance taken by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) to elevate security best practices in government and the private sector.
Understanding CISA’s Binding Operational Directive (BOD) 22-01
On November 3, 2021, the CISA, a federal agency under the U.S. Department of Homeland Security, introduced the Known Exploited Vulnerabilities Catalog, a continuously updated database of exploited Common Vulnerabilities and Exposures (CVEs). Under the CISA’s Binding Operational Directive (BOD) 22-01, all Federal Civilian Executive Branch (FCEB) agencies were mandated to consult the database to identify and remediate listed vulnerabilities within a certain timeframe. While mandatory only for FCEB agencies, organizations in the private sector were also strongly encouraged to download the catalog and use it to compare against their own internal security measures as a means of reducing risk. With 287 entries when first released, the catalog has been updated continuously at a cadence based on threat activity, often multiple times per month. As of late 2023, the catalog stood at well over 1,000 entries and growing.
But the CISA didn’t stop there. In October 2022, the CISA published BOD 23-01, a directive aimed at advancing measurable progress toward enhancing visibility into agency assets and associated vulnerabilities. Again, while aimed primarily at addressing visibility challenges at the component, agency, and FCEB enterprise level, BOD 23-01 has implications for strengthening the security posture of organizations across any number of private sector verticals. The directive focuses on two core activities essential to improving operational visibility for a successful cybersecurity program: asset discovery and vulnerability enumeration.
Asset Discovery and Vulnerability Enumeration
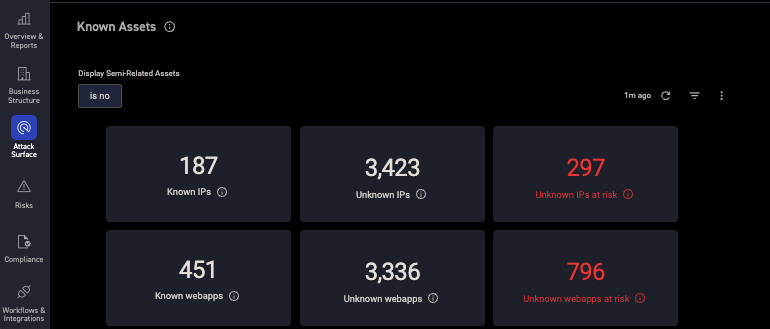
Asset Discovery is a building block of operational visibility, and it is defined as an activity through which an organization identifies what network addressable IP-assets reside on their networks and identifies the associated IP addresses (hosts). Asset discovery is non-intrusive and usually does not require special logical access privileges.
Vulnerability Enumeration identifies and reports suspected vulnerabilities on those assets. It detects host attributes (e.g., operating systems, applications, open ports, etc.) and attempts to identify outdated software versions, missing updates, and misconfigurations. The vulnerability enumeration process validates compliance with or deviations from security policies by identifying host attributes and matching them with information on known vulnerabilities. Understanding an asset’s vulnerability posture is dependent on having appropriate privileges, which can be achieved through credentialed network-based scans or a client installed on the host endpoint.
It should be pointed out that asset visibility is not an end in itself, for BOD 23-01, but is necessary for updates, configuration management, and other security and lifecycle management activities that significantly reduce cybersecurity risk. This holds true for exigent activities like vulnerability remediation as well. At its core, the goal of the directive is for agencies to comprehensively achieve the following outcomes without prescribing exactly how to do so:
- Maintain an up-to-date inventory of networked assets as defined in the scope of the directive.
- Identify software vulnerabilities using privileged or client-based means where technically feasible.
- Track how often the agency enumerates its assets, what coverage of its assets it achieves, and how current its vulnerability signatures are.
- Provide asset and vulnerability information to CISA’s CDM Federal Dashboard.
Capitalizing on the CISA Directives: How CyCognito Can Help Your Organization Build on Asset Discovery and Vulnerability Enumeration
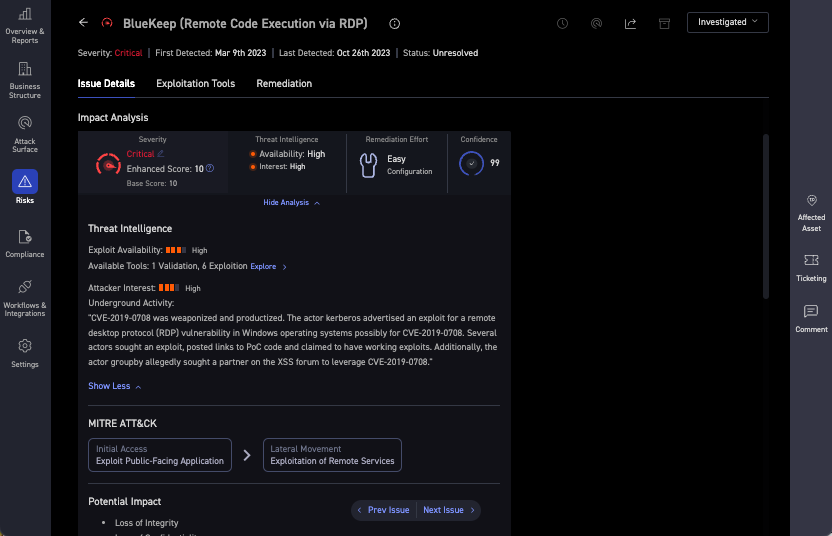
For more than a year now, CyCognito has operationalized the CISA known exploited vulnerability catalog within its platform. Data from the catalog is used during assessment and prioritization phases to understand asset risk and assign urgency to issues. The CISA known exploitable vulnerability catalog is the latest of many intelligence sources used by CyCognito to develop asset risk scores, including those from NSA, MITRE, FBI and CISA. For example, MITRE ATT&CK Tactics and Techniques are often displayed as part of CyCognito Exploit Intelligence to assist in communicating how adversaries may use a particular exploitable vulnerability, in this case, initial access and lateral movement. You can read more about that integration in this blog post.
How CyCognito Automates Asset Discovery
The CyCognito platform has been adopted by leading companies in financial services, media and publishing, consumer packaged goods, healthcare, and many other sectors precisely because it enables comprehensive asset discovery for attack surface assessment. In fact, automated, zero-input asset discovery and attribution is the foundation of CyCognito’s external attack surface management system. With CyCognito, it becomes possible to discover and contextualize your entire internet-exposed attack surface in line with the BOD 23-01 directive.
The first thing CyCognito does is use machine learning and natural language processing to automatically map your organization—including all subsidiaries and their assets. In this way, it becomes possible to understand your attack surface from the perspective of a malicious attacker. CyCognito uses that context and evidence to chart your attack surface and understand the attacker’s path of least resistance. By mapping out a discovery path, the CyCognito platform shows the hierarchy of the discovered organizations along with attribution context for you to understand what ties them together. Evidence of each relationship is provided via links, making it easy to understand and document each asset, with pages showing what each asset does and how it could give attackers a foothold into the organization.
Enumerating Vulnerabilities to Defend Against Threats
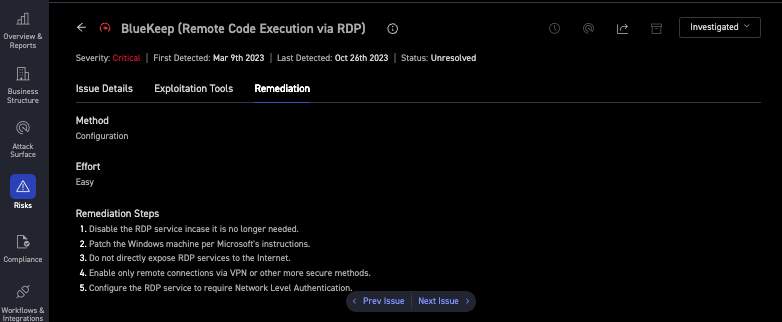
The CyCognito platform also addresses today’s vulnerability management requirements in line with the BOD 23-01 directive. Built on the foundation of full discovery of your entire extended IT ecosystem, the CyCognito platform helps you to proactively defend against threats from even the most sophisticated attackers. It operates continuously and autonomously using advanced reconnaissance techniques to identify attackers’ paths of least resistance into your environment so that you can efficiently eliminate them. Once it identifies potential attack vectors, it prioritizes risks and delivers both actionable remediation guidance and ongoing validation of fixes. The result is a platform that delivers risk-based vulnerability management for your entire attacker-exposed IT ecosystem, closing what is a significant gap in existing attack surface management and vulnerability management processes.
The CyCognito platform uniquely delivers:
- The essential foundation of vulnerability management: full discovery of your extended IT ecosystem, including assets that are part of your IT ecosystem but are unknown or unmanaged by you.
- Detection and testing of attack vectors across your entire attacker-exposed IT ecosystem, going well beyond CVEs to include data exposures, misconfigurations, and even software zero-day vulnerabilities.
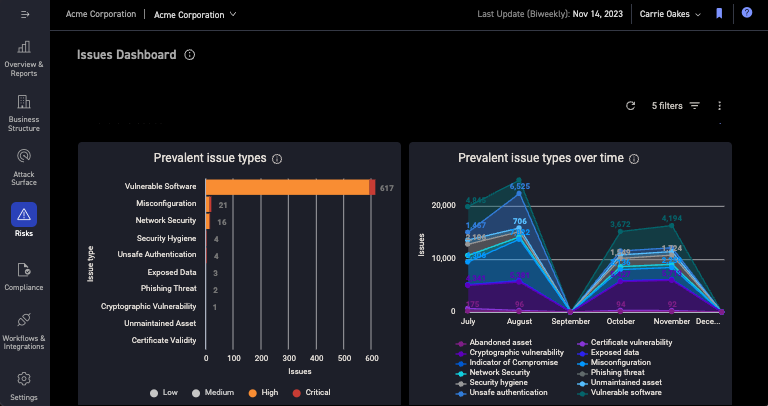
- Prioritization of the attack vectors in your IT ecosystem based on what could impact your organization most from a cybersecurity risk perspective.
- Actionable remediation guidance and reporting to accelerate your remediation and validation.
By taking an attacker-oriented approach to vulnerability management, security teams using the CyCognito platform can automatically discover and understand the business context for every asset within the organization. With vulnerabilities prioritized in this way, teams can mitigate threats and concentrate remediation actions where they’re most needed.


